A successful business electronic recycling program in Orlando, Florida doesn't just happen when you unplug old equipment. It begins with a solid internal policy that guides the entire process, protecting your company from data breaches, ensuring compliance with regulations like the Florida Information Protection Act (FIPA), and turning a logistical challenge into a secure, streamlined operation. For any Orlando business handling sensitive data, a documented IT Asset Disposition (ITAD) plan is an essential safeguard.
Building Your IT Asset Disposition Framework

Before your Orlando business can tackle that pile of end-of-life electronics, you need a blueprint. An ITAD policy is that foundational document, outlining your company's official procedures for retiring old tech. It eliminates guesswork and ensures everyone—from IT and finance to facilities management—knows their exact role.
A well-crafted ITAD policy is your first line of defense against compliance violations and security incidents. Without one, you're opening your business to inconsistent practices, data falling through the cracks, and potential fines from regulations like the FTC Disposal Rule.
Defining Asset Lifecycles and Responsibilities
A practical starting point is defining the lifecycle for different IT assets. For instance, a server might be on a five-year cycle, while employee laptops are refreshed every three years. Documenting these timelines creates predictable replacement schedules and simplifies budgeting.
Next, assign clear responsibilities. Who has the final authority to dispose of an asset? Who is in charge of tracking inventory, and who will coordinate the pickup with your business electronic recycling partner?
Key roles for commercial and enterprise services include:
- IT Manager: Oversees the entire ITAD process, from policy creation to reviewing final vendor reports for services like computer recycling or laptop disposal.
- Department Heads: Approve the retirement of assets used by their teams.
- Facilities Manager: Handles the logistics of staging assets and coordinating the physical e-waste pickup.
- Compliance Officer: Ensures the process aligns with legal standards like HIPAA, FIPA, or GDPR.
By clearly assigning these duties, you create a chain of command that builds accountability into every step.
Creating an Initial Asset Inventory
You can't manage what you don't measure. The next step is creating a detailed inventory of all electronics slated for disposal. This list must be more than a headcount; it should capture key details for security and logistical planning. If your inventory includes a large volume of company phones, consider specialized solutions like a mobile phone recycling service for small businesses as part of your framework.
Your inventory spreadsheet should include columns for:
- Asset Type: (e.g., Laptop, Server, Monitor, Printer, Medical Equipment)
- Brand and Model: (e.g., Dell Latitude 7420, HP ProLiant DL380)
- Serial Number or Asset Tag: For unique tracking of each device.
- Physical Location: (e.g., Building A, Room 301, Rack 12)
- Data-Bearing Status: A "Yes/No" flag to identify devices requiring secure data destruction.
Key Takeaway: An accurate inventory is the backbone of a defensible ITAD program. It becomes the master list for your chain-of-custody and proves every asset is accounted for, from your Orlando office to its final disposition. This initial list is the primary document you will provide to your ITAD partner.
How to Select the Right ITAD Partner
Choosing an IT Asset Disposition (ITAD) partner is one of the most critical decisions for your company's security and reputation. Think of them as an extension of your own team. A great partner protects your data and maintains compliance, while the wrong one can expose you to massive liabilities, from data breaches to steep regulatory fines.
This decision goes far beyond comparing price quotes. While cost is a factor, the real value lies in a vendor’s security protocols, verifiable certifications, and transparent process. You need a partner who can confidently assume liability for your retired assets, guaranteeing every device is handled through secure e-waste management.
Non-Negotiable Certifications
The first filter for potential ITAD partners is their certifications. These aren't just website logos; they represent proof of rigorous, third-party audits confirming a company meets the highest industry standards for data security, environmental practices, and employee safety.
Two certifications are the gold standard in the electronics recycling industry:
- R2v3 (Responsible Recycling): This is the baseline you should demand. An R2v3 certified partner has proven they have a secure facility, follow strict data sanitization protocols, and maintain a documented chain of custody from start to finish.
- e-Stewards: Often considered even more stringent, the e-Stewards standard includes a strict ban on exporting hazardous e-waste to developing nations, ensuring your old equipment doesn’t contribute to pollution overseas.
A vendor holding both R2v3 and e-Stewards certifications demonstrates a top-tier commitment to ethical and secure IT equipment disposal. Never partner with a company that cannot provide proof of at least one of these.
Evaluating Data Destruction Methods
Once you've confirmed certifications, focus on how they destroy your data. Your retired devices are full of sensitive information—customer lists, financial records, and intellectual property. Ensuring that data is permanently destroyed is non-negotiable.
You’ll generally find two main approaches for commercial services:
- On-site Shredding: A popular choice for a reason. A mobile shredding truck comes to your Orlando location, and you can physically witness your hard drives, SSDs, and backup tapes get turned into tiny pieces. It offers the highest level of assurance for sensitive operations like data center decommissioning.
- Off-site Wiping and Shredding: With this method, the vendor transports your assets in a secure, locked vehicle to their certified facility. There, drives are either wiped using software that meets NIST 800-88 standards or physically destroyed in an industrial-grade shredder.
This flowchart can help you visualize the vetting process, from checking certifications to final reporting.
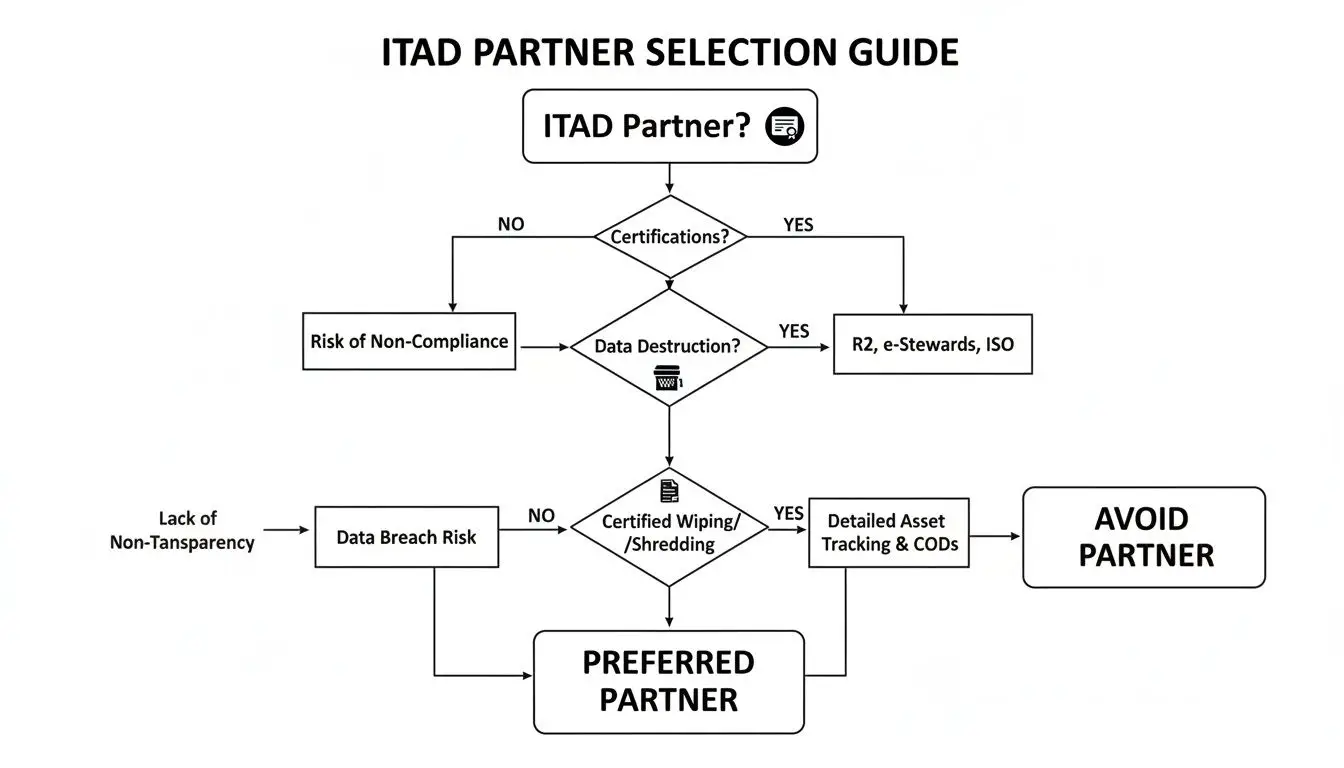
As you can see, a partner’s qualifications, destruction capabilities, and reporting procedures are all critical gates to pass through before making a final decision.
To help you compare vendors at a glance, we've put together this quick checklist.
ITAD Vendor Vetting Checklist
| Vetting Criteria | What to Look For | Red Flags to Avoid |
|---|---|---|
| Certifications | Active R2v3 and/or e-Stewards certification. Bonus for ISO 9001, 14001, 45001. | No certifications, expired credentials, or vague claims of being "green." |
| Data Destruction | Clear options for on-site/off-site shredding and wiping to NIST 800-88 standards. | No on-site option, unwillingness to let you witness destruction, using unverified software. |
| Chain of Custody | Serialized asset tracking from pickup to final disposition. GPS-tracked, company-owned vehicles. | Using third-party couriers, no asset tagging, manual or incomplete tracking sheets. |
| Insurance | High-limit liability insurance covering data breaches and environmental incidents. | Low coverage limits, refusal to provide a Certificate of Insurance (COI). |
| Reporting | Provides detailed Certificates of Data Destruction and Recycling for every job. | Generic, non-serialized reports or charging extra for essential documentation. |
| Value Recovery | Transparent process for testing, grading, and remarketing assets for a fair market return. | Vague or complex revenue-sharing models, promises of unrealistically high returns. |
This checklist is a great starting point, but don't be afraid to dig deeper and ask for specifics.
Scrutinizing Logistics and Documentation
A secure process is only as good as its weakest link, which is often found in logistics and paperwork. You need to get into the details of how a partner will handle your equipment the second it leaves your building.
Be sure to ask pointed questions about their process for your Orlando facility:
- Do they use their own fleet of vehicles and vetted employees, or do they subcontract transport?
- Are assets tracked with serialized barcodes from your dock to their final disposition?
- What kind of insurance do they carry? Always ask for their Certificate of Insurance to verify their coverage for data breaches and environmental issues.
Finally, ensure they provide ironclad documentation after the job is done. A professional ITAD provider will issue a Certificate of Data Destruction and a Certificate of Recycling. These documents are your legal proof that you fulfilled your compliance duties and successfully transferred liability. You can learn more about how to differentiate between top-tier IT asset disposition companies in our guide. This paper trail is your best defense if an auditor ever comes knocking.
Secure Data Destruction Is Non-Negotiable

Let's be blunt: a retired hard drive isn't just old equipment. It’s a ticking time bomb for data thieves. Ensuring every last byte of your company and customer data is permanently destroyed is the single most important part of any business electronic recycling plan. Anything less is a direct invitation for a data breach.
This isn’t about ticking a box. It’s about turning a major liability—old storage devices—into inert, risk-free material. Your main decision will come down to two paths: software-based data wiping or physical destruction.
Data Wiping vs. Physical Shredding
Data wiping, or sanitization, uses specialized software to overwrite an entire hard drive with random data, often in multiple passes. Done correctly, this makes the original information completely unrecoverable. The gold standard for this is NIST 800-88, a set of guidelines for media sanitization. For a full breakdown, check out our guide on the NIST SP 800-88 framework.
Physical shredding is exactly what it sounds like. Hard drives, SSDs, backup tapes, and phones are fed into an industrial shredder that grinds them into tiny metal fragments. It's tough to argue with a pile of metal shavings.
So, which do you choose? It depends on your risk tolerance and what you’re getting rid of.
- Data Wiping (NIST 800-88): This is the perfect choice for newer, working drives that could be resold to recover value. Sanitizing the drive this way preserves its value while eliminating your data security risk.
- Physical Shredding: This is the best option for old, broken, or non-functional drives, or for any device that held extremely sensitive information (e.g., from medical equipment disposal or data center decommissioning). It provides instant, undeniable proof that the data is gone forever.
With global e-waste projected to exceed 60 million metric tons by 2025, regulations are tightening. In the U.S., the FTC has strict rules about secure data disposal. This is especially true for the industrial sector, which drives 40% of recycling demand and often needs services like on-site shredding for product destruction and large-scale asset disposal.
On-Site vs. Off-Site Destruction
Next, you need to decide where this all happens. This choice has significant implications for your security and logistics.
On-Site Shredding
For many organizations in finance, healthcare, or government, having the destruction done on-site in Orlando is the only acceptable option. A mobile shredding truck comes right to your business, and your team can witness the entire process from start to finish.
Real-World Scenario: A hospital is retiring servers full of patient health information (PHI). They'll choose on-site shredding every time. This gives them an unbroken chain of custody and lets them physically see every drive get destroyed before it leaves their building, ensuring they stay compliant with HIPAA.
Off-Site Destruction
Certified off-site destruction is a very secure and cost-effective alternative. Your ITAD partner will transport your assets in a securely locked, GPS-tracked vehicle to their audited facility. Once there, the drives are either wiped or shredded under 24/7 video surveillance.
This is an excellent option for larger projects where cost is a factor and is perfectly safe for companies without the extreme compliance needs of a hospital. The key is working with a certified partner who provides a complete, unbroken chain-of-custody record.
Why You Need a Certificate of Data Destruction
No matter which method or location you choose, the process isn't over until the paperwork is done. A Certificate of Data Destruction (CoDD) is your official, legally defensible proof that you did your due diligence.
This isn’t just a simple receipt. A proper CoDD is a serialized document that lists every single hard drive or storage device by its unique serial number, confirming its destruction. This document is what formally transfers liability from your company to your ITAD vendor, and it's your get-out-of-jail-free card if an auditor ever comes knocking.
Getting Logistics and Asset Recovery Right

Even the most secure ITAD plan can fall apart the moment your assets leave the building. The logistics of moving equipment from your Orlando facility to a processing plant aren't just about getting boxes on a truck; it's about keeping every single asset secure from start to finish. This process begins well before the pickup, with careful asset tagging and professional packing.
Coordinating an electronic waste pickup, especially for a major project like a data center decommission, demands precision. The last thing you need is a disruption to your daily operations. This is why you need a partner who provides a detailed logistics plan, complete with scheduled arrival times, facility access requirements, and a crystal-clear scope of work.
Keeping an Unbreakable Chain of Custody
The single most important part of ITAD logistics is the chain of custody. Think of it as the documented, serialized trail that follows every device from the second it leaves your control until it’s either destroyed or resold.
It all begins with the inventory you provide. A professional ITAD vendor will use that list to generate serialized barcode labels for every single piece of equipment. Those barcodes get scanned at your facility during pickup, scanned again upon arrival at their secure plant, and scanned at every step in between.
This isn't optional. It’s what provides the auditable proof that no device went missing or was mishandled along the way. Ultimately, this detailed tracking is the evidence that backs up the Certificates of Destruction and Recycling you'll receive.
Turning Old Tech into New Revenue
While security is the top priority, a smart business electronic recycling program should also benefit your bottom line. This is where IT asset recovery, or an IT asset buyback program, makes a huge difference. It’s how you can turn retired laptops, servers, and networking gear into cash, which can go a long way toward offsetting your disposal costs.
Not every piece of equipment will have a second life, but you might be surprised by what does. The key is to identify assets that still have remarketing potential.
Here’s what typically determines an asset's value:
- Age: Equipment that is 3-5 years old generally offers the best return.
- Condition: Devices that are functional and look clean will always fetch a higher price.
- Brand and Model: Enterprise-grade gear from brands like Dell, HP, and Cisco holds its value far better than consumer-grade hardware.
- Specifications: Higher-end builds with more RAM, faster processors, and larger storage are more in demand.
A transparent partner will give you a clear evaluation, grade your assets, and offer a fair market price. Getting familiar with the process helps you understand how effective asset recovery services can transform your ITAD program from a cost center into a value generator.
The Booming Market for Used IT Assets
The opportunity for value recovery is bigger than ever. According to research from Fact.MR, the global electronics recycling market was valued at USD 43.2 billion in 2025 and is on track to hit an incredible USD 147.9 billion by 2035. That's a compound annual growth rate of 13.1%.
PCs and laptops are a huge part of this, making up 45% of the recycling market share, while industrial users account for 40% of the demand. These numbers paint a clear picture: there's a strong and growing secondary market for refurbished IT equipment, and your Orlando business can benefit from it.
Key Insight: Value recovery isn’t just a nice-to-have; it's a strategic pillar of a modern ITAD program. When you work with a vendor that has strong remarketing channels, you can turn depreciated hardware into real financial returns and prove the program's ROI to your stakeholders.
Ensuring Compliance and Reporting Your Impact
Your job isn't finished just because the truck has pulled away from the loading dock. The final leg of any professional business electronic recycling program is all about documentation, proving compliance, and showing the positive impact you've made. That paperwork from your ITAD partner? It’s much more than a receipt—it's your legal proof that the job was done right.
This documentation is your shield and your megaphone. On one hand, it creates an auditable trail confirming you've met your obligations under rules like the FTC Disposal Rule and HIPAA. On the other, it provides powerful data for sustainability reports, which matter more and more to customers, investors, and your own team.
Decoding Your Certificates of Destruction and Recycling
Once your assets are processed, a certified vendor like Beyond Surplus will provide two essential documents: a Certificate of Recycling and a Certificate of Data Destruction. They sound similar, but they serve two very different and equally critical roles in closing out your ITAD project.
Certificate of Recycling: This confirms that all your non-data-bearing assets (think monitors, keyboards, mice) and the sanitized metal shells of your old computers were handled in an environmentally sound way. It should break down the total weight and types of materials recycled, officially passing the environmental liability from you to the vendor.
Certificate of Data Destruction: This is the big one for risk management. It’s your itemized, serialized proof that every single hard drive, server, and phone you handed over was securely wiped or physically destroyed.
Pro Tip: Never, ever accept a generic, non-serialized certificate. A legitimate certificate must list every asset by its unique serial number or asset tag. This creates an unbreakable chain of custody back to your original inventory list and is absolutely non-negotiable for proving compliance.
Navigating the Complexities of Data Privacy
Getting the right certificates is just one piece of the compliance puzzle. The world of data privacy is a minefield of shifting regulations, with laws like GDPR, CCPA, and the new Florida Information Protection Act (FIPA) setting a very high bar for how companies handle personal data—even when it's on a device headed for the shredder.
These laws have serious teeth, and claiming ignorance won't save you. One misplaced hard drive could trigger a seven-figure fine. To get your ITAD policies airtight, it’s worth consulting a specialist like a Florida Data Privacy Lawyer to make sure you're aligned with current legal standards. A little proactive legal advice now can prevent a massive headache later.
Leveraging Your Impact for Sustainability Reporting
In today's market, a strong Environmental, Social, and Governance (ESG) profile isn't just nice to have; it's a competitive advantage. Your electronics recycling program is a goldmine of positive data for these reports. The information on your Certificate of Recycling lets you quantify your company’s contribution to a healthier planet.
This data helps you tell a compelling story. You can report on things like:
- The total pounds of e-waste diverted from landfills.
- The amount of hazardous materials managed safely.
- The volume of valuable resources recovered and put back into the circular economy.
Sharing these numbers in annual reports, on your website, or in marketing materials makes your commitment to sustainability real and tangible. It shows customers and investors you’re actively addressing the global e-waste problem.
The global context makes this even more powerful. While Europe formally collects 42.8% of its e-waste, the USA recycles a mere 15% of its 6.92 million tonnes. In 2022, only 22.3% of e-waste was documented as properly recycled worldwide, a figure expected to drop to 20% by 2030 as waste generation skyrockets. By documenting your efforts properly, you demonstrate leadership in a world that’s falling behind.
Common Questions About Business Electronic Recycling
As you build out your company's ITAD plan, a few common questions always seem to pop up. We hear them all the time from IT managers and business leaders trying to do the right thing with their commercial e-waste.
Getting clear answers is key to creating a secure and effective business electronic recycling program. Let's tackle some of the most frequent ones so you can move forward with confidence.
What Is the Difference Between R2 and e-Stewards Certification?
This is a big one. Both R2 and e-Stewards are the gold standard for electronics recyclers, but they come at it from slightly different angles. Knowing the distinction helps you pick a partner that truly matches your company's goals.
R2 (Responsible Recycling): Think of this as a flexible, market-based standard. It's all about verifying solid practices for environmental safety, worker health, and—most importantly—data security. An R2v3 certified recycler has proven they have a secure process from start to finish with a documented chain of custody.
e-Stewards: This standard came from the environmental group Basel Action Network and is known for being more rigid. Its core mission is an absolute ban on exporting hazardous e-waste to developing nations.
Key Insight: A vendor with either certification is a great starting point for your Orlando business. But if your company has a strong global corporate social responsibility (CSR) focus, you might lean toward e-Stewards. Many of the best ITAD providers, including Beyond Surplus, hold both certifications to cover all the bases for their enterprise clients.
Can We Recover Value from Our Old Office Computers?
Absolutely. In fact, you should expect to. This is a crucial part of any modern ITAD program, often called IT asset recovery or asset remarketing.
Equipment that’s still relatively new—usually in that three-to-five-year-old range—and in good working order can have significant value. Your ITAD partner will test, grade, and resell these assets on established secondary markets.
The money from those sales can often offset, or even completely cover, the costs of recycling your older, non-working gear. When you're talking to a potential partner, dig into their buyback program. Ask how they determine value and what their revenue-sharing model is. You're looking for total transparency here.
How Do We Recycle Specialized Medical or Lab Equipment?
Recycling specialized gear from a healthcare or research setting requires a vendor who understands the unique compliance and safety demands. This is a core commercial service and should not be left to chance.
Medical equipment disposal and laboratory equipment disposal involves devices that can contain unique materials and fall under much stricter rules, especially around data privacy (like HIPAA) or biohazard safety.
Before anything gets picked up, it’s critical that these devices are professionally decontaminated according to all health and safety protocols. You must inform your ITAD partner exactly what kind of equipment you have. This allows them to confirm they have the right certifications and tools to handle the materials and, most importantly, destroy any patient data or proprietary research information stored inside.
Is an Employee E-Waste Recycling Day a Business Service?
No. While hosting an e-waste drive for your team is a fantastic initiative, it is completely separate from your company's official business electronic recycling program. The key difference comes down to ownership and liability. This distinction is critical to understand.
- Business Services: These focus only on company-owned assets. The entire process is locked down by a formal service agreement, complete with a documented chain-of-custody and serialized data destruction reports to protect your business. This is our focus.
- Residential Events: These deal with personally owned electronics from employees' homes. The legal agreements and liability shift entirely. These services are outside the scope of our commercial offerings.
You should never mix corporate assets with employee electronics in the same pickup. It completely invalidates the audit trail and the legal and security protections of your formal ITAD program. A professional vendor can help you run both, but they must be treated as two very distinct projects.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal in Orlando, Florida. Schedule a pickup or learn more about our nationwide services.