A hard drive certificate of destruction is your official, legally-binding proof that sensitive data has been completely and permanently wiped out. This isn't just some flimsy receipt. Think of it as a critical legal document that officially transfers all liability for that data from your business to your certified destruction partner. It's your first line of defense if a data breach ever comes knocking.

Why This Document Is Your Shield Against Data Breaches
When your business retires an old computer, server, or any device with a hard drive, just hitting "delete" is nowhere near enough. Lingering data can easily be recovered, leaving your entire organization exposed to massive financial hits and a tarnished reputation. A certificate of destruction acts as a powerful shield, giving you undeniable proof that you took responsible, legally compliant steps to protect that sensitive information.
It’s a lot like transferring the title of a car. The second you sign that title and hand it over, you are no longer legally on the hook for what happens to that vehicle. In the same way, this certificate officially ends your liability for the data on a retired asset. It’s the final, unbreakable link in your chain of custody.
The Critical Role of Liability Transfer
Without that formal piece of paper, your company remains fully accountable for any data breach that gets traced back to improperly disposed-of equipment. The fallout from that can be devastating, especially with today’s strict regulations.
- Regulatory Compliance: A certificate is your golden ticket for auditors. It proves you met the strict disposal requirements of laws like HIPAA, GDPR, and the FTC Disposal Rule, which can be the difference between a clean audit and crippling fines.
- Legal Defense: If you ever face a lawsuit from a data breach, this certificate shows you performed due diligence and acted responsibly, which will seriously strengthen your legal position.
- Peace of Mind: Most importantly, it gives you verifiable assurance that your company's private files, customer data, and intellectual property have been permanently destroyed and can never fall into the wrong hands.
This document is so much more than paperwork; it’s a core piece of any solid risk management plan. You can see how this fits into a bigger security picture by reading our guide on how to protect your company from data breaches.
To help you see the bigger picture, here’s a breakdown of the certificate’s key functions and why they matter to your bottom line.
Key Functions of a Destruction Certificate
| Function | Business Implication | Primary Benefit |
|---|---|---|
| Proof of Destruction | Provides tangible evidence that specific devices were destroyed. | Protects against claims of improper data handling. |
| Liability Transfer | Legally shifts responsibility for the data to the destruction vendor. | Shields the business from fines and lawsuits post-disposal. |
| Chain of Custody | Documents the secure handling of assets from your door to final destruction. | Ensures an unbroken, auditable trail for compliance. |
| Compliance Verification | Serves as official documentation for regulatory audits (HIPAA, FTC, etc.). | Prevents non-compliance penalties and demonstrates due diligence. |
As you can see, each function plays a direct role in safeguarding your business not just from data thieves, but from legal and financial trouble, too.
Fortifying Your Data Defenses
Getting a certificate of destruction is the final, essential step in securing your end-of-life hardware. To round out your security posture, it's also smart to understand a comprehensive Data Loss Prevention strategy. While the certificate proves your data was destroyed, a DLP strategy helps protect that same data while it's still active and in use.
Ultimately, a hard drive certificate of destruction closes the loop on IT asset retirement for good. It transforms a potential liability into a verified, documented security control, ensuring your old tech never becomes the source of a future crisis.
The Anatomy of an Audit-Proof Certificate
Let's be clear: not all certificates of destruction are created equal. A vague, flimsy document might give you a false sense of security, but it will crumble the moment an auditor looks at it, leaving your business completely exposed.
A truly audit-proof certificate, on the other hand, is a detailed, legally defensible record. It builds an airtight chain of custody and tells a clear, verifiable story of exactly what happened to your sensitive data from start to finish.

Think of it like a receipt from a store. A basic receipt might just say "groceries," which doesn't prove much. But a detailed, itemized receipt lists every single thing you bought, its price, and the exact time of the transaction. A proper hard drive certificate of destruction is that detailed receipt—it leaves zero room for doubt and proves what was destroyed, when, and how. This level of detail is non-negotiable for proving due diligence.
The Foundation of Verifiability
At its heart, a strong certificate connects every single retired asset back to the destruction event. Vague descriptions are a massive red flag for auditors. If your certificate just says "Lot of 100 hard drives" or "50 lbs of mixed media," it’s practically worthless because it fails to prove your specific drives were destroyed.
True security is in the details.
For an auditor, this granular tracking is everything. It allows them to pick any asset from your original inventory records and follow its documented journey all the way to its final, verified destruction. This is the only way to close the loop on an asset's lifecycle and definitively end your organization's liability.
Essential Components of a Legally Defensible Certificate
An audit-proof hard drive certificate of destruction must contain several key elements to be considered legally sound. Each component plays a specific role in building an unbroken and verifiable record. If even one is missing, it can weaken your legal standing and compliance posture.
A comprehensive certificate must include:
- Unique Serial Numbers for Each Asset: This is the absolute most critical part. A serialized list provides an itemized accounting of every single hard drive, SSD, or other data-bearing device that was destroyed.
- Specific Method of Destruction: The document needs to state exactly how the devices were destroyed. Forget vague terms; it should specify "physical shredding to 1/4 inch particles" or "degaussing," making sure it aligns with standards like NIST 800-88.
- Precise Date and Location of Destruction: This information establishes a concrete timeline and physical location for the event, which is essential for audit trails and legal verification.
- Authorized Signatures: The certificate must be signed by an authorized representative from the IT asset disposition (ITAD) vendor, who is formally attesting to the accuracy of the information.
- Chain of Custody Reference: It should include a unique job or order number that links back to the complete chain-of-custody documentation, detailing the secure transport and handling of the assets from your door to theirs.
An inadequate certificate is more than just a documentation failure; it's a security failure. It signals a potential break in the chain of custody, leaving a gap that auditors and legal opponents can easily exploit.
To make sure your documentation is always audit-ready, it helps to know what a complete and professional destruction certificate format should look like. Partnering with a certified vendor like Beyond Surplus ensures that every certificate you receive is meticulously detailed, serialized, and built to withstand the toughest scrutiny, giving you documented peace of mind.
Staying Compliant in a World of Regulations
Data privacy laws aren't gentle suggestions; they're strict rules with serious financial teeth. Your hard drive certificate of destruction is the critical document that proves your responsible actions meet the complex legal landscape your business has to navigate. Think of it as your primary evidence, showing you held up your end of the bargain.
Without this proof, a retired hard drive becomes a ticking time bomb of liability. If a data breach investigation traces back to improperly handled media, it can unravel years of hard work. The certificate is what stands between your company and a finding of "willful neglect."
Translating Technical Standards into Business Protection
At the heart of secure data destruction are the guidelines from the National Institute of Standards and Technology (NIST). Specifically, NIST Special Publication 800-88 provides the framework for sanitizing media. For any business, getting a handle on its two key methods for permanent data removal is essential.
- Purge: This method uses logical or physical techniques to make data recovery impossible, even with state-of-the-art lab equipment. Think of degaussing, which uses powerful magnetic fields to wipe a drive clean.
- Destroy: This is the final word in data removal. It renders the media completely unusable for storing data ever again, making recovery impossible by any means. This includes methods like shredding, pulverizing, and incineration.
Your certificate of destruction has to specify which of these compliant methods was used. That detail is what gives the document its power, showing an auditor you didn't just toss out an old asset—you followed a federally recognized best practice for data elimination. You can learn more by exploring our detailed guide on NIST SP 800-88 compliance.
The Real-World Impact of Major Regulations
Simply listing regulations doesn't capture the immense risk they represent. Data breaches from improper hard drive disposal have caused devastating damage, making certificates of destruction indispensable for businesses everywhere. Under HIPAA, violations can lead to fines of up to $1.5 million per year for each violation category. A missing destruction certificate leaves a company defenseless against claims of 'willful neglect'.
GDPR raises the stakes even higher, with penalties reaching €20 million or 4% of annual global turnover, whichever hurts more. You can discover more insights about these staggering financial penalties and the importance of certified destruction.
Let’s bring these abstract rules into day-to-day business reality.
During an audit or data breach investigation, the first thing regulators ask for is documentation. A serialized hard drive certificate of destruction isn't just another piece of paper—it is your most crucial piece of evidence, stopping a regulatory inquiry in its tracks.
Navigating the Regulatory Minefield
Different industries face different sets of rules, but the need for proof is a constant across all of them. A properly executed certificate of destruction is universally accepted as evidence that you did your due diligence.
Key Regulations Where a Certificate is Vital:
- HIPAA (Health Insurance Portability and Accountability Act): For any healthcare provider or business associate handling Protected Health Information (PHI), a certificate is non-negotiable. It proves you have made PHI unreadable, indecipherable, and impossible to reconstruct.
- GDPR (General Data Protection Regulation): This regulation protects the data of EU citizens. The "Right to Erasure" (Article 17) requires companies to permanently delete personal data on request. A certificate is the only verifiable way to prove this has been done.
- FTC Disposal Rule: Part of the Fair and Accurate Credit Transactions Act (FACTA), this rule demands that businesses take reasonable measures to destroy consumer report information. Physical destruction with a corresponding certificate is a primary method of compliance.
Ultimately, these regulations all share a common goal: ensuring sensitive information is protected throughout its entire lifecycle. The certificate of destruction is the official document that closes that loop, confirming you upheld your legal and ethical duty to the very end. It brings abstract laws into the concrete reality of running a secure and compliant business.
Choosing Between On-Site and Off-Site Destruction
When it comes time to retire your sensitive data, you’re faced with two primary options: on-site and off-site destruction. Each approach has its own security protocols and logistical quirks. The best choice really boils down to your company's risk tolerance, compliance mandates, and internal security policies.
Think of it like this: on-site destruction is like hiring a private chef to cook in your own kitchen. You see every ingredient, watch every step, and know exactly what’s happening from start to finish. Off-site destruction is like dining at a five-star restaurant with a world-class reputation—you trust their proven processes and security to deliver a perfect, secure result behind the scenes.
The On-Site Destruction Advantage
With on-site destruction, the shredder comes directly to you. A specialized, mobile shredding truck pulls up to your facility, and you get to witness the entire process firsthand. This method delivers the ultimate level of transparency, which is why it's a top choice for organizations dealing with highly sensitive data or those with strict internal oversight rules.
The process is refreshingly direct and immediate:
- Your hard drives are scanned and inventoried right there at your location.
- One of your own employees watches as the drives are fed into the industrial-grade shredder.
- All that’s left is a pile of mangled, unrecognizable metal fragments.
A huge perk of this method is receiving your hard drive certificate of destruction on the spot. This instant proof closes the chain of custody loop before your assets even think about leaving your property, giving you immediate peace of mind.
The Secure Off-Site Destruction Process
Off-site destruction means your assets are securely transported to a specialized facility for disposal. While you don't get a front-row seat to the shredding, the entire model is built on an airtight, unbreakable chain of custody. The journey is meticulously documented and secured every step of the way, making it an incredibly reliable and efficient choice.
The security of off-site destruction isn't just a promise; it's a verifiable process. It hinges on locked containers, sealed and GPS-tracked trucks, 24/7 facility monitoring, and strict access controls to keep your assets protected from pickup to final destruction.
Here’s how the off-site process typically unfolds:
- Secure Collection: Your assets are placed into sealed, tamper-evident containers right at your office.
- Documented Transport: A detailed chain of custody log is started immediately, tracking the assets' journey.
- Facility Destruction: Once at the secure facility, the drives are inventoried again before being destroyed under constant video surveillance.
- Certificate Issuance: A serialized certificate of destruction is issued and delivered to you, often through a secure online portal, as soon as the job is complete.
This approach is often more cost-effective, especially for larger volumes, and can be much simpler from a logistics standpoint.
Comparing On-Site vs Off-Site Hard Drive Destruction
To make the decision clearer, it helps to see the two options side-by-side. This table breaks down the key differences, helping you weigh what matters most for your business's security and compliance needs.
| Feature | On-Site Destruction | Off-Site Destruction |
|---|---|---|
| Location | At your facility using a mobile shredding truck. | At a secure, specialized vendor facility. |
| Transparency | 100%. You witness the entire process firsthand. | Relies on a documented chain of custody and video surveillance. |
| Chain of Custody | The loop closes instantly on-site. | Meticulously tracked from your door to the destruction facility. |
| Certificate | Issued immediately upon completion. | Issued after destruction is complete at the facility. |
| Cost | Generally higher due to specialized equipment and travel. | Often more cost-effective, especially for larger volumes. |
| Best For | Highly sensitive data, strict compliance, or internal mandates. | Businesses seeking efficiency, cost savings, and logistical convenience. |
Both methods, when handled by a certified professional, are secure and compliant. The right one for you depends on balancing transparency, convenience, and cost.
Making the Right Decision for Your Business
Choosing between on-site and off-site services is a strategic call. With remote work creating new data risks, the demand for both verifiable destruction methods is climbing. In fact, the data destruction services market is expected to grow by USD 26.08 billion by 2032, showing just how critical this service has become.
To help guide your choice, think about these key factors:
- Data Sensitivity: If you're dealing with classified information, intellectual property, or critical patient data, the absolute transparency of on-site destruction might be a must.
- Compliance Needs: Some regulations might favor witnessed destruction. Double-check your industry's specific rules to see if one method is recommended over the other.
- Budgetary Constraints: Off-site destruction is usually more budget-friendly, especially for large-scale IT retirement projects, because it lets the vendor streamline their operations.
- Internal Policies: Your own company's security rules might state that data-bearing devices can't leave the building until they are physically destroyed.
Ultimately, whether you choose on-site or off-site destruction from a certified ITAD partner like Beyond Surplus, you’ll receive a legally defensible certificate of destruction. Whether you need to watch the shredder in action or prefer the efficiency of secure transport, there’s a compliant solution ready for you. You can learn more about on-site hard drive shredding services near you to see which option best fits your operational needs.
How We Turn Destruction Into Documented Proof
Knowing what a hard drive certificate of destruction should include is one thing. Seeing it executed flawlessly is another entirely. At Beyond Surplus, we put theory into practice with a transparent, meticulous process designed to give you compliant and verifiable proof that your data is gone for good. This isn't just about destroying hardware; it’s about building an unbroken, auditable trail that shields your business.
Our process kicks off the moment our team walks through your door. We don't just grab equipment and go. We immediately establish a documented chain of custody by scanning the serial number of every single asset slated for destruction. This first scan is the critical first link, ensuring total accountability from the very beginning.
Our Auditable Process Starts With a Scan
This individual, asset-level tracking is the bedrock of our service. Each device is logged into our secure system, creating a digital breadcrumb trail. This trail follows your asset through every single stage, whether you opt for on-site shredding right in your parking lot or secure transport back to our facility. This detailed approach removes all guesswork and provides the granular proof needed to satisfy any audit.
The infographic below lays out the two secure pathways we offer for both on-site and off-site destruction.
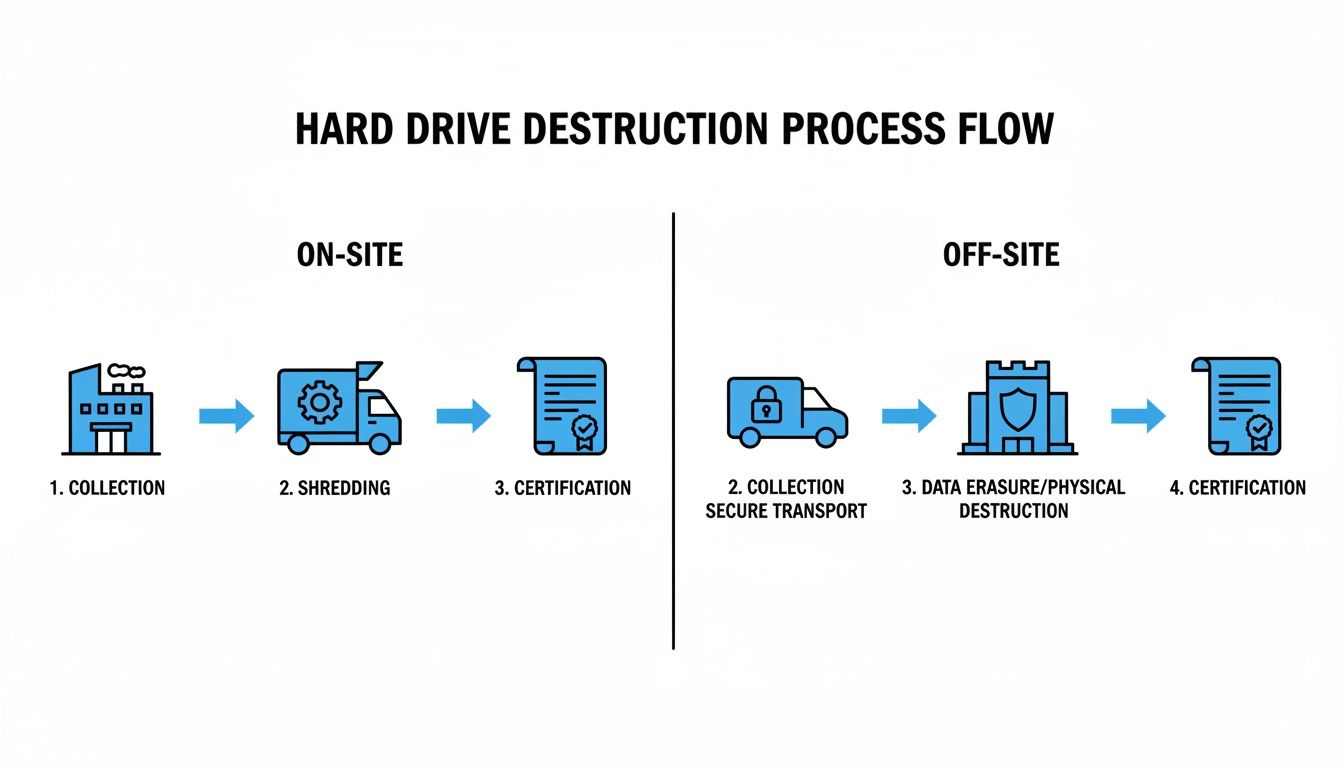
As you can see, both routes begin with secure handling at your location and end with a verified certificate. Compliance is guaranteed, no matter which method you choose.
Delivering Your Verifiable Proof of Destruction
Once the physical destruction is complete—either by our mobile shredding trucks on your property or inside our secure, monitored facility—we conduct a final reconciliation. We cross-reference the serial numbers of the destroyed assets against the initial inventory scan. This confirms that every single device is accounted for and has been successfully destroyed.
Only after this final check-off do we issue your serialized certificate of destruction. This document is far more than a simple receipt; it’s a legally defensible record that includes:
- A unique certificate number for the job.
- A complete, itemized list of every destroyed asset's serial number.
- The precise date and location of destruction.
- The specific destruction method used (e.g., physical shredding).
- An authorized signature from Beyond Surplus, attesting to the record's accuracy.
The need for such a buttoned-up, documented process is exploding. The global hard drive destruction service market was valued at USD 1.5 billion in 2023 and is projected to hit USD 3.6 billion by 2032. This growth isn't surprising—it's driven by businesses scrambling to comply with tough regulations and sidestep the massive costs of a data breach.
We give our clients secure, on-demand access to their certificates through a dedicated portal. This means you can pull up your documentation instantly for an audit or internal review, providing immediate proof of your due diligence.
This commitment to a transparent and verifiable system is how we deliver more than a service; we provide documented peace of mind. To get a full picture of our secure logistics and asset management, you can learn more about how our process works.
Answering Your Key Questions
Even after you've got the process down, some practical questions always pop up about hard drive certificates of destruction. Getting these answers right is the key to making sure your data disposal plan is truly solid. Let's tackle the most common ones to clear up any confusion and make sure you’re set up for success.
How Long Should We Retain a Certificate of Destruction?
The short answer? Keep them for a very long time—maybe even forever. While certain regulations give you a minimum timeframe, the best practice is to make these certificates a permanent part of your IT asset records.
Think of it as the final chapter in a device's life story. Rules like HIPAA require you to hold onto data security documents for at least six years. If you're a publicly traded company, the Sarbanes-Oxley Act (SOX) can push that to seven years or more, especially since IT assets are often tied to financial records.
But the real risk goes beyond just hitting a minimum deadline. A data breach investigation or a compliance audit can happen years after a piece of equipment was retired. Your certificate of destruction is the only lasting, verifiable proof that you did your part. It's the timeless evidence that closes the liability loop on that asset for good.
Is a Digital Certificate as Valid as a Paper Copy?
Absolutely. A digital certificate is just as legally sound as a paper one, as long as it contains all the necessary, audit-proof details. In fact, in today's world, digital copies are usually preferred because they're more efficient and secure.
The real power of a certificate isn't the paper it's printed on; it's the information it holds. As long as the document has the right stuff, its format doesn't matter.
Essential Elements for Any Format:
- A complete, serialized list of every single asset destroyed.
- The specific date, location, and method used for destruction.
- A clear chain-of-custody reference number.
- The authorized signature from the destruction company.
Digital certificates actually have a few big advantages. Reputable ITAD partners, like us at Beyond Surplus, give you access to your documents through a secure online portal. This means you can store, search, and pull up audit evidence in minutes, without ever worrying about losing a critical piece of paper.
What if a Vendor Provides a Vague or Non-Serialized Certificate?
A vague certificate is a massive red flag. You should consider it completely unacceptable. A document that just says "Lot of 50 drives" or "100 lbs of mixed media" is practically useless in an audit because it doesn’t prove your specific assets were actually destroyed.
This kind of sloppy paperwork points to a broken or nonexistent chain of custody, leaving a huge gap in your records that a regulator or lawyer could drive a truck through. If a vendor gives you a document like this, reject it immediately. Demand a serialized certificate that ties every single one of your devices to the destruction event.
If your vendor can't or won't provide a detailed, serialized certificate, the job isn't done. This is a sign of a fundamental flaw in their process and puts your company at serious risk. It's time to find a new, certified partner who gets why auditable proof is so important.
A proper certificate is simply non-negotiable. It's a core part of what you're paying for, right alongside the physical destruction service. Accepting anything less leaves you exposed.
Does a Certificate Guarantee Protection from a Lawsuit?
While no single piece of paper can make you 100% immune to legal trouble, a properly executed, serialized certificate of destruction is your absolute best line of defense. It’s powerful, tangible proof that your organization took its data security responsibilities seriously.
If you ever face a data breach investigation or lawsuit, the burden will be on you to show you took every reasonable step to protect sensitive information. That certificate becomes your Exhibit A. It proves that for the assets listed, a data leak couldn't have come from your old equipment because you have verifiable proof it was destroyed.
This documentation is crucial for shifting liability and can dramatically reduce potential fines and damage to your reputation. It might not stop someone from filing a lawsuit, but it gives your legal team the hard evidence they need to build a rock-solid defense. That's why a certificate is a cornerstone of any smart data security and risk management program.
At Beyond Surplus, we provide detailed, serialized Certificates of Destruction for every job, ensuring your business has the audit-proof documentation needed for full compliance and peace of mind. Contact us today to learn more about our secure and certified IT asset disposal services.



