For businesses in Georgia, managing outdated computers is a critical component of a robust security and compliance strategy. Partnering with a professional business computer disposal Georgia service ensures your company’s sensitive data is completely destroyed and that all retired IT equipment is handled responsibly. This proactive approach protects your organization from significant financial and legal liabilities.
Why Smart IT Asset Disposal Matters in Georgia

Georgia's thriving technology sector makes the state a major hub for data management and innovation. This rapid commercial growth, however, presents a significant operational challenge for businesses: a growing volume of outdated IT equipment, including computers, servers, and laptops, that requires secure and compliant disposal.
As companies upgrade their infrastructure—from advanced AI servers to new cloud systems—the stockpile of retired assets accumulates. Simply storing old computers, servers, and hard drives is not a viable solution; it's a security risk. Each device may contain a wealth of sensitive corporate information, including customer data, financial records, and proprietary intellectual property.
The Risks of Improper Disposal
Improperly handling end-of-life IT equipment can expose your organization to severe consequences. These are not hypothetical risks but real-world threats to your company's reputation and financial stability.
- Data Breaches and Financial Penalties: A single compromised hard drive can trigger a catastrophic data breach. This can lead to substantial fines from regulatory bodies enforcing standards like HIPAA or the FTC Disposal Rule, alongside costly lawsuits and irreversible brand damage.
- Environmental Non-Compliance: Electronic waste (e-waste) contains hazardous materials. If not disposed of correctly, these materials can cause environmental harm. Failing to adhere to proper e-waste recycling protocols can result in penalties and contradicts corporate social responsibility principles. Learn more about the environmental impact of electronic waste.
- Loss of Potential Revenue: Many retired IT assets retain residual value. Disposing of them without a professional assessment means forfeiting potential revenue that could be recovered through an IT asset buyback program.
The rapid growth of Georgia's tech sector, especially its position as a national powerhouse in data center investments, has directly accelerated hardware turnover. This surge means that IT asset disposition has become an essential conversation that, as some sustainability experts note, "not many of us had a couple years ago." This shift highlights the urgent need for a strategic approach to managing end-of-life electronics.
The Opportunity in Strategic ITAD
Partnering with a certified IT Asset Disposition (ITAD) provider like Beyond Surplus transforms this disposal challenge into a strategic opportunity. A comprehensive ITAD process is much more than simple recycling; it encompasses secure data destruction, asset value recovery, and certified, compliant disposal.
This ensures every piece of equipment is managed correctly, providing a verifiable chain of custody and complete peace of mind. For businesses in Georgia, this isn't just about discarding old equipment. It’s about protecting your organization, maximizing your return on investment, and demonstrating your commitment to environmental responsibility.
Building Your IT Asset Inventory and Disposal Plan
A successful computer disposal project starts long before pickup, beginning with a detailed and strategic plan. The cornerstone of this plan is a comprehensive IT asset inventory.
This master list documents every device slated for decommissioning. It is more than just a cleanup checklist—it defines the project scope, determines the potential value of your retired assets, and initiates an unbroken chain of custody.
Categorizing Your Assets for Disposal
While a basic spreadsheet is a good start, simply listing "50 laptops" is insufficient. This lack of detail prevents your ITAD partner from developing an effective strategy, providing an accurate quote, or fully protecting your business.
To execute this correctly, a granular approach is necessary. A useful inventory provides complete transparency and prevents surprises.
Here’s an effective structure for organizing your inventory:
- Asset Type: Group items logically, such as Laptops, Desktops, Servers, Networking Switches, Monitors, or Mobile Phones.
- Manufacturer and Model: Be specific. Instead of "Cisco switch," specify "Cisco Catalyst 9300." Use "Dell Latitude 7420" instead of just "Dell laptop."
- Serial Number & Asset Tag: Document both the manufacturer's serial number and your internal asset tag for dual-factor tracking.
- Physical Condition: Note the asset's condition. Is it functional? Does it have cosmetic damage like a cracked screen? Are parts missing?
- Specifications: This is critical for high-value equipment like servers. Record the CPU type, RAM amount, and hard drive capacity.
An accurate and detailed inventory is more than just an administrative task. It is the single most important document for establishing a verifiable chain of custody, which is essential for compliance and transferring liability to your disposal partner.
This level of detail also enhances your overall IT management. Understanding your asset landscape informs better preventive IT maintenance and sharpens your entire technology refresh cycle.
Putting the Plan into Action
Once your categories are defined, the data collection begins. This task can seem daunting, but a systematic approach makes it manageable. Assign team members to specific equipment types or office floors to divide the workload effectively.
For large-scale projects, consider using barcode scanners or asset management software to accelerate the process. These tools can often export data directly into a spreadsheet, reducing manual entry and minimizing human error.
The effort invested in creating a detailed inventory pays significant dividends.
A well-documented inventory allows you to share your list with an ITAD provider like Beyond Surplus and receive a precise service quote. More importantly, it enables an accurate estimate for any equipment eligible for our IT buyback program.
This transforms a potentially chaotic project into a streamlined, secure, and financially advantageous process. To see how this inventory fits into the broader strategy, review our guide on IT lifecycle management in Georgia. A clear inventory ensures that from the moment your assets leave your facility, every device is tracked, its data is destroyed, and its final disposition is certified.
Ensuring Total Data Security Through Certified Destruction
When retiring business computers in Georgia, the process is incomplete until all data is irretrievably destroyed. A forgotten hard drive or an improperly wiped server is a significant security vulnerability. For any Georgia-based company, ensuring total data security is a non-negotiable measure to protect your operations, clients, and corporate reputation.

The data on these drives can include customer lists, financial records, or proprietary R&D. Simply deleting files is ineffective, as the data can be easily recovered using basic software. True security demands certified destruction methods that render information permanently unreadable.
Physical Destruction vs. Data Wiping
There are two primary methods for data destruction: physically destroying the storage media or using specialized software to wipe it. The optimal choice depends on whether the hardware will be reused or if the sole objective is to ensure data can never be recovered.
Let's examine the options available to businesses in Georgia.
On-Site vs. Off-Site Data Destruction Methods
| Feature | On-Site Destruction (Shredding/Wiping) | Off-Site Destruction (Shredding/Wiping) |
|---|---|---|
| Security | Maximum security. You witness the entire process, providing an unbroken chain of custody. | High security. Assets are transported in locked, tracked vehicles to a secure facility. |
| Best For | Highly sensitive data, strict compliance needs (healthcare, finance), and absolute peace of mind. | Large volumes of assets, budget-conscious projects, and standard compliance requirements. |
| Logistics | A mobile shredding truck or data wiping station comes directly to your Georgia office. | Secure pickup from your location and transport to a specialized destruction facility. |
| Cost | Typically higher due to the convenience and dedicated resources. | Generally more cost-effective, especially for bulk disposals. |
| Verification | Direct visual confirmation that your drives have been destroyed or wiped. | Documented chain-of-custody from pickup to destruction, followed by certification. |
Both on-site and off-site methods, when performed by a certified professional, meet stringent compliance standards. The decision often depends on your organization's specific risk tolerance and operational requirements.
Software-Based Data Wiping
If your retired computers still hold resale value, physical destruction is not the ideal solution. This is where professional data wiping, also known as data sanitization, is employed. We use specialized software to overwrite a hard drive completely with random data, often in multiple passes.
This process adheres to strict standards like the NIST 800-88 Guidelines for Media Sanitization, the gold standard for data erasure utilized by federal agencies. A successful wipe guarantees no data remains, making the device safe for resale and helping you recover value from your retired assets.
Explore how professional data destruction services in Georgia operate and help your business maintain compliance.
A Certificate of Data Destruction is your legal proof of compliance. It's not just a piece of paper—it’s the document that officially transfers liability for the data from your company to your disposal partner. It’s your shield in an audit or legal dispute.
The Power of a Certificate
Regardless of the method chosen—shredding or wiping—the process is not complete until you receive a Certificate of Data Destruction. This is your official, auditable proof that you have performed due diligence.
The certificate should list the serial numbers of the devices, the destruction method used, the date of completion, and a statement confirming that all work was performed according to industry standards. Without it, you cannot prove that you protected your sensitive data. It is the final step that closes the loop on your IT disposal project and safeguards your business from future claims.
Navigating Georgia's Compliance and E-Waste Regulations
For any Georgia business, disposing of old computers and servers is more than an operational task; it's a matter of legal compliance. Navigating the complex landscape of federal and state regulations is essential to protect your company from heavy fines, reputational damage, and legal action. A certified ITAD process is not optional—it's a critical risk management function.
At the federal level, the FTC Disposal Rule mandates that businesses take reasonable measures to protect consumer information on retired records. When this data resides on a hard drive, "reasonable" means certified data destruction.
Industry-Specific Compliance Mandates
In addition to federal rules, many businesses in Georgia must comply with strict, industry-specific data protection laws. These regulations dictate precisely how sensitive information must be handled through its entire lifecycle, including final destruction.
- Healthcare (HIPAA): The Health Insurance Portability and Accountability Act requires the protection of patient health information (PHI). A single discarded device still containing PHI constitutes a major violation, with penalties reaching millions of dollars.
- Finance (GLBA): The Gramm-Leach-Bliley Act requires financial institutions to secure consumers' private financial data. This protection extends to data on retired IT assets, making secure disposal a mandatory part of GLBA compliance.
- Legal & Professional Services: Law firms and accounting agencies handle highly sensitive client information. A data breach from an improperly wiped device can compromise attorney-client privilege and result in severe legal and ethical consequences.
For businesses in these sectors, engaging a certified vendor for business computer disposal in Georgia is an essential compliance measure. Learn about our approach to compliant IT disposal in Georgia and how we help businesses meet these demanding standards.
The Impact of Georgia's Data Center Economy
Georgia's status as a major data center hub intensifies the need for secure and efficient ITAD. The state's generous tax incentives fuel intense competition, compelling operators to manage equipment lifecycles with maximum efficiency and security. This environment makes selecting the right disposal partner more critical than ever.
The scale is immense. Georgia's data center tax exemption program represents a significant investment, with the state projected to forgo $2.5 billion in sales tax revenue in fiscal year 2026 alone. With so much at stake, data centers require certified partners who can not only handle secure disposal but also maximize value recovery from retired assets.
Your best defense in a compliance audit is your paperwork. A Certificate of Data Destruction and a Certificate of Recycling aren't just receipts—they are your legal proof that you did your due diligence and properly transferred liability.
The Importance of Auditable Documentation
Ultimately, compliance is about verifiable proof. In the event of an audit or data breach investigation, you must be able to demonstrate that you took every necessary step to protect sensitive information. Professional documentation is your most valuable asset in this scenario.
When you partner with a certified ITAD provider like Beyond Surplus, you receive detailed, legally defensible documents that close the loop on your disposal project. These certificates list the serial numbers of every destroyed hard drive and confirm all materials were recycled in accordance with environmental regulations. This auditable trail provides the concrete evidence needed to satisfy auditors and protect your business.
Turning Retired IT Assets into Revenue
For many Georgia businesses, a storage room filled with old IT equipment represents a logistical and security challenge. However, that collection of retired servers, laptops, and networking gear is not just a liability—it can be a significant financial asset. With a strategic approach, your outdated hardware can become a hidden revenue stream.
This is where a modern business computer disposal Georgia strategy excels. Instead of merely paying for disposal services, you can collaborate with an ITAD expert to identify which assets retain market value. This process, known as IT asset value recovery or a buyback program, can significantly offset or even cover the entire cost of your disposal project.
Assessing the Value of Your Used Equipment
The first step is a comprehensive assessment to determine your equipment's Fair Market Value (FMV). This is not a rough estimate but a careful evaluation based on several key factors.
- Age and Generation: Newer equipment typically retains more value. We find that servers and networking gear from the last three to five years often have the highest recovery potential.
- Condition: A fully functional unit with minimal cosmetic wear will command a much higher price than a broken or incomplete device.
- Brand and Model: Enterprise-grade hardware from trusted manufacturers like Dell, HPE, Cisco, and Apple is consistently in demand on the secondary market.
- Current Market Demand: The value of specific components can fluctuate based on global supply. High-capacity RAM or certain CPUs can be particularly valuable.
A professional ITAD partner removes the guesswork. We analyze your asset inventory and provide a transparent quote based on current market conditions, so you know exactly what your equipment is worth.
What Types of Assets Have Resale Value?
While most electronics can be recycled, certain categories of IT hardware are prime candidates for a buyback program. These are assets that other businesses actively seek for their own operations, for spare parts, or for refurbishment.
Assets that often hold significant value include:
- Enterprise-grade servers and storage arrays
- Recent-generation laptops and desktops, especially in bulk
- Networking hardware such as switches, routers, and firewalls
- High-end workstations and monitors
When you start thinking of your IT disposal project as a value recovery opportunity, the whole financial picture changes. What used to be a pure cost center becomes an activity that can actually put money back into your budget.
Partnering for a Seamless Buyback Process
Attempting to sell old equipment independently can quickly become a logistical burden. The process involves testing each device, finding buyers, negotiating prices, and managing shipping—all of which diverts your IT team from its core responsibilities.
Partnering with Beyond Surplus simplifies the entire process. We manage every step, from initial valuation and quoting to secure logistics and final payment. This integrated approach ensures you maximize the financial return on your assets without the operational headaches. This financial recovery is a key component of a robust ITAD strategy. See how we handle it by exploring our asset recovery services in Georgia. A professional buyback program can transform your next IT refresh cycle into a financially positive initiative for your company.
Your Action Plan for Business Computer Disposal
This section provides a practical roadmap for a secure and streamlined IT asset disposal project. For IT managers and business owners across Georgia, this is your guide to executing an ITAD engagement successfully, eliminating risk and uncertainty from start to finish.
Consider this your step-by-step game plan, organized into clear, actionable milestones.
Key Milestones for Your Disposal Project
First, secure buy-in from key stakeholders. Present the security risks of inaction and the financial benefits of value recovery to your finance, legal, and department heads.
Next, create a detailed asset inventory. Document every device slated for disposal, including asset type, serial number, internal asset tags, and condition. This document is the foundation of the entire project.
Then, research and select a certified ITAD partner. Prioritize vendors with credentials like NAID AAA or R2 certifications. Request references and verify their data destruction methods and environmental policies. A certified vendor for business computer disposal Georgia is your best defense.
With a partner chosen, coordinate the logistics. Schedule a pickup that minimizes disruption to your operations. Your vendor must provide secure, GPS-tracked transportation to maintain a clear chain of custody from your facility to theirs.
Finally, the project is complete only when you have the necessary paperwork. Insist on receiving a Certificate of Data Destruction and a Certificate of Recycling. These documents are your official proof of legal and compliance obligations.
The following diagram illustrates how value recovery integrates into this process, converting a cost center into a revenue opportunity.
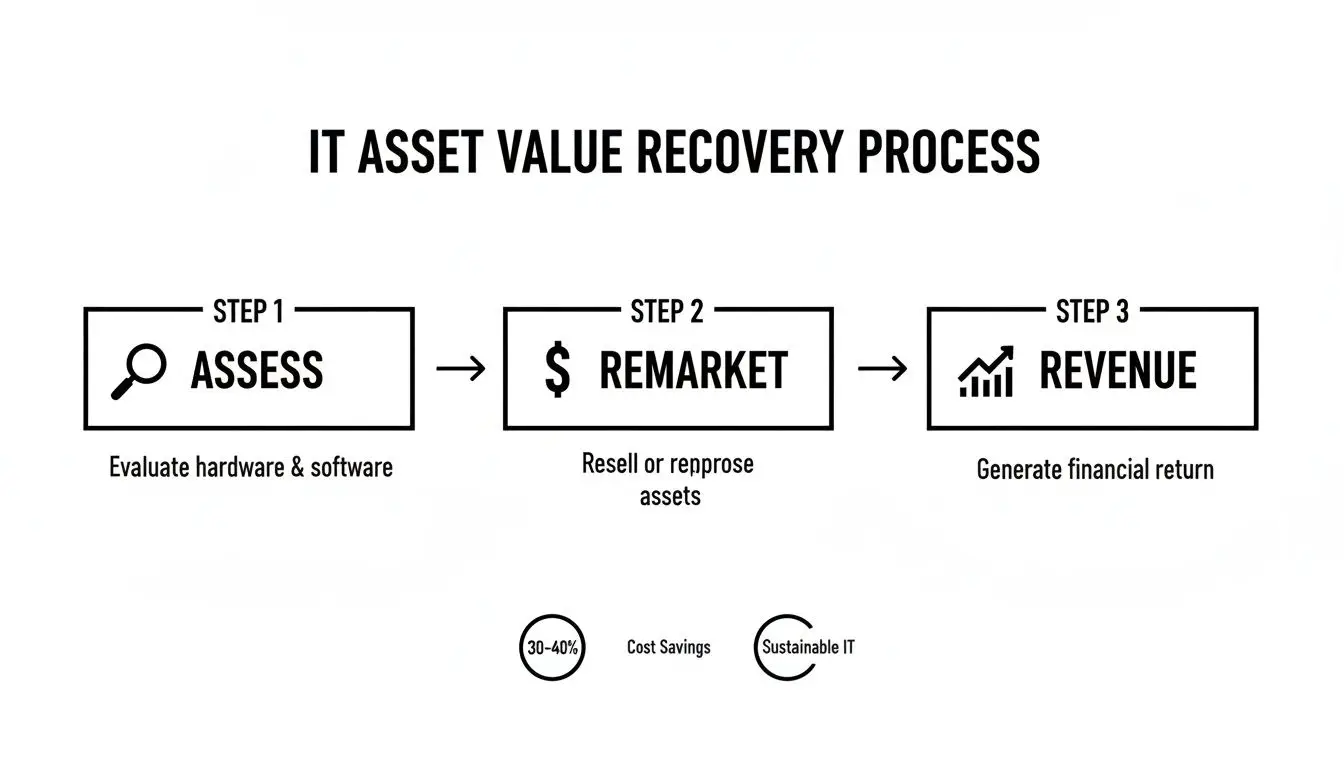
As shown, after a thorough assessment, assets with remaining value are remarketed, generating revenue that is returned to your business.
By following a structured action plan and partnering with a certified expert, you transform a complex obligation into a streamlined, secure, and financially beneficial business process.
Executing this plan with a knowledgeable partner removes uncertainty and guarantees compliance. Ready to implement your disposal plan with confidence?
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal.
Frequently Asked Questions About Business Computer Disposal in Georgia
When disposing of old IT assets, Georgia businesses often have questions regarding security, logistics, and compliance. We have compiled answers to the most common inquiries to help you proceed with confidence.
What Types of Business Equipment Do You Accept for Recycling?
We manage nearly all types of commercial IT and electronic assets. Our services are designed exclusively for businesses, enterprises, and other organizations; we do not accept residential or consumer electronics.
We are equipped for the secure disposal and recycling of:
- Servers, storage area networks (SANs), and other data center hardware
- Laptops, desktops, and workstations
- Networking equipment, including switches, routers, and firewalls
- Specialized assets such as medical devices and laboratory equipment
This commercial focus ensures we have the expertise to handle the unique security and logistical challenges associated with enterprise-grade technology.
How Can I Be Sure Our Company Data Is Secure?
Data security is the foundation of our business computer disposal Georgia services. We employ multiple layers of protection to ensure your sensitive information is permanently destroyed, providing documented proof.
We offer both on-site and off-site solutions to fit your security requirements, including physical hard drive shredding and data wiping software that meets the strict NIST 800-88 standard. Upon completion, you will receive a formal Certificate of Data Destruction, which serves as your official record of compliant data sanitization.
Think of a Certificate of Data Destruction as more than just a receipt. It's a legal document proving you did your due diligence to protect sensitive data. It shields your organization from liability if you ever face an audit or data security inquiry.
Do You Offer Service Throughout Georgia?
Yes. While our primary facility is located near Atlanta, we provide secure logistics and pickups for businesses across the entire state of Georgia and nationwide. We understand that a business in Savannah has the same critical security needs as one in Columbus.
Our in-house logistics team manages all transportation using our own fleet and a network of vetted partners. This guarantees a secure, fully documented chain of custody from the moment your assets leave your facility until they arrive at our secure plant for final processing. You receive consistent, reliable service regardless of your location.
For a partner that understands the security, compliance, and logistical challenges facing Georgia businesses, trust Beyond Surplus. Contact us today for a consultation on your IT asset disposal project.