Old laptops, servers, and hard drives collecting dust in a storage closet aren't just clutter—they're ticking time bombs, potential data breaches waiting to happen. That's where secure destruction of data comes in. It’s the formal process of making absolutely certain that the information on your retired IT gear is gone forever, completely unrecoverable. For any business, this isn't just a cleanup task; it's a core piece of your risk management strategy and a legal necessity.
Why Secure Data Destruction is a Business Imperative
When it comes to retired IT assets, simply "getting rid of them" without a certified process is a massive gamble. Failing to handle data destruction professionally exposes your company to huge, unnecessary risks. We're talking about crippling financial penalties, brand damage that can take years to repair, and a total collapse of customer trust.
Think about the journey of that old server. From the moment you unplug it to its final destination, it's vulnerable. If it’s just sold off, donated, or tossed in a recycling bin without proper sanitization, the data is still there for the taking. This kind of oversight can land your business in hot water, directly violating compliance rules like HIPAA, the FTC Disposal Rule, and PCI-DSS, which carry serious legal weight. To learn more, check out our guide on how to protect your company from data breaches with secure data destruction practices.
The Financial and Reputational Stakes
The consequences of dropping the ball on data destruction are real and severe. A single data breach can easily cost a company millions in fines, legal battles, and the costs of notifying every affected customer. But the hit to your wallet is often just the beginning. The long-term damage to your reputation can be even worse. Customers and partners trust you with their data, and a breach tells them you failed to protect it.
To give you a better idea of what's at stake, here’s a breakdown of the risks your business can't afford to ignore:
The Real Costs of Improper Data Disposal
| Risk Category | Potential Impact on Your Business |
|---|---|
| Financial Penalties | Fines from regulatory bodies like the FTC or HHS can reach millions of dollars per incident. |
| Legal Costs | Defending against lawsuits from customers, partners, or employees whose data was exposed is expensive and time-consuming. |
| Brand Damage | News of a data breach erodes customer trust overnight, leading to lost business and a tarnished public image. |
| Competitive Disadvantage | Competitors can use your security failures against you, while potential partners may see you as too risky to work with. |
| Intellectual Property Theft | Retired devices often contain trade secrets, R&D data, and strategic plans that could be stolen and used by rivals. |
It's clear that a "hope for the best" approach just doesn't cut it. The risks are simply too high for any commercial enterprise.
This growing awareness is driving a major shift in how businesses handle their old tech. The global market for data destruction services is booming, fueled by tougher regulations. Market estimates show the industry is expected to grow from USD 7.70 billion in 2024 to approximately USD 16.82 billion by 2030. This explosion in growth reflects how seriously governments and industries worldwide are taking data privacy.
A robust data destruction policy isn't an expense—it's an investment in business continuity, compliance, and your brand's integrity. It's your last line of defense against a breach coming from hardware you thought was long gone.
Of course, securing data isn't just about retired assets. It’s just as important to manage threats while devices are still in use. Knowing how to remove viruses from computers is crucial for maintaining security day-to-day. Ultimately, a complete IT asset disposition (ITAD) plan that includes certified destruction isn't a tech option; it’s a modern business necessity.
Decoding the Methods of Data Destruction
Hitting the "delete" button feels final, but when it comes to sensitive business data, it's anything but. True, professional data sanitization uses specific, verifiable techniques designed to make information completely unrecoverable. Each method strikes a different balance between security, cost, and whether you can reuse the old gear, so picking the right one is key for your business operations.
The goal is simple: make the data impossible to get back. This can be done with software that overwrites old files, powerful magnets that scramble the information, or by physically smashing the hardware to bits. Your choice really depends on what kind of storage device you have and your company's security policies.
Software-Based Erasure: Data Wiping
Data wiping, also known as data erasure, is a software-driven process. It works by methodically writing random characters over every bit of an existing hard drive or solid-state drive (SSD). Think of it like painting over a canvas multiple times with different colors—eventually, the original image is completely gone. A single pass often isn't enough, which is why professional services use multiple overwriting passes to make absolutely sure the original data is history.
This is the go-to method for businesses that want to reuse or resell their IT assets, since the drive itself is left in perfect working order. The most important part, however, is getting a verified report that the job was done right.
- Best for: Hard Disk Drives (HDDs) and Solid-State Drives (SSDs) you plan to reuse, resell, or donate.
- Key Advantage: It preserves the physical hardware, which maximizes the value you can get back from it.
- Consideration: The process can be slow for large volumes of drives, and you need software that provides a verifiable certificate of erasure.
If you're looking to align your process with federal guidelines, it's a good idea to get familiar with government standards. You can dive deeper into the specifics in our overview of NIST SP 800-88 guidelines for media sanitization.
Magnetic Degaussing
Degaussing is a specialized technique that only works on magnetic storage like traditional HDDs and older backup tapes. It blasts the device with a super-powerful magnetic field, which instantly and permanently scrambles the magnetic particles on the drive's platters where your data lives.
Imagine a library where the text in every single book is instantly garbled into a meaningless jumble of letters. The books (your drives) are still on the shelf, but the stories they held are gone forever. Degaussing is fast and incredibly effective, but it also fries the drive's firmware, rendering the hardware completely useless afterward. It’s a one-way street.
It's also worth noting this method does nothing for modern flash-based media like SSDs, since they don't store data magnetically.
Physical Destruction: Shredding and Crushing
When data security is your top priority and you have no plans to reuse the hardware, physical destruction is the final answer. This means using industrial machinery to shred, crush, or pulverize a storage device into tiny, unrecognizable pieces. It’s just like a paper shredder turning a sensitive document into confetti, but for hard drives, servers, and other enterprise IT equipment.
This method offers the most satisfying, visual proof that the data is gone for good. There's no coming back from this.
- On-Site vs. Off-Site: Destruction can happen right at your facility (on-site) using a mobile shredding truck for total transparency, or the devices can be securely transported to a certified facility (off-site).
- Security Level: This is the gold standard for data security. There is zero possibility of reconstructing the data.
- Media Types: Works on everything—HDDs, SSDs, backup tapes, phones, and even optical discs.
This decision tree helps visualize how to figure out if your retired IT assets are a potential liability or can be managed for compliance.
The flowchart drives home a critical point: every piece of old hardware is a ticking time bomb until it’s properly sanitized or destroyed by a certified professional.
Choosing the Right Data Destruction Method for Your Business
Picking the best data destruction method isn't always straightforward. You have to weigh the sensitivity of your data against the potential value of the hardware. This table breaks down the most common techniques to help you match the right method to your specific situation.
| Method | Best For | Security Level | Key Advantage |
|---|---|---|---|
| Data Wiping (Software) | Reusable HDDs & SSDs | High | Preserves asset value for resale or redeployment. |
| Degaussing (Magnetic) | Magnetic media (HDDs, tapes) | Very High | Extremely fast for large quantities of magnetic drives. |
| Physical Destruction | All media types; end-of-life assets | Absolute/Highest | Provides undeniable proof of destruction. |
Ultimately, the right choice ensures your data is gone for good while aligning with your organization's goals, whether that's maximizing your return on investment or achieving the highest possible level of security.
Navigating Data Disposal Compliance and Regulations
Failing to have a formal process for secure data destruction isn't just a security blind spot—it's a direct violation of federal and state laws. Staying compliant isn't a suggestion; it's a legal mandate with some seriously steep financial and reputational consequences. For any business, figuring out how to navigate this complex web of rules is the key to avoiding huge penalties and protecting sensitive information.
These rules all exist for one core reason: to protect the data of customers, patients, and clients. Regulations spell out exactly how organizations must handle and dispose of sensitive information sitting on retired IT assets. Just wiping a hard drive without verification or tossing old gear into a general electronics bin simply doesn't cut it.
Key Regulations Governing Data Disposal
Several major regulatory frameworks lay down the law for data destruction. While they each have a different focus, they all share a common goal: ensuring sensitive information is made completely unrecoverable when equipment is retired. Getting a clear handle on these rules is the first step toward building a compliant ITAD program.
Here are some of the most important regulations your business needs to know about:
- NIST SP 800-88: The National Institute of Standards and Technology's Special Publication 800-88 is the gold standard for media sanitization. It outlines specific methods for clearing, purging, and destroying data on different types of media, acting as a best-practice guide for all commercial sectors.
- HIPAA: The Health Insurance Portability and Accountability Act demands that healthcare organizations and their business associates protect patient health information (PHI). The HIPAA Security Rule specifically requires policies that address the final disposal of ePHI and the hardware it lives on.
- FTC Disposal Rule: As part of the Fair and Accurate Credit Transactions Act (FACTA), this rule requires businesses to take reasonable measures to guard against unauthorized access to consumer information during disposal. It applies to nearly any business that handles consumer or employee data.
- PCI-DSS: The Payment Card Industry Data Security Standard is a set of rules for any company that accepts, processes, stores, or transmits credit card information. Requirement 9.8 gets very specific about destroying media that contains cardholder data.
For businesses in the healthcare world, the details of these rules are especially critical. To get a deeper dive into the specifics, check out our guide on IT equipment disposal and HIPAA requirements.
The High Cost of Non-Compliance
Ignoring these regulations can be a disaster. Fines for getting it wrong can easily climb into the millions of dollars for a single incident. A HIPAA violation, for example, can lead to penalties of up to $50,000 per violated record. Beyond the immediate hit to your wallet, a public breach can permanently tarnish your brand and shatter customer trust.
Partnering with a certified IT Asset Disposition (ITAD) vendor is the smartest way to navigate these complex legal waters. A professional partner ensures every step of the data destruction process is compliant, documented, and audit-ready.
A certified vendor will provide a Certificate of Data Destruction for every single asset they process. This document is your legal proof of compliance. It effectively transfers liability away from your organization and proves you took the necessary steps to protect sensitive data. In a world of tightening regulations, this paperwork isn't just a nice-to-have—it's essential protection for your business.
The Critical Role of Certification and Chain of Custody
Properly destroying data is only half the job. The other half—and arguably the more critical part for your business—is proving you did it. Without solid documentation, you're left exposed to legal and financial risks, even if every last bit of data was wiped clean. This is where certification and a rock-solid chain of custody become your best friends in compliance.
Think of the chain of custody as a documented evidence trail for your old IT gear. It starts the second a device leaves your facility, tracking its every single move—from your loading dock, onto the secure truck, and all the way to the destruction facility. Every time the asset changes hands, it's logged. This creates a clear, auditable record proving your sensitive hardware was never lost, stolen, or mishandled along the way.
This meticulous tracking leaves no room for error and no gaps where a data breach could happen. It gives you a transparent, defensible story of the entire disposal process.
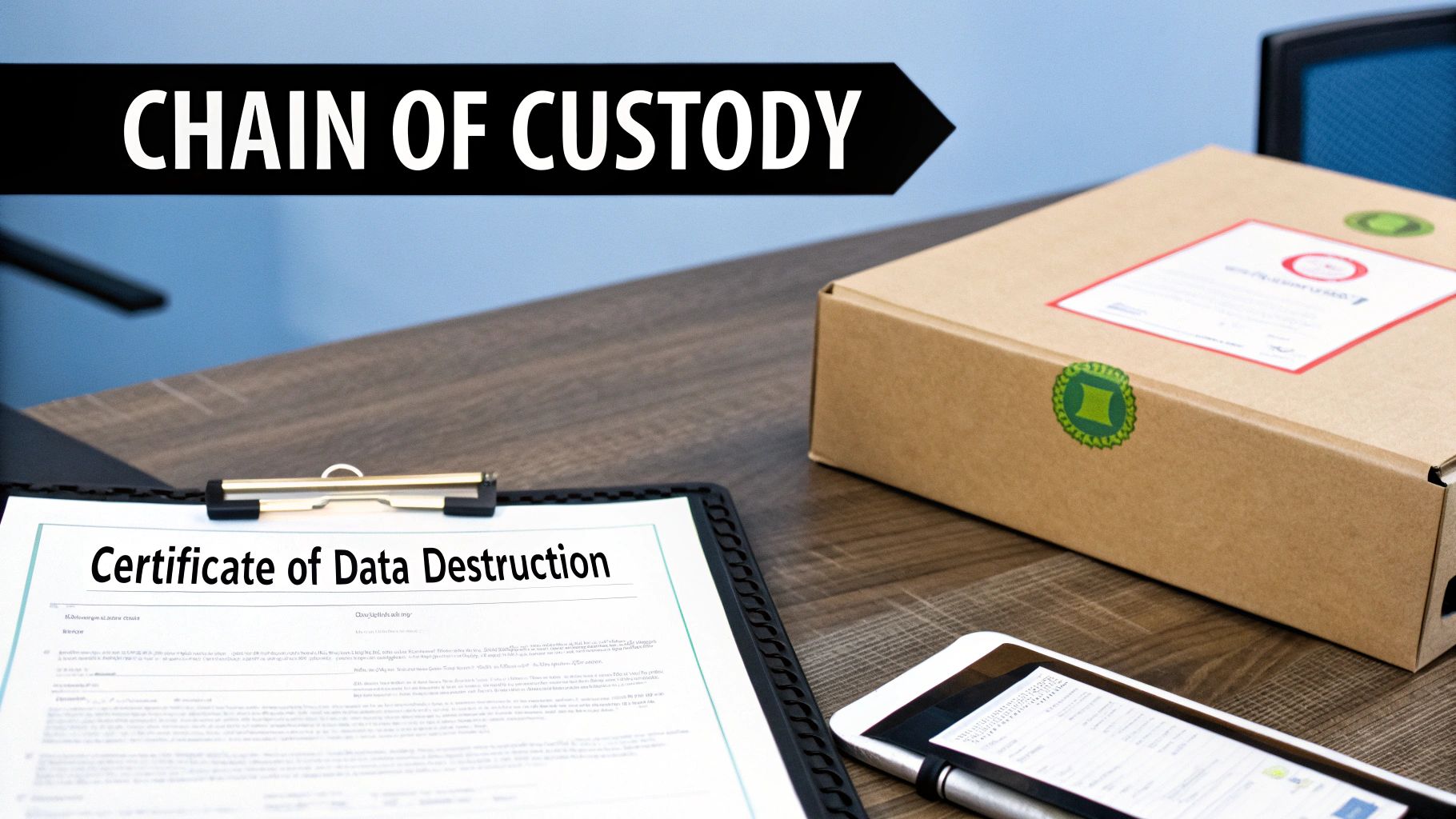
Why a Certificate of Destruction Is Your Legal Shield
Once the secure process is complete, your ITAD partner provides you with a Certificate of Data Destruction. This isn't just a receipt; it’s your official, legal proof that you met your data protection obligations. It's the document that will shield your organization from future claims or audits related to those disposed assets.
A well-drafted certificate formally transfers liability from your company to the vendor. It confirms you took every necessary step to protect sensitive information. If a regulator ever comes knocking, this certificate is your first and best line of defense.
A Certificate of Data Destruction is the final, crucial step in risk mitigation. It closes the loop on the asset lifecycle, providing the concrete proof needed to satisfy auditors, stakeholders, and regulatory bodies.
Essential Elements of a Valid Certificate
Not all certificates are created equal. A flimsy, vague document offers about as much protection as a paper umbrella in a hurricane. To be legitimate and defensible, a Certificate of Data Destruction needs specific, detailed information.
Here’s what your certificate absolutely must include:
- Unique Serial Numbers: A full list of the unique serial numbers for every single asset that was destroyed.
- Method of Destruction: A clear description of the exact method used—like shredding, crushing, or degaussing—and confirmation that it aligns with standards like NIST 800-88.
- Date and Location: The specific date and address where the destruction occurred.
- Chain of Custody Reference: A reference number or link to the chain of custody records that tracked the secure transfer.
- Authorized Signatures: The signature of an authorized person from the certified ITAD vendor who oversaw the process.
This level of detail isn't optional—it's essential for real compliance. If you're wondering what this kind of professional paperwork should look like, you can learn more about a proper destruction certificate format and its key parts. Without this documented proof, your business is just operating on trust, and trust alone won't hold up in an audit.
How to Choose the Right Data Destruction Partner
Picking a partner to handle your company's sensitive data is a critical business decision. The right ITAD vendor becomes an extension of your security team, guarding your information as if it were their own. But the wrong one can open you up to a world of risk. You need to look past the price tag and really dig into a provider's certifications, processes, and transparency.
Your first step should be to check for non-negotiable industry certifications. These aren't just fancy logos for a website; they're hard-earned proof that a vendor meets the highest standards for security, environmental responsibility, and ethical operations. They tell you an independent auditor has kicked the tires and confirmed the vendor is serious about the secure destruction of data.
Essential Vendor Certifications
Make sure any potential partner holds current, recognized certifications. Think of these as the baseline for proving they know what they’re doing and can be trusted with your business assets.
- R2v3 (Responsible Recycling): This is all about environmental stewardship, worker safety, and data security. An R2v3-certified vendor is committed to ensuring your old tech is managed responsibly and doesn't end up in a landfill.
- e-Stewards: Often seen as the gold standard, e-Stewards certification has extremely strict rules. It prohibits shipping hazardous e-waste to developing nations and requires the absolute highest levels of data security and environmental protection.
Seeing these certifications means a provider is committed to both protecting your data and being a good corporate citizen. It’s assurance that your equipment will be handled correctly from the moment it leaves your hands.
On-Site vs. Off-Site Destruction Capabilities
A critical decision you'll face is where the data destruction happens. A flexible ITAD partner should provide both on-site and off-site options to fit different security requirements and operational needs.
On-site destruction is exactly what it sounds like—a mobile shredding truck comes right to your facility. This approach lets your team witness the physical destruction of hard drives and other media firsthand. It offers the ultimate peace of mind and an ironclad, unbroken chain of custody.
Off-site destruction involves having your assets securely transported in locked, GPS-tracked vehicles to a certified facility. For larger volumes of equipment, this is often the more practical and cost-effective route. When you're working with a certified vendor who documents every step, it’s just as secure.
Critical Questions to Ask Potential Vendors
Before you sign on the dotted line, come prepared with a list of tough questions. How a vendor answers will tell you everything you need to know about their expertise and whether they’re truly committed to protecting your business.
A trustworthy ITAD partner will welcome detailed questions and provide clear, transparent answers. Vague responses or an unwillingness to share process details are major red flags that should not be ignored.
Here are a few essential questions to get the conversation started:
- How do you guarantee a secure chain of custody from pickup to final disposal? Get into the details. Ask about their locked containers, sealed trucks, GPS tracking, and the security measures at their facility.
- Can you provide detailed, asset-level reporting for our audits? A top-tier partner will give you serialized reporting that tracks every single asset, its final status (recycled, resold, or destroyed), and a matching Certificate of Data Destruction.
- What’s your process for data-bearing devices that fail the wiping process? They need a clear, documented plan for physically destroying any drive that can't be successfully erased. You can learn more about what professional hard drive destruction services should involve.
- Can we tour your facility or witness the destruction process? A vendor who is confident in their security and processes will have no problem with you stopping by for a visit or watching the action. Transparency is key.
The global market for secure data destruction is growing fast—it's projected to hit USD 3.2 billion by 2031. This boom is happening because of rising data privacy fears and tougher regulations, forcing businesses to get serious about professional destruction. By asking the right questions, you can find a partner ready to meet these high standards. You can read more about this growing market and its drivers to understand the trends.
Building Your Company's IT Asset Disposition Program
Knowing the theory is one thing, but taking decisive action is what ultimately protects your business. This is where a formal IT Asset Disposition (ITAD) program comes in. Think of it as your operational playbook—a structured, repeatable, and legally defensible framework for managing the secure destruction of data on retired hardware. It’s what turns a potential liability into a managed risk.
A solid ITAD program transforms asset retirement from a chaotic, last-minute task into a streamlined business function. Bringing in a professional partner like Beyond Surplus from the start can help you design an efficient and scalable program that actually fits how your organization works.

Core Stages of an ITAD Program
Building your program isn’t complicated, but it does require a few key stages. Each step is designed to ensure security and accountability from the moment an asset is unplugged to its final disposition. Following these steps helps create a robust system that stands up to any scrutiny.
-
Asset Inventory and Classification: First, you need to know what you have. Create a detailed inventory of all IT assets slated for retirement, including serial numbers, asset tags, and device types. The critical part here is classifying each asset based on the sensitivity of the data it holds. This decision dictates the entire process that follows.
-
Defining Secure Logistics: Next, map out a secure plan for collecting and transporting these assets. This means defining strict protocols for on-site packing, using locked and sealed containers, and requiring GPS-tracked vehicles. You're building an unbroken chain of custody from your facility all the way to the final processing location.
-
Execution and Verification: This is the action phase. Data is destroyed according to the classification you set earlier. Whether you opt for on-site shredding for maximum transparency or certified off-site wiping to allow for asset resale, this step must be followed by verification. A Certificate of Data Destruction for each and every serialized asset is non-negotiable proof of compliance.
-
Reporting and Auditing: The final stage is all about the paperwork. Consolidate all documentation—inventory lists, chain of custody logs, and destruction certificates—into a complete audit trail. This is the file you’ll pull out to demonstrate regulatory compliance and give stakeholders peace of mind.
The Growing Importance of Formal ITAD
If you're wondering whether a formal ITAD program is really necessary, just look at the market. In 2025, the global data destruction services market was valued at around USD 11.38 billion. It's forecasted to more than double to USD 26.08 billion by 2032.
That kind of explosive growth signals a major shift in how organizations view the data lifecycle, driven by everything from digital transformation to stricter sustainability mandates. You can get more details on the booming data destruction market and what’s behind it.
By creating a formal ITAD program, you are not just managing old equipment; you are actively managing business risk. A well-designed program ensures that your company's data security is handled professionally, consistently, and in full compliance with all regulations.
Common Questions About Secure Data Destruction
Even with a solid plan for retiring old IT gear, questions always pop up. Getting clear on the details helps IT and facility managers ensure the company is protected. Let's tackle some of the most common questions we hear from businesses about secure destruction of data.
Is Deleting Files or Formatting a Drive Good Enough?
In a word: no. Not even close. When you delete a file or format a drive, you're essentially just removing the signposts that tell the operating system where to find the data. The data itself is still sitting there on the drive, and it's surprisingly easy to get back with basic recovery software. For a business, this is an unacceptable risk. Real data destruction means either overwriting that data so thoroughly it's gone for good or physically annihilating the drive.
What’s The Real Difference Between Wiping and Shredding?
This is a critical distinction for IT asset management. Data wiping is a software-based process where every single part of a drive is overwritten with random characters, making the original information impossible to recover. The key benefit? The physical hard drive is still perfectly usable and can be resold or repurposed, maximizing asset value recovery.
Shredding, on the other hand, is a physical destruction process. We use industrial machinery to physically pulverize the drive into small, unrecognizable pieces.
- Choose Wiping if the hardware still has value and you want to remarket it.
- Choose Shredding for drives that are at the end of their life or when your internal security policy requires absolute, physical proof of destruction.
The decision really boils down to reusability. Wiping preserves the asset's value for resale, while shredding offers the ultimate, visible confirmation that the data is gone forever—but at the cost of the hardware itself.
Why Do We Actually Need a Certificate of Data Destruction?
A Certificate of Data Destruction is more than just a piece of paper; it's your legal proof that you handled sensitive data responsibly. This document is your first line of defense in an audit and formally transfers the liability for that data from your company to your certified ITAD partner.
It contains all the critical details—asset serial numbers, the exact destruction method used, the date it happened. Without this certificate, you have no verifiable evidence of compliance. If a data breach were ever traced back to one of your old assets, you'd be exposed to significant fines and legal trouble. It’s your official record and your safety net.
For a comprehensive and compliant approach to managing your retired IT assets, trust the experts. Beyond Surplus provides certified electronics recycling, secure IT asset disposal, and transparent data destruction services for businesses. Contact us today to schedule a consultation.