For businesses in Georgia, engaging a professional data destruction service is the only guaranteed method to permanently eliminate sensitive information on retired IT assets like hard drives, SSDs, and servers. Simply deleting files or allowing old equipment to accumulate in storage creates a significant and unnecessary risk. Certified data destruction ensures that information is irretrievably gone, protecting your company from costly data breaches and regulatory penalties. This guide outlines why secure data destruction is a critical component of any IT asset disposal strategy for Georgia-based enterprises.
Why Your Georgia Business Needs Secure Data Destruction
Leaving a retired hard drive unsecured is akin to leaving your company’s confidential financial records on a public sidewalk in downtown Atlanta. With the explosive growth of data creation and the increasing sophistication of cyber threats, the risks associated with improper disposal of retired technology are at an all-time high. For businesses across Georgia, from Savannah's logistics centers to Alpharetta's technology corridor, the consequences extend far beyond a simple data leak.
Negligent disposal practices can have a catastrophic impact on your organization. The data residing on a single decommissioned server or in a box of old laptops could easily contain:
- Client and Customer Data: Names, addresses, financial details, and other personally identifiable information (PII).
- Employee Records: Social Security numbers, payroll information, and confidential HR files.
- Proprietary Business Information: Your valuable trade secrets, internal financial statements, and strategic plans.
A breach involving this type of data not only tarnishes your corporate reputation but can also lead to severe financial repercussions from regulatory fines, civil litigation, and remediation costs.
The Real-World Risks of Inaction
Many business owners believe that formatting a drive or letting old IT equipment collect dust in a storage closet is a sufficient security measure. This is a dangerous misconception. Data can often be recovered from formatted and even physically damaged drives using readily available software tools. The only way to achieve absolute certainty that data recovery is impossible is through professional, certified data destruction.
Failing to properly destroy data on end-of-life assets isn't just a security oversight—it's a direct compliance risk. Federal regulations like the FTC Disposal Rule and industry-specific mandates such as HIPAA hold organizations accountable for protecting consumer information throughout its entire lifecycle, including disposal.
More Than Just Security—It's About Compliance
For industries like healthcare, finance, and legal services, the regulatory stakes are even higher. Organizations in Georgia must adhere to federal laws that mandate the secure disposal of sensitive information. Non-compliance can trigger steep fines and significant legal challenges. For instance, the Georgia Personal Identity Protection Act (GPIPA) requires businesses to notify residents affected by a data breach, a process that is both costly and damaging to public trust.
Professional data destruction services in Georgia provide a critical layer of protection by issuing a Certificate of Destruction. This document serves as legal proof of your due diligence. You can learn more about the benefits of secure data destruction and how it protects your company’s bottom line. Partnering with a certified expert like Beyond Surplus helps you mitigate these risks, ensuring your data is permanently eliminated and your company remains compliant.
Choosing Between On-Site and Off-Site Destruction
Once you have committed to securely destroying the sensitive data on your retired IT equipment, the next critical decision involves the method and location of the destruction. For businesses in Georgia, the choice typically falls between on-site and off-site services. Each approach offers distinct advantages tailored to different security needs, compliance requirements, and operational workflows.
On-site data destruction, often referred to as mobile shredding, brings the security process directly to your facility. A specialized vehicle equipped with industrial-grade shredders arrives at your location, allowing you to witness the physical destruction of every hard drive, SSD, or backup tape before the truck departs. This method provides the highest level of assurance and a completely transparent chain of custody.
Conversely, off-site data destruction operates like a high-security armored transport service for your data. Your retired devices are inventoried, packed into sealed, tamper-proof containers, and transported by trained, background-checked personnel in a GPS-tracked vehicle. The destruction takes place at a secure, access-controlled facility under 24/7 video surveillance, with the entire process meticulously documented from start to finish.
The choice between a DIY approach and professional destruction is a critical one, with major implications for your data security.
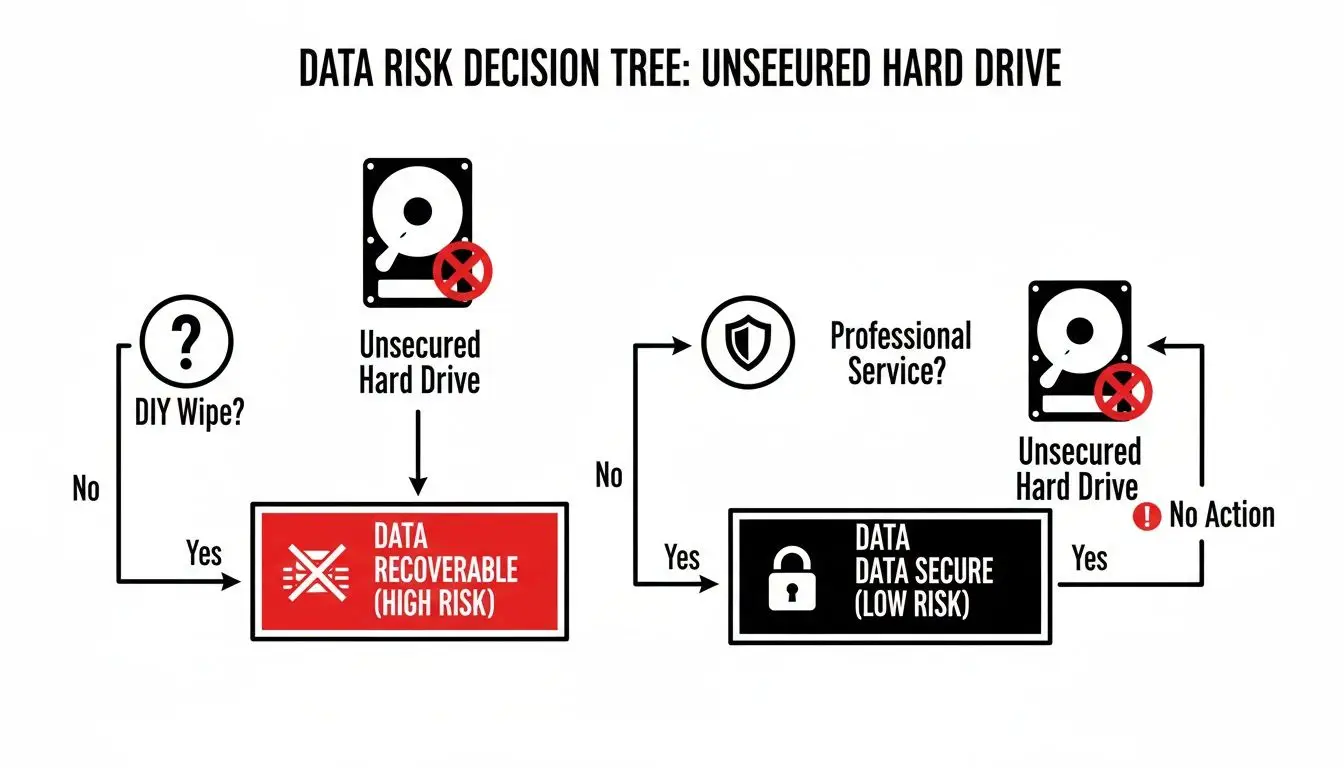
As you can see, trying to handle it yourself is full of risk and uncertainty. Professional services provide a clear, verifiable path to security and compliance.
On-Site vs. Off-Site: A Head-to-Head Look
To help you determine the optimal path for your organization, it is useful to compare the two methods side-by-side. Both are highly secure when performed by a certified vendor, but they cater to different business priorities.
This table breaks down the key factors to consider.
| Feature | On-Site Destruction (Mobile Shredding) | Off-Site Destruction (Facility-Based) |
|---|---|---|
| Security | Maximum. Witness destruction firsthand. Zero-break chain of custody. | Very High. Secure transport and 24/7 monitored facility. |
| Verification | Immediate. Watch it happen and get on-the-spot confirmation. | Documented. Receive a Certificate of Destruction after the process. |
| Logistics | Requires scheduling and physical space for a large truck. | Minimal disruption. Just need a secure pickup, no special space needed. |
| Best For | High-security needs, compliance audits, smaller batches. | Large volumes (e.g., data center cleanouts), cost-effectiveness. |
| Cost | Can be higher due to dedicated truck and personnel time. | Often more economical, especially for bulk disposals. |
Ultimately, whether you choose on-site or off-site destruction, the most important factor is the quality and certification of the vendor you partner with.
The Best Reasons for On-Site Destruction
On-site destruction is the preferred option for organizations with zero tolerance for risk. It is the only method that guarantees a zero-break chain of custody, as your assets never leave your physical sight before they are rendered completely inert.
This approach is ideal for:
- Maximum Security Needs: For stakeholders who require visual confirmation, on-site destruction eliminates any ambiguity regarding the disposition of your data.
- Immediate Verification: You receive confirmation and initial documentation on the spot, providing instant proof that the task is complete.
- Compliance Transparency: For industries governed by HIPAA, GLBA, or other stringent regulations, an on-site destruction event is an easily auditable and powerful demonstration of due diligence.
While incredibly secure, keep in mind that on-site services often require some scheduling lead time and a dedicated, accessible space for the shredding truck. To get a better feel for the process, you can learn more about our on-site electronics recycling in Georgia.
When Off-Site Destruction Makes More Sense
Off-site destruction is a highly secure, efficient, and practical alternative, particularly for large-volume projects or when on-site logistics are not feasible. With a certified partner like Beyond Surplus, you are not sacrificing security—you are simply changing the location of the process.
The entire procedure is built on a foundation of trust and meticulous documentation.
Off-site destruction relies on a documented, unbroken chain of custody. This includes secure, sealed containers, GPS-tracked transport, and destruction within a 24/7 monitored facility, ensuring your assets are protected at every step.
This option is particularly advantageous for:
- Large-Volume Projects: Decommissioning a data center with hundreds or thousands of drives is far more efficient at a specialized facility designed for that scale.
- Logistical Simplicity: It causes minimal disruption to your daily operations. There’s no need to allocate space for a large truck—just a straightforward, secure pickup.
- Cost-Effectiveness: Due to the economies of scale at a dedicated, high-volume facility, off-site services are often the more economical choice for larger projects.
Whether you need data destruction services in Georgia to occur at your location or at our secure facility, the end goal is identical. The most critical factor is partnering with a certified vendor who provides a transparent, auditable process and a Certificate of Destruction to guarantee compliance and protect your organization.
Staying Compliant With Data Privacy Laws in Georgia
For any business in Georgia, disposing of old IT equipment is more than an operational task—it is a legal obligation. Securely destroying the data on that equipment is a mandate, and failure to do so correctly can expose your organization to significant legal and financial consequences. While navigating these regulations may seem complex, understanding your responsibilities is the first step toward protecting your business.

While Georgia does not have a comprehensive, all-encompassing privacy law like some states, it treats data breaches with extreme seriousness. The primary statute is the Georgia Personal Identity Protection Act (GPIPA). This act mandates that companies must notify Georgia residents "without unreasonable delay" if their unencrypted personal data is compromised.
Consider the implications: if a retired hard drive from your office is not properly destroyed and its data is accessed by an unauthorized party, you are legally required to report it. This process is not only expensive but can also permanently damage your reputation and erode customer trust.
Key Federal Regulations Affecting Georgia Businesses
In addition to Georgia's state-level rules, several major federal laws mandate secure data handling for businesses nationwide. These regulations apply across the state and carry steep penalties for non-compliance, making professional data destruction services in Georgia an essential business practice.
Three of the most significant federal regulations include:
- HIPAA (Health Insurance Portability and Accountability Act): This applies to any organization handling Protected Health Information (PHI). Healthcare providers, insurers, and their business associates in Georgia must ensure PHI is rendered completely unreadable and indecipherable before any device is disposed of.
- GLBA (Gramm-Leach-Bliley Act): This law targets financial institutions, including banks, credit unions, and investment firms. The GLBA Safeguards Rule requires these entities to implement a security plan that specifically includes the secure disposal of customer financial information.
- FTC Disposal Rule: An extension of the Fair and Accurate Credit Transactions Act (FACTA), this rule applies to any business that uses consumer reports. It requires "reasonable measures" to dispose of such information securely, with certified shredding or wiping being the recognized gold standard.
These stringent regulations have propelled professional data security to the forefront. In fact, North America is projected to hold approximately 38% of the global data destruction market by 2035, largely due to regulations like HIPAA.
The Certificate of Destruction: Your Proof of Compliance
How do you prove compliance with these multifaceted rules? The answer is a Certificate of Destruction. This formal document, issued by a certified vendor upon completion of services, serves as your official legal record of due diligence.
A Certificate of Destruction is more than just a receipt; it's a legal instrument that transfers liability from your organization to your certified vendor. It is your single most important piece of evidence during a compliance audit or in the event of a legal challenge.
This critical document typically includes:
- The date of destruction.
- The method used (e.g., shredding, wiping).
- A unique serial number for tracking.
- A statement confirming the process was secure and final.
To remain fully compliant, it is also vital to understand your company's business records retention policies. Knowing the legal retention period for data is the first step; securely destroying it is the last. You can also learn more about NIST SP 800-88, the government's gold standard for media sanitization that guides all our certified processes. A strong partner is not just a service provider—they are an extension of your compliance team.
How to Select the Right Data Destruction Partner
Choosing a vendor to manage your sensitive data is a decision that should not be taken lightly. It is comparable to hiring a security firm to protect your company's most valuable intellectual property. For IT managers and business owners across Georgia, selecting the right partner for data destruction services is about much more than price—it is about ensuring security, demonstrating compliance, and safeguarding your corporate reputation.
A single weak link in your IT asset disposition (ITAD) chain can create significant liabilities.

To make an informed choice, you need a clear set of criteria to evaluate potential vendors. This ensures you partner with a true professional, not merely a recycling company that offers data destruction as a secondary service.
Look for Industry Certifications
Certifications are your first line of defense and are absolutely non-negotiable. They provide independent, third-party verification that a vendor adheres to strict standards for security, environmental responsibility, and professional integrity.
When vetting a partner, prioritize these credentials:
- NAID AAA Certification: This is the gold standard for the data destruction industry. It signifies that the vendor is subject to regular, unannounced audits of their hiring practices, security protocols, and destruction methodologies.
- R2v3 or e-Stewards: These certifications focus on responsible electronics recycling. They guarantee that after your data is destroyed, the physical equipment is managed in an environmentally safe manner and will not contribute to landfill pollution.
A vendor lacking these key certifications presents a major red flag, as they cannot offer the same level of independently verified trust.
Scrutinize the Chain of Custody
The "chain of custody" refers to the documented, unbroken trail of your assets from the moment they leave your facility until their final destruction. A weak chain of custody is a security breach waiting to happen.
Your potential partner must be able to demonstrate a rock-solid, auditable chain of custody. This isn't just a buzzword; it's the very foundation of a secure process.
Ask vendors to provide a detailed overview of their entire process. A secure chain of custody should always include:
- Secure Logistics: This involves using locked, sealed containers and GPS-tracked vehicles for transportation.
- Trained Personnel: All staff members who handle your assets must be background-checked and thoroughly trained in security procedures.
- Detailed Documentation: Every step, from pickup to final destruction, must be logged and auditable, often including individual serial number tracking.
Demand Comprehensive Insurance and Reporting
A true professional stands firmly behind their work, which is reflected in their insurance coverage and the quality of their reporting. Ensure any vendor you consider carries comprehensive data breach insurance. This policy protects your organization in the highly unlikely event of a security failure.
This type of insurance demonstrates that the vendor has a vested interest in the security of their process and is confident in their protective measures.
Finally, insist on detailed reporting. Upon completion of the service, you must receive a formal Certificate of Destruction. This legally binding document is your proof of compliance for any future audits. The certificate should clearly list the methods used (such as shredding to a specific size or NIST 800-88 compliant wiping) and identify the exact assets that were destroyed.
For a deeper dive into the overall process, our guide on what is IT asset disposition offers some valuable insights. By asking these tough questions and demanding verifiable proof, you can confidently choose a data destruction partner in Georgia who truly protects your organization.
Understanding the Growing Need for Secure ITAD
The accumulation of old IT hardware in a storage room is not just a local issue for Georgia businesses—it is a symptom of a larger global trend. The increasing demand for professional data destruction services in Georgia is a direct consequence of worldwide market dynamics. Understanding this broader context clarifies why a strategic IT Asset Disposition (ITAD) program is no longer optional but a fundamental component of modern business operations.
Several key factors are driving this shift. Technology is evolving at an unprecedented rate, meaning servers and laptops that were state-of-the-art only a few years ago are now being replaced. Concurrently, businesses are creating and storing more data than ever before, filling these devices with sensitive client, financial, and proprietary information.
The Accelerating Pace of Data and Risk
This constant cycle of technology upgrades and data generation leaves behind a mountain of retired IT assets, each representing a potential security risk. Every old hard drive or server in storage is a locked box of corporate secrets. Without a certified process to permanently destroy its contents, you are essentially hoping that no one ever discovers the key.
This reality has fueled a massive global market for secure data destruction. As businesses have become more aware of security threats and stringent regulations, the need for professional services has skyrocketed. This growth is a direct response to:
- The Explosion of Data: Increased digital business operations create vast amounts of sensitive information that must be properly managed at the end of the hardware lifecycle.
- Shorter Tech Lifecycles: Rapid innovation renders equipment obsolete faster, increasing the frequency of asset disposal.
- Rising Data Breach Incidents: High-profile data breaches have highlighted the immense financial and reputational damage a leak can cause, driving demand for guaranteed data destruction.
A Multi-Billion Dollar Global Industry
Thanks to these pressures, the global data destruction market has seen incredible growth. It’s valued at around $14 billion as of 2026, and it's projected to keep expanding. This growth directly reflects how seriously organizations are now taking data security and compliance. You can learn more about these forces shaping the data destruction market.
For businesses in Georgia's key industries—like healthcare, finance, and technology—this global trend has very real, local consequences. The same forces driving the worldwide market are impacting companies in Atlanta, Augusta, and Savannah right now.
Developing a robust ITAD strategy is not about following a trend; it is about proactively managing security threats and complex regulations. The message is clear: ignoring your end-of-life data is no longer a viable option. Companies that partner with certified data destruction experts are better prepared to protect their assets, comply with laws like HIPAA and GLBA, and maintain the trust of their clients in a data-driven world. This proactive approach is the foundation of modern risk management.
Partner With Beyond Surplus for Guaranteed Data Security
Choosing a provider for your data destruction services in Georgia is a critical business decision. It is not merely about disposing of old hardware—it directly impacts your company's security posture, reputation, and legal compliance. After evaluating the risks, regulatory requirements, and logistical options, one conclusion is clear: you need a certified, experienced, and trustworthy expert.
Beyond Surplus is that partner for businesses across Georgia. We deliver guaranteed security from the moment your assets are collected to the point of their final, verified destruction. Our entire process is engineered to eliminate risk and simplify your IT asset disposition, providing you with complete peace of mind.
Your End-to-End ITAD Solution
When you work with us, you're not just hiring a vendor; you're gaining a security partner. We have built our reputation on providing transparent, auditable, and reliable services that meet the highest industry standards.
Here’s what we offer:
- Certified Data Destruction: We employ NIST 800-88 compliant methods, including on-site and off-site hard drive shredding and certified data wiping. This ensures your data is completely unrecoverable, even with advanced forensic tools.
- Flexible Logistics: Whether you require the transparency of witnessing on-site shredding or prefer the efficiency of a secure off-site pickup, we tailor our services to fit your operational needs.
- Guaranteed Compliance: Every service is documented with a Certificate of Destruction. This is your official legal evidence of due diligence under regulations like HIPAA, GLBA, and FACTA.
- Responsible Recycling: We are committed to environmental stewardship. All non-data-bearing electronic waste is processed responsibly in accordance with strict R2v3 standards.
From Cost Center to Value Recovery
While securely disposing of old equipment is paramount, we also help Georgia businesses unlock the residual value in their retired IT assets. Our IT asset buyback program can offer a significant return on investment for qualifying equipment, turning a former cost center into a new source of revenue for your budget.
Choosing Beyond Surplus means choosing peace of mind. We combine absolute data security with responsible environmental practices and the potential for financial return, offering a complete solution for your organization's ITAD needs.
Don't let retired IT assets become a ticking time bomb. Partner with the leader in secure data destruction services in Georgia. We invite you to learn more about our comprehensive ITAD services in Georgia and see how we protect businesses just like yours every single day.
Ready to secure your data and streamline your asset disposition? Contact Beyond Surplus today to schedule a consultation and receive a customized quote for your needs.
Got Questions About Data Destruction? We've Got Answers.
When it comes to disposing of retired IT equipment, Georgia businesses often have numerous questions. This is perfectly normal. Understanding the correct procedures for data destruction can be complex, so we have compiled straightforward answers to the most frequently asked questions we encounter.
What Kinds of Devices Actually Need to Be Destroyed?
A common misconception is that data destruction is only necessary for old computers and servers. In reality, any device that has ever stored corporate information must be professionally sanitized or destroyed to eliminate risk.
This includes a surprisingly broad list of items:
- Hard disk drives (HDDs) and solid-state drives (SSDs)
- Company-issued smartphones and tablets
- Networking equipment like switches, firewalls, and routers
- Office printers and copiers, which contain internal hard drives
- Backup tapes and all other forms of removable media
If a piece of equipment ever held sensitive company, employee, or customer information, it requires certified destruction. Simply deleting files or performing a basic format is insufficient, as the data often remains recoverable.
Is a Certificate of Destruction Good Enough for an Audit?
Absolutely. A Certificate of Destruction from a certified partner is not just a piece of paper; it is a vital legal document. Consider it your official, auditable proof that you exercised due diligence and disposed of sensitive data in accordance with legal and regulatory standards.
When an auditor comes knocking to check for compliance with rules like HIPAA, GLBA, or FACTA, this certificate is the first thing they'll want to see. It legally transfers the liability for that data from you to your destruction vendor, protecting you from claims of negligence down the road.
Without that certificate, demonstrating responsible disposal becomes nearly impossible, leaving your organization exposed to significant legal and financial penalties.
How Should We Get Our Old IT Gear Ready for Pickup?
Preparing your equipment for our team is a simple process. The primary goal is to ensure the handoff is smooth, secure, and easily trackable.
Follow these quick steps:
- Make a Quick Inventory: Compile a list of the equipment designated for destruction. If required by company policy, record the serial numbers for your internal records.
- Round Up the Equipment: Consolidate all items in a single, secure location that is easily accessible for our team. This facilitates an efficient and non-disruptive pickup.
- Don't Bother Wiping Anything: Do not waste your IT team's valuable time attempting to wipe drives. Our certified destruction methods are designed to handle all data-bearing media, ensuring the data is forensically unrecoverable.
Simply inform us of your inventory, and we will manage the entire process, from secure transport to final certified destruction.
Does Data Wiping Really Erase Everything?
Yes, provided it is performed to a professional standard. Certified data wiping, also known as sanitization, is a process that uses specialized software to overwrite every sector of a hard drive with random characters. This is typically done in multiple "passes" to ensure no traces of the original data remain.
We strictly adhere to the NIST 800-88 "Guidelines for Media Sanitization." This federal standard guarantees that the original information is completely unrecoverable, even with sophisticated forensic tools. Upon completion, we issue a certificate that verifies the wipe was successful, providing you with definitive proof that the data is gone forever.
For total confidence in your IT asset disposal strategy, trust the certified experts. Beyond Surplus provides secure, compliant, and documented data destruction services across Georgia and nationwide.
Contact Beyond Surplus for a confidential consultation and customized quote.