For businesses across the United States, managing the disposal of outdated IT equipment is a significant operational challenge. Mail-in electronics recycling provides a streamlined, secure, and compliant solution for this critical task. This guide is designed for IT managers, facility managers, and procurement professionals seeking an efficient method for handling IT asset disposal (ITAD), especially for smaller volumes of equipment or for business locations not situated near a major recycling facility. Mail-in services transform a complex logistical problem into a straightforward, auditable process.
Why Mail-In Electronics Recycling is a Strategic Choice for Your Business
For enterprises that do not generate enough retired IT assets to warrant a full truckload pickup, a professional mail-in program is the ideal solution. It empowers IT departments and facility coordinators to dispose of retired assets according to their own schedule, eliminating the need to accumulate large quantities of equipment. This flexibility is a significant advantage for small to medium-sized businesses and corporate satellite offices.
Mail-in programs have become a primary method for collecting e-waste, particularly for high-value, portable equipment like laptops and networking gear. Businesses can ship their used devices to certified recyclers equipped to safely dismantle them and recover valuable materials. Throughout the U.S., these specialized commercial services make responsible electronics recycling accessible, even in areas with limited industrial recycling infrastructure.
To understand the scale of the e-waste challenge, Discover more insights about electronic waste projections on backthruthefuture.com.
Key Business Drivers for Adopting Mail-In Recycling Services
The strategic value of mail-in ITAD extends beyond convenience. A well-managed service enables businesses to achieve critical operational and compliance objectives.
- Data Security Compliance: Every device is meticulously tracked and processed under strict data destruction protocols. This is essential for maintaining compliance with regulations such as HIPAA, GDPR, and FACTA, which mandate the protection of sensitive information.
- Corporate Environmental Responsibility: Partnering with a certified electronics recycler ensures that your assets are processed in an environmentally sound manner. This supports corporate sustainability goals and provides the necessary documentation for environmental reporting and compliance.
- Efficient Resource Allocation: Outsourcing the disposal of smaller batches of IT assets allows internal teams to focus on core business functions instead of navigating the complexities of e-waste logistics and compliance.
Verifiable Chain of Custody for Total Peace of Mind
A primary benefit of a structured mail-in program is the creation of a clear, auditable chain of custody. From the initial request for a shipping label to the final receipt of a certificate of destruction, every stage is documented.
This verifiable trail is indispensable for internal audits and for demonstrating regulatory compliance. Ultimately, leveraging a reputable service for your company's IT equipment recycling provides documented assurance that your assets were managed responsibly.
Securing Corporate Data Before Shipment
Before any IT asset leaves your facility, ensuring complete data sanitization is not just a best practice—it is a mandatory security protocol for any business. Standard deletion or a basic reformat of a storage drive is insufficient, as residual data can often be recovered, posing a significant security risk. For organizations handling sensitive client, financial, or proprietary information, the consequences of a data breach from a improperly disposed device can be catastrophic.
The foundational step in any secure mail-in electronics recycling process is a robust data sanitization plan. Before equipment is packaged for shipment, it is critical to implement comprehensive data security management practices to mitigate potential breaches. This professional approach safeguards your organization from the moment a device is decommissioned until you receive a final Certificate of Data Destruction.
Software Wiping Versus Physical Destruction for Commercial Assets
When sanitizing data-bearing assets, businesses have two primary methods. Understanding the appropriate application of each is key to balancing security requirements with potential value recovery.
Software Wiping: This process utilizes specialized software to overwrite the entire surface of a hard drive or solid-state drive (SSD) with random data, rendering the original information unrecoverable.
- Best For: Newer, functional devices that retain commercial value and are suitable for refurbishment and resale. Wiping preserves the hardware's integrity while guaranteeing data erasure.
- Compliance: Professional services must use methods compliant with recognized standards like DoD 5220.22-M or NIST 800-88 Clear/Purge, which are the industry benchmarks for secure data erasure.
Physical Destruction: This method involves the complete physical obliteration of the storage media through shredding, crushing, or degaussing.
- Best For: End-of-life or non-functional drives, or media containing highly sensitive data where no risk is acceptable.
- Guaranteed Security: Physical destruction offers absolute assurance. Data cannot be recovered from media that has been physically destroyed.
Beyond Surplus offers comprehensive services that align with these industry-best practices for business data destruction.
A critical oversight in corporate IT asset disposal is assuming a non-functional device poses no data risk. A laptop that fails to power on may still contain a fully intact hard drive with sensitive corporate data. Professional data destruction is a non-negotiable step for every asset, regardless of its operational status.
Creating a Verifiable Asset Inventory
A detailed inventory is a fundamental component of your risk management and compliance strategy. Before packaging any electronics, create a manifest that tracks critical details for each asset.
Your inventory log should capture:
- Asset Type: (e.g., Laptop, Server, HDD)
- Manufacturer and Model: (e.g., Dell Latitude 7420)
- Serial Number: The unique identifier for precise tracking.
- Corporate Asset Tag: Your internal tracking number.
- Condition: (e.g., Functional, Damaged, End-of-Life)
This manifest serves as your internal record and is used to verify against the Certificate of Data Destruction provided by your recycling partner. This documentation creates an unbroken chain of custody, providing auditable proof that every data-bearing device was managed and sanitized according to your corporate policy.
Proper Packaging and Shipping of Commercial IT Assets
The methodology for packaging retired electronics is as critical as the data sanitization process. Secure packaging prevents physical damage during transit, which is essential for protecting any potential resale value and ensuring components arrive intact for secure processing. Improper packaging can lead to shipment rejection by the carrier or damage that complicates the data destruction and recycling chain of custody.
The process begins with appropriate materials. Utilize new, double-walled corrugated cardboard boxes capable of supporting the weight of your IT equipment. Maintain a minimum of two inches of clearance on all sides of each device to allow for adequate cushioning.
This flowchart outlines the essential steps for maintaining security from your facility to the recycling partner.
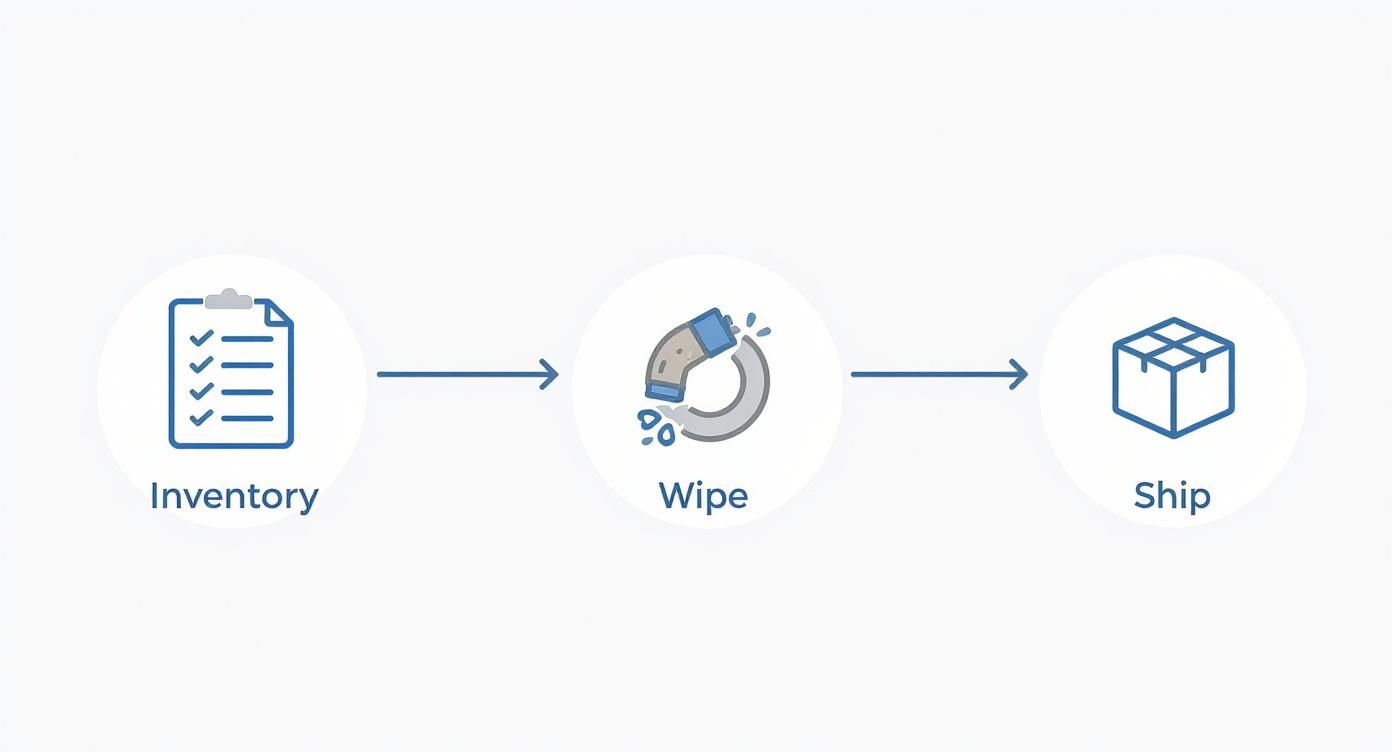
As illustrated, secure shipping is the final critical phase following inventory creation and data wiping.
Handling Sensitive Components and Batteries for Commercial Shipment
Individual components such as server memory (RAM) and processors are highly susceptible to electrostatic discharge (ESD). A minor static shock can destroy these components, eliminating their value. Always place such items in anti-static bags before packaging. This simple, low-cost step protects the value of assets intended for reuse.
Lithium-ion batteries, present in nearly all corporate laptops, tablets, and smartphones, are classified as dangerous goods by shipping carriers due to fire risk. They require specific handling.
- Mandatory Labeling: Any package containing these devices must be clearly marked with a lithium battery handling label, often referred to as the UN3481 warning label.
- Carrier Compliance: Failure to apply this label will likely result in shipment rejection by carriers like FedEx, UPS, or USPS.
- Damage Prevention: It is recommended to keep batteries inside their host devices. Shipping loose batteries is a more complex process that requires specialized packaging and prior consultation with both your recycling partner and the carrier.
To assist your business in executing this correctly, we have developed a concise checklist. Adhering to these steps ensures your electronics are packed securely and meet all shipping regulations.
Packaging Checklist for Commercial IT Asset Shipment
| Checklist Item | Action Required | Importance for Businesses |
|---|---|---|
| Box Selection | Use new, double-walled corrugated cardboard boxes. | Prevents crushing and supports the weight of dense IT equipment. |
| Cushioning Space | Leave at least 2 inches of space on all sides of each item. | Allows for sufficient padding to absorb shocks during transit. |
| Component Protection | Place loose RAM, CPUs, and circuit boards in anti-static bags. | Protects sensitive electronics from electrostatic discharge (ESD) damage. |
| Battery Labeling | Apply the UN3481 lithium battery label to the outside of the box. | Mandatory for carrier compliance and alerts handlers to hazardous materials. |
| Internal Padding | Wrap each item individually in bubble wrap. | Prevents assets from scratching or impacting one another. |
| Void Fill | Fill all empty space with packing peanuts, air pillows, or paper. | Immobilizes contents to prevent shifting and potential damage. |
| Secure Sealing | Use high-quality packing tape to seal all seams and corners. | Reinforces the box's structural integrity and prevents accidental opening. |
| Label Placement | Attach the provided shipping label securely to the top of the box. | Ensures accurate tracking and delivery to the certified recycling facility. |
By following this checklist, you are not merely packing a box; you are preserving the chain of custody and protecting your corporate assets until they are securely processed.
Best Practices for Secure Cushioning and Shipping
After selecting a sturdy box and addressing battery compliance, the final step is to cushion and seal the package correctly. Wrap each device individually in bubble wrap. Fill all remaining empty space with packing peanuts, crumpled paper, or air pillows. The objective is zero movement within the box. If you can hear contents shifting, add more filler material.
Improper cushioning is a common and costly mistake. A shipment of loose hard drives without padding arrived at a facility with several drives physically cracked. This represents not only a loss of asset value but also a significant data security risk. Proper cushioning is the most effective and affordable insurance policy.
Cost management is also a factor in business logistics. Understanding the cheapest way to send your parcels can contribute to overall cost-effectiveness.
Finally, seal the box securely with high-quality packing tape, reinforcing all seams. Affix the shipping label provided by your mail-in electronics recycling partner. This label contains the tracking information needed to monitor the shipment and receive delivery confirmation, closing the loop on your end of the secure chain of custody.
What Happens After Your Business Electronics Arrive
Upon arrival at the certified recycling facility, your shipment undergoes a highly controlled, secure, and transparent process designed to protect corporate data and maximize material recovery. This is the final, critical stage of the mail-in electronics recycling process, where your retired assets are responsibly managed.

The moment your shipment is received, it is checked into a secure inventory management system. The chain of custody initiated by your business is formally continued, with each asset logged by its serial number against your shipping manifest. This meticulous tracking ensures complete accountability.
The Data Destruction Phase
Before any physical processing, the primary focus is data security. All devices capable of storing information—including hard drives, SSDs, and smartphones—are immediately segregated for sanitization.
Based on your service agreement and the asset type, one of two paths is followed:
- Secure Wiping: Using specialized software that adheres to NIST 800-88 standards, all data is completely overwritten. This is the preferred option for functional drives with resale potential, as it preserves the hardware.
- Physical Destruction: The storage device is fed into an industrial shredder, which grinds it into small fragments, guaranteeing that the data is 100% irrecoverable. This is the ultimate security measure for end-of-life media or drives that contained highly sensitive corporate data.
This step is methodically executed and documented. The serial number of every drive that is wiped or destroyed is recorded for inclusion in your final compliance reports.
Dismantling and Material Recovery
With all data security protocols completed, the focus shifts to de-manufacturing. This is a systematic disassembly process where technicians manually dismantle each device.
This manual approach is crucial due to the complex mix of materials in electronics. Circuit boards are separated for the recovery of precious metals like gold, silver, and copper. Aluminum casings, steel frames, plastic components, and wiring are sorted into distinct commodity streams for further processing.
Simultaneously, hazardous components such as mercury-containing lamps from older monitors and leaded glass are safely removed and managed in accordance with strict environmental regulations.
The value of a certified recycler lies in their ability to maximize resource recovery while minimizing environmental impact. They convert obsolete equipment into a valuable stream of commodities, ensuring that hazardous materials are diverted from landfills.
This responsible processing is more critical than ever. In 2022, global e-waste generation reached 62 million tonnes, an 82% increase since 2010. With recycling rates lagging, maximizing resource recovery is an environmental imperative.
Your Final Proof of Compliance
The process concludes with the issuance of official documentation, which serves as your legal proof of proper disposal. Your business will receive two key documents:
- Certificate of Data Destruction: This report lists the serial numbers of all data-bearing devices that were sanitized, detailing the specific method used (wiping or shredding).
- Certificate of Recycling: This document certifies that all non-hazardous electronic assets were processed in an environmentally responsible manner, in compliance with all local, state, and federal laws.
These certificates transfer liability from your company to the recycler and provide the auditable documentation required for internal controls and regulatory compliance. For a more detailed overview, explore our guide on what happens to IT equipment after disposal.
Common Questions About Business E-Waste Recycling
For IT managers and procurement professionals considering a mail-in electronics recycling program, questions about security, logistics, and compliance are paramount. Here are answers to the most frequent inquiries from our business clients.
Is Mail-In Recycling Truly Secure for Sensitive Corporate Data?
Yes, provided you partner with a certified electronics recycler. The security of a mail-in program is entirely dependent on the vendor's credentials and documented processes. A provider holding an R2v3 or e-Stewards certification is bound by strict, externally audited standards for data security and chain of custody.
These certified partners utilize data destruction methods that align with NIST 800-88 guidelines, the federal standard for media sanitization. Upon completion, you receive a serialized Certificate of Data Destruction, which serves as your official, auditable proof that all sensitive corporate information has been permanently destroyed.
What Types of Electronics Can Our Business Mail In?
Mail-in programs are specifically designed for smaller, high-density IT assets suitable for box shipment. This service is ideal for corporate equipment such as:
- Laptops, tablets, and smartphones
- Loose hard drives (HDDs) and solid-state drives (SSDs)
- Networking equipment like switches, routers, and firewalls
- Server components including RAM, CPUs, and power supplies
Conversely, mail-in solutions are not practical for large, heavy, or bulky items. Equipment such as full-size server racks, large multifunction office printers, or specialized laboratory and medical equipment require a scheduled freight pickup service.
What Are the Typical Costs for a Business Mail-In Service?
The cost structure for commercial mail-in electronics recycling varies among providers. Some vendors may offer the service at no charge if the assets have sufficient resale value to cover processing costs, which is common for newer laptops or enterprise-grade networking gear.
Other providers may charge based on total weight, the number of boxes, or for specific services like certified data destruction. It is essential to request a detailed, transparent quote that itemizes all potential fees—including shipping, processing, data destruction, and documentation—to avoid unexpected costs.
The primary consideration should extend beyond the initial price. A fee from a certified recycler includes documented compliance and risk mitigation, which is invaluable for protecting your company from the severe financial and reputational damage of a data breach.
How Do We Prove Compliance After Disposal?
Proof of compliance is provided through the official documentation issued by your recycling partner. These reports are the final, essential step in a defensible IT asset disposal process.
Your business should always receive two critical documents:
- A Certificate of Recycling: This confirms that your electronic assets were processed in an environmentally compliant manner, adhering to all relevant regulations.
- A Certificate of Data Destruction: This is your security assurance. It must list the serial numbers of all data-bearing devices and specify the sanitization method used, whether software wiping or physical shredding.
These certificates are non-negotiable for internal audits and demonstrating regulatory compliance. For additional information, please visit our comprehensive electronics recycling FAQ page.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal services designed for your business. Schedule a pickup or request a quote today.