For any business in Georgia, from a bustling Atlanta tech firm to a critical healthcare provider in Savannah, old hard drives represent a significant liability. Choosing professional hard drive shredding in Georgia isn't just about disposal; it's a fundamental component of modern risk management for commercial enterprises. Properly managing this final step protects your brand, secures proprietary data, and ensures full compliance with industry regulations.
Why Data Security Hinges on Professional Hard Drive Shredding
When IT assets reach the end of their lifecycle, the data stored on them doesn't simply vanish. A decommissioned server, an old office laptop, or a retired storage array can still hold a wealth of sensitive corporate information.
Simply deleting files or formatting a drive provides a false sense of security. The reality is that data can often be recovered with commercially available software, creating a tangible business risk.
Professional hard drive shredding physically destroys the drive's platters—the spinning disks where your data resides—making any information completely and permanently unrecoverable. It is the only foolproof method to guarantee that your confidential business, client, or employee information never falls into the wrong hands.
The Real-World Consequences of Inadequate Disposal
Many organizations underestimate the danger lurking in their discarded IT equipment. Common mistakes include piling old drives in a storage closet, tossing them into a general e-waste bin without certified destruction, or relying on inadequate DIY methods like drilling or hammering. These shortcuts leave companies vulnerable to severe consequences.
Consider the potential impact on your business:
- Customer and Client Data Leaks: Exposure of personal information, financial records, or purchase histories can lead to identity theft and irreparable damage to your reputation.
- Employee Information Breaches: Discarded drives might contain payroll data, social security numbers, and other private employee details, creating significant HR and legal liabilities.
- Intellectual Property Theft: Engineering plans, proprietary code, and strategic documents are the lifeblood of many companies. If exposed, this data can cripple your competitive advantage.
The financial fallout from these mistakes can be staggering. The average cost of a data breach for U.S. businesses climbed to $9.44 million in 2023, a figure that underscores the massive financial peril of improper hard drive disposal and highlights why Georgia companies must invest in secure shredding.
Ultimately, secure hard drive shredding is not just an operational expense—it's an essential investment in business protection. To learn more, protect your company from data breaches with secure data destruction practices in our detailed guide. This service effectively transfers liability away from your organization and provides a certified, audit-proof record that you have fulfilled your duty to protect sensitive information.
Choosing Your Data Destruction Method in Georgia
Once your Georgia business commits to secure data disposal, the next critical decision is how to execute it. This choice directly impacts your security posture, compliance standing, and operational efficiency. The primary methods available to businesses are on-site mobile shredding, off-site plant-based shredding, and certified data wiping.
Each method serves a specific purpose, and understanding the differences is key to aligning the right service with your organization's unique requirements. Your decision will depend on factors like data sensitivity, budget, internal security protocols, and whether the retired equipment has potential for reuse or resale.
On-Site Mobile Shredding: The Gold Standard for Security
For any organization that requires absolute certainty, on-site mobile shredding is the definitive solution. This service brings the destruction process directly to your facility anywhere in Georgia. A specialized shredding truck, essentially a high-powered industrial shredder on wheels, arrives at your location.
Your team can witness the entire process, from verifying the serial numbers on your hard drives against your inventory list to watching them enter the shredder. This approach provides undeniable, eyewitness proof of destruction and completely eliminates chain-of-custody risks, as your sensitive data never leaves your property intact.
Off-Site Plant-Based Shredding: A Secure and Efficient Alternative
Off-site shredding is a cost-effective and highly secure option, particularly for large-volume projects or situations where on-site logistics are impractical. With this service, your hard drives are collected from your location in locked, tamper-evident containers.
They are then transported in a vetted, GPS-tracked vehicle to a highly secure, access-controlled destruction facility. Upon arrival, the drives are shredded under continuous video surveillance. The entire process is meticulously documented to maintain an unbroken chain of custody from your facility to final destruction.
This flowchart illustrates the fundamental decision-making process for handling retired hard drives.
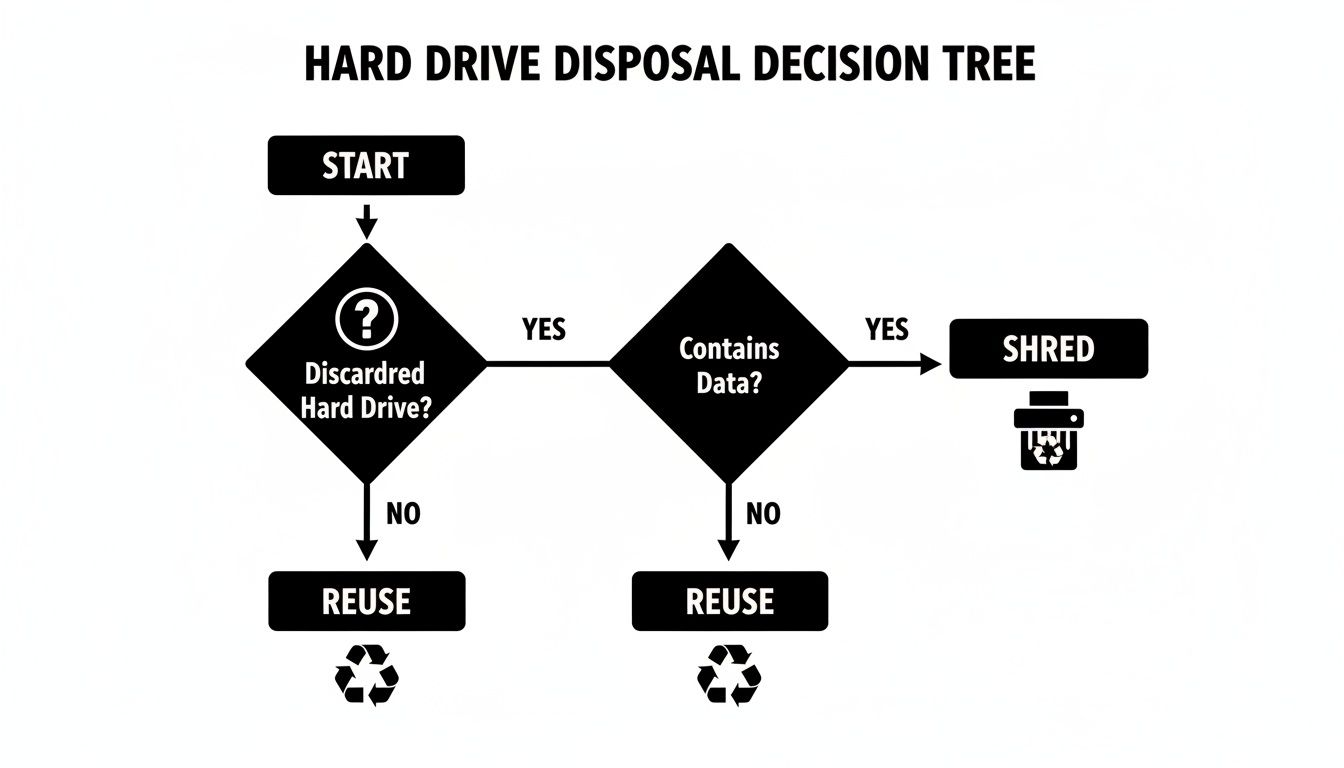
As shown, if a drive being retired contains sensitive data, physical shredding is the only path that ensures total security.
Considering Data Wiping and Degaussing
What if you need to eliminate data but wish to preserve the drive for reuse or resale? This is where certified data wiping and degaussing are utilized. Data wiping, or sanitization, employs specialized software to overwrite every sector of the drive with random data, making the original information irrecoverable.
To help you decide, here’s a quick comparison of these methods for different business needs.
Comparing Data Destruction Methods for Your Georgia Business
| Destruction Method | Best For | Key Advantage | Consideration |
|---|---|---|---|
| On-Site Mobile Shredding | Businesses with highly sensitive data (healthcare, finance, government) that require witnessed destruction. | Maximum security and peace of mind; eliminates chain-of-custody risks entirely. | Generally the most premium-priced option due to the convenience and security level. |
| Off-Site Plant-Based Shredding | Large-volume projects, routine disposals, or when on-site logistics are difficult. | Cost-effective for bulk destruction while maintaining a secure, documented process. | Requires trust in the vendor's chain-of-custody protocols and secure transport. |
| Certified Data Wiping | IT assets that will be resold, donated, or redeployed internally. | Allows for asset reuse, generating a return on investment and promoting sustainability. | The drive must be in good working condition; not an option for failed or damaged media. |
| Degaussing | Rapid, secure erasure of magnetic media like traditional hard drives (HDDs) and tapes. | An extremely fast and effective method for rendering magnetic data unrecoverable. | Does not work on SSDs (Solid-State Drives) and can render the drive unusable afterward. |
Ultimately, choosing the right method comes down to balancing your security requirements, budget, and sustainability goals.
Key Takeaway: While physical destruction offers absolute certainty, data wiping is a viable option for assets intended for remarketing. However, it requires the drive to be fully functional and is not suitable for damaged or failed media.
Degaussing is another powerful method that uses a high-powered magnetic field to completely scramble the magnetic platters inside a traditional hard drive. To better understand this technology, review our guide explaining what a degausser is and how it functions. Both wiping and degaussing must be performed by a certified vendor who can provide a certificate of sanitization as proof of erasure.
For the highest level of data security for end-of-life equipment, nothing surpasses the certainty of turning it into tiny metal fragments through physical shredding.
Preparing Your IT Assets for Secure Shredding

A successful shredding project begins long before our truck arrives at your Georgia facility. Proper preparation is essential for a seamless, efficient process and prevents logistical complications.
Pre-project planning not only ensures the destruction runs smoothly without disrupting your business operations but also strengthens your compliance posture and provides a solid audit trail.
Building Your Destruction Inventory
The first and most critical step is to create a detailed inventory. Your IT department should compile a comprehensive list of every device slated for destruction. This process goes beyond counting servers and laptops; it involves identifying every piece of equipment that contains data.
Think beyond the obvious, as overlooked devices often pose the greatest risk. Your inventory should account for hard drives in all corporate assets:
- Servers and Storage Arrays: These are the primary targets, often containing numerous drives.
- Desktop Computers and Laptops: Standard employee workstations that must be tracked individually.
- Network Appliances: Firewalls, routers, and switches have internal storage holding sensitive network configurations and data logs.
- Multifunction Printers and Copiers: Modern office machines contain internal hard drives that store images of every document copied or scanned.
For a bulletproof audit trail, ensure each line item includes the asset's serial number. This allows you to match your internal records precisely with the Certificate of Data Destruction we provide, offering undeniable proof that every device was accounted for and destroyed. For enhanced asset tracking, some companies use durable identifiers like engraved metal labels to maintain a clear chain of custody.
Physical Segregation and Coordination
Once your inventory is complete, the next step is to physically consolidate all assets marked for destruction. Designate a secure, controlled area—such as a locked storage room or a caged section of your warehouse—to stage the equipment. This simple step prevents an employee from mistakenly returning a server intended for shredding back into service.
Insider Tip: Clearly mark every pallet or container with bright labels reading "FOR DESTRUCTION." This visual cue prevents mix-ups and makes it easy for your staff and our logistics team to identify the correct equipment upon arrival.
This level of preparation streamlines the pickup process and demonstrates a clear, defensible internal procedure. We cover similar principles in our guide on how to prepare your computers, tablets, and phones for recycling. By taking these steps, your Georgia business ensures the entire operation is efficient, secure, and audit-ready from the start.
Meeting Compliance Standards with Certified Documentation
For any Georgia business handling sensitive data, disposing of an old hard drive is only half the task. The other, more critical half is proving you did it correctly. In the world of data destruction, undocumented actions are indefensible. Certified documentation is your best defense against regulatory scrutiny.
Regulatory bodies do not accept verbal assurances. Whether your business is in healthcare dealing with HIPAA, finance under the Gramm-Leach-Bliley Act (GLBA), or any other sector covered by the FTC Disposal Rule, the burden of proof rests entirely on you. You must be able to demonstrate a secure, compliant, and defensible process.
Your proof is the Certificate of Data Destruction. This is more than a receipt; it is a formal, legal document that serves as the official record of your data handling.
The Anatomy of an Audit-Proof Certificate
A legitimate Certificate of Data Destruction is a cornerstone of your risk management strategy. It is the document that officially transfers liability for the data on those retired drives from your company to your certified vendor. To withstand an audit, this certificate must contain specific, verifiable details.
Here’s what to look for on an audit-proof certificate:
- A Unique Serial Number: This enables tracking and allows you to match the certificate to your internal records.
- The Date of Destruction: Pinpoints the exact day the drives were destroyed.
- Method of Destruction: Specifies whether it was on-site shredding, off-site pulverization, or another method.
- A List of Destroyed Media: Ideally, the certificate should list the individual serial numbers of every hard drive, creating a perfect match with your initial inventory.
- An Authorized Signature: A representative from the destruction vendor must sign and date the certificate, formally attesting to the completion of the service.
This level of detail creates an unbroken chain of custody and a clean audit trail. We explore what makes a hard drive destruction certificate a powerful compliance tool in another article. This document is your concrete evidence of due diligence.
Beyond the Certificate: The Broader Compliance Picture
While the Certificate of Data Destruction is the final piece of the puzzle, it is supported by your vendor’s overall compliance framework. If you are preparing for an audit like SOC 2, you already understand the importance of thorough records. Resources like guides on Mastering SOC 2 Documentation can help illustrate how every part of your data handling process, from creation to destruction, must be defensible.
Key Insight: The Certificate of Data Destruction transforms an operational task—disposing of old hardware—into a documented, strategic risk mitigation action. It is the legal firewall that protects your Georgia business long after the shredded fragments have been recycled.
When you partner with a certified ITAD vendor like Beyond Surplus, you are not just purchasing a shredding service. You are securing a documented, compliant process that protects your brand, your customers, and your bottom line.
Sustainable E-Waste Practices After the Shred

Once your hard drives have been transformed into a pile of metal fragments, the process is not yet complete.
The subsequent handling of these materials is a true test of a company's commitment to sustainability. The final, critical step is ensuring the shredded metal and plastic are managed responsibly.
This is why choosing a vendor with a strict zero-landfill policy is essential. It guarantees that solving one problem—data security—does not create another by sending hazardous e-waste to Georgia's landfills.
From Fragments to Commodities
The pile of shredded material is not waste; it is a collection of valuable resources awaiting reclamation. A certified downstream recycling process meticulously sorts these fragments into clean commodity streams.
This high-tech process uses powerful magnets, eddy currents, and other advanced separation methods to isolate different materials. The main components recovered from hard drives include:
- Aluminum: Casings and structural parts are baled and sent to smelters.
- Steel: Dense platters and other ferrous metals are captured for reuse.
- Circuit Boards: These are processed to recover precious metals like gold, silver, and palladium.
This careful sorting transforms a data liability into raw materials, directly supporting a circular economy.
The Environmental Impact of Certified Recycling
The e-waste problem in the U.S. is significant, with Americans generating approximately 7.4 million tons annually. Hard drives are a particularly hazardous component of this waste stream, containing lead, mercury, and other toxins that require specialized handling.
After shredding, these materials are channeled back into the manufacturing economy. Steel platters, for example, have a 99% recyclability rate, and using recycled steel can reduce the demand for virgin ore mining by up to 70%. By enforcing a zero-landfill policy, we ensure this hazardous waste never pollutes Georgia's environment.
Partnering with a provider holding top-tier certifications like R2v3 or e-Stewards is your best assurance of responsible recycling. These standards mandate strict environmental controls, worker safety protocols, and a transparent chain of custody for all materials.
Key Takeaway: True IT asset disposition is a complete lifecycle management process, not just data security. Ensuring your shredded hard drives are responsibly recycled demonstrates a powerful commitment to corporate sustainability and environmental stewardship.
This final step closes the loop, proving that your Georgia business can protect its data without compromising its environmental ethics. Our comprehensive electronics recycling services in Georgia are designed to meet these high standards, providing secure and sustainable solutions for all your end-of-life IT assets.
Answering Your Hard Drive Shredding Questions
When preparing to retire IT assets, questions are expected. For businesses in Georgia, getting clear answers is crucial for making informed decisions that protect data and ensure compliance. Here are some of the most common questions from IT managers and business owners.
What’s the Typical Cost for Hard Drive Shredding in Georgia?
For smaller projects, the price for professional hard drive shredding in Georgia typically ranges from $7 to $20 per drive. For larger volumes, such as a data center decommissioning or a major office tech refresh, the per-unit cost often decreases to a more economical $5 to $10 per drive.
Several factors will influence your final quote:
- Volume of drives: Higher quantities result in a lower cost per drive.
- On-site vs. Off-site service: On-site mobile shredding is our premium service that brings the shredder to your location for maximum security and convenience, which may have a different price point than our secure plant-based service.
- Logistical details: Factors like facility accessibility or the need for our team to remove drives from machines can affect the final price.
Always request a detailed quote from a certified vendor to get a price tailored to your specific project requirements.
Do I Have to Pull the Hard Drives Out of the Computers Myself?
No, you do not have to. A full-service ITAD partner like Beyond Surplus can manage the entire process for you. Our trained technicians can safely and efficiently remove hard drives from desktops, laptops, servers, and other equipment.
While having your internal team remove the drives can sometimes reduce labor costs, outsourcing this task to our technicians is often more efficient, especially for large-scale projects. This allows your IT team to focus on core business functions rather than dismantling hundreds of computers. Be sure to mention this requirement when you request a quote.
Is Shredding a Hard Drive Actually Better Than Using Wiping Software?
For absolute, guaranteed data security, physical shredding is the superior method. It physically obliterates the drive's platters, turning them into small metal fragments. Data recovery is not just difficult; it is physically impossible. This is why organizations like the NSA and DoD mandate physical destruction and why it is the gold standard for meeting stringent compliance regulations.
Data wiping software overwrites existing data and is a suitable method for functional drives that have resale or reuse value, as it leaves the hardware intact.
For any drive at its end-of-life, especially one that contained sensitive data or is non-functional, shredding is the only method that provides 100% foolproof data destruction and complete peace of mind.
What Kind of Paperwork Should I Get After the Shredding Is Done?
Upon completion of the service, you must receive a formal Certificate of Data Destruction. This is not merely a receipt but a critical legal document. It serves as your official proof of compliance with data privacy laws and formally transfers liability for the disposed assets from your company to us.
A proper, audit-proof certificate should always include:
- The date and location of destruction.
- The specific method used (e.g., on-site shredding).
- A unique tracking serial number for the certificate.
- An authorized signature from your vendor.
For the most comprehensive and defensible audit trail, we also provide a serialized list of every hard drive destroyed. You can match this list against your internal inventory records, creating an unbroken and verifiable chain of custody.
For businesses across Georgia seeking a certified, secure, and sustainable partner for their end-of-life IT assets, Beyond Surplus offers expert guidance and a full suite of services. Contact Beyond Surplus today for certified electronics recycling and secure IT asset disposal.