For businesses across Georgia, secure computer disposal isn't just an item on a checklist; it's a critical security function. When retiring IT assets like servers, laptops, and desktops are improperly discarded, your organization is exposed to devastating data breaches, steep regulatory fines, and permanent damage to your corporate reputation. A single misplaced hard drive can be all a malicious actor needs to access sensitive client information, proprietary data, and financial records. This guide is for IT managers, facility managers, and business owners in Georgia seeking a compliant solution.
The Business Risks of Improper Computer Disposal in Georgia
When your Georgia business executes a technology refresh, the outgoing equipment doesn’t simply disappear. Those retired assets are liabilities in waiting, loaded with confidential data that can create massive financial and legal exposure if handled incorrectly by non-commercial recyclers.
A common mistake for businesses is underestimating data persistence. Simply deleting files or performing a factory reset is insufficient for enterprise security. With today’s specialized software, information can easily be recovered from devices that haven't been professionally sanitized or physically destroyed.

The fallout extends beyond data security. Since Georgia lacks a formal statewide e-waste program for businesses, the responsibility to act ethically and legally falls squarely on your company. Disposing of old electronics in a dumpster is not only environmentally irresponsible due to toxic materials like lead and mercury—it can also place your business in violation of local ordinances and federal regulations.
Financial and Reputational Damage
The consequences of a data breach originating from discarded IT assets are complex and expensive. Fines from regulatory bodies like the FTC can be substantial, particularly for violating regulations protecting consumer information. However, the impact on your reputation can be even more damaging.
A public data breach shatters customer trust, harms your brand's credibility, and can lead to significant loss of business. The narrative of a company failing to protect its clients' data can persist for years, making it harder to secure new partnerships and sales. Exploring the link between retired equipment and security incidents reveals the high stakes of data breaches from improper equipment disposal.
A recent study found the average cost of a data breach for a U.S. business is over $9.4 million. Much of this cost stems not from the initial incident response, but from long-term reputation damage and lost business.
Compliance and Legal Headaches
For businesses in regulated industries such as healthcare (HIPAA) or finance (GLBA), the rules for secure data disposal are even more stringent. Failure to comply can lead to severe penalties, legal battles, and mandatory public disclosures.
These regulations require businesses to take "reasonable measures" to destroy sensitive information. This is a standard that a certified IT Asset Disposition (ITAD) partner is specifically equipped to meet—and document. That documentation, such as a Certificate of Data Destruction, serves as your legal proof of compliance, effectively transferring liability and shielding your organization from future claims.
Understanding Georgia’s Data Disposal Compliance for Businesses
For businesses in Georgia, navigating the regulations for secure computer disposal can be challenging. This is primarily because Georgia does not have a specific e-waste law dictating how companies must handle retired electronics. This places the full weight of compliance on your organization, making it absolutely critical to adhere to applicable federal laws.
Believing that hitting 'delete' or performing a factory reset is sufficient is a common and dangerous misconception for any commercial entity. Data recovery software can easily retrieve information from drives that have not been professionally wiped or physically destroyed. When dealing with sensitive customer, patient, or financial data, federal regulators do not consider "deleted" to be secure.
Your responsibility for that data does not end when a device is unplugged. It concludes only once that device is verifiably and permanently destroyed.
Key Federal Regulations for Businesses
Regardless of your location in Georgia, several major federal laws dictate how your business must handle sensitive information. These are not mere suggestions—they are legally binding, and non-compliance can lead to serious penalties.
- The FTC Disposal Rule: This applies to nearly every business and requires you to take "reasonable measures" to protect consumer information from unauthorized access during its disposal.
- HIPAA (Health Insurance Portability and Accountability Act): Any entity in the healthcare sector, from a small clinic to a large hospital system, must adhere to HIPAA's strict privacy and security rules. This includes the secure, permanent destruction of Protected Health Information (PHI) on any electronic device.
- GLBA (Gramm-Leach-Bliley Act): This regulation is for financial institutions. Banks, investment firms, and insurance companies must comply with GLBA, which requires protecting nonpublic personal information (NPI) throughout its entire lifecycle—including disposal.
Together, these laws make professional, certified IT asset disposal a fundamental component of any corporate risk management strategy.
The core principle behind all these regulations is straightforward: you, the data owner, are liable until you can prove that data has been permanently and irreversibly destroyed. An audit trail is your only valid defense, and that is precisely what a certified ITAD partner provides.
The demand for compliant disposal services is growing rapidly. While Georgia lacks a formal e-waste program, its status as a major data center hub means a massive volume of IT equipment is being retired constantly. This makes certified data destruction following standards like NIST 800-88 a non-negotiable practice for avoiding breaches and crippling fines.
The Role of a Certificate of Data Destruction
How do you prove your business has met its legal obligations? An invoice from a recycler is insufficient. You require a Certificate of Data Destruction.
This is the critical legal document that serves as your official record of compliant disposal. It details the specific methods used (e.g., shredding, wiping), lists the serial numbers of the destroyed devices, and, most importantly, formally transfers liability from your company to the disposal vendor.
Without this certificate, your business has no verifiable proof that it took the required steps to protect sensitive data. This leaves your organization completely exposed in an audit or a data breach investigation. This documentation is the cornerstone of any sound strategy for compliant IT disposal in Georgia.
Choosing the Right Data Destruction Method for Your Business
When it is time to retire your company's IT assets, you face a critical decision: how do you ensure the sensitive corporate data on them is permanently eliminated? For enterprise purposes, there are two gold-standard options for this final step: certified data wiping and physical hard drive shredding.
The optimal choice is not always the most obvious. It depends on your specific business scenario—including the age and condition of the equipment, your internal security policies, and whether those assets retain residual resale value. Making the correct decision here is a cornerstone of any secure computer disposal strategy for a Georgia business.
When to Choose Certified Data Wiping
Certified data wiping, known in the industry as sanitization, uses specialized software to completely overwrite a hard drive with random data. This process adheres to strict protocols like the NIST 800-88 standard, rendering the original information completely unrecoverable. It is a forensic-level digital cleansing.
This method makes the most sense for your business when:
- You have newer, high-value equipment. If you are retiring servers, laptops, or networking gear that is only a few years old, they likely have significant resale value. Wiping allows you to securely prepare these devices for the secondary market, potentially turning a disposal cost into a revenue stream.
- You're returning leased equipment. Most corporate leasing agreements require devices to be returned in working order, with all company data scrubbed. Wiping is ideal for this, as it satisfies the terms without physically damaging the hardware.
- You plan to redeploy assets internally. For larger companies, wiping is a safe and efficient method to repurpose computers for other employees or departments without risk of data cross-contamination.
When Physical Shredding Is the Better Option
In some cases, absolute certainty is required. Physical hard drive shredding is precisely what it sounds like. We feed hard drives, SSDs, backup tapes, and other media into an industrial shredder that grinds them into small, confetti-like fragments. At this point, data recovery is physically impossible.
Your business should choose shredding in these scenarios:
- Your assets are at the true end of their life. For obsolete desktops or non-functional equipment with no resale value, shredding is the most direct and foolproof method to eliminate data risk.
- Your internal policy mandates it. Many organizations, particularly in highly regulated sectors like finance, healthcare, or government contracting, have strict protocols that mandate physical destruction without exception.
- You're disposing of proprietary tech or prototypes. If your R&D firm or manufacturing company is retiring devices containing trade secrets or invaluable intellectual property, shredding provides undeniable proof of destruction.
The diagram below illustrates how this choice fits into the broader compliance framework, from understanding regulations to executing the disposal and obtaining the critical audit trail.
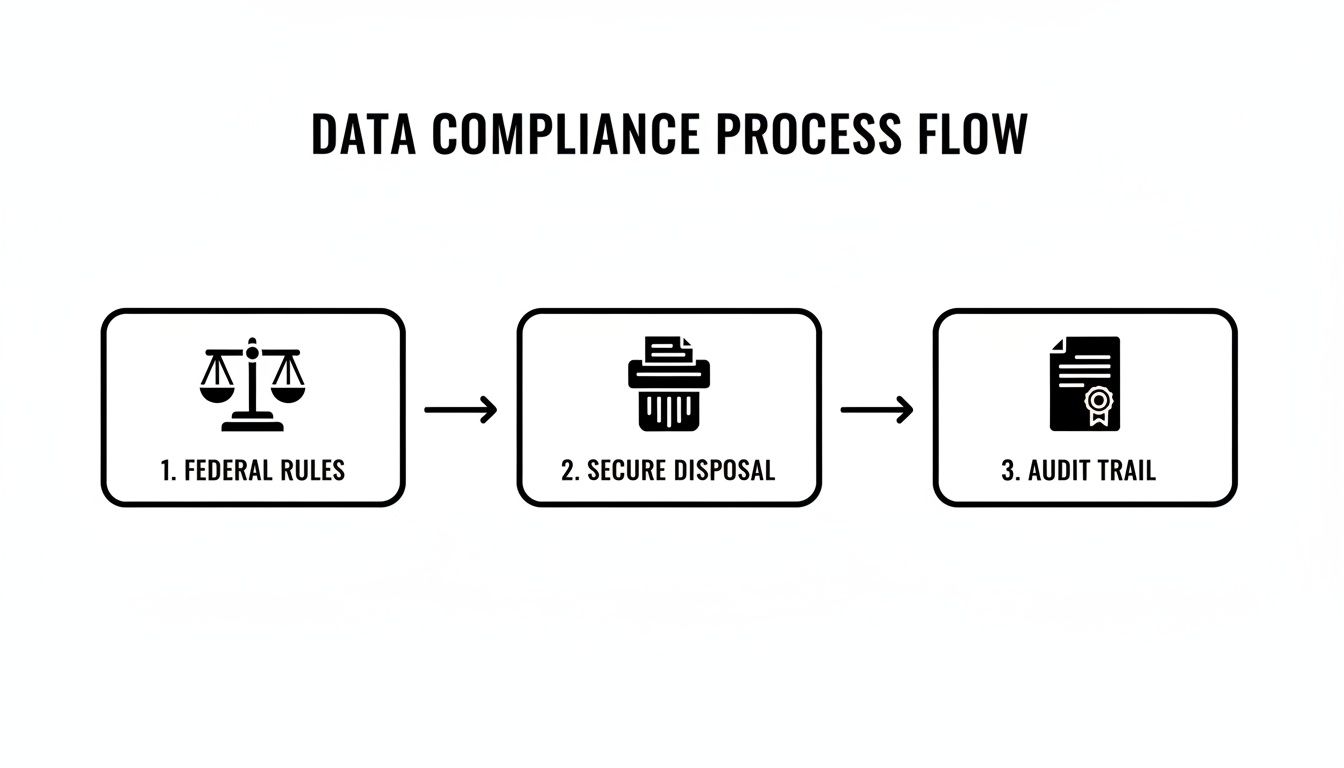
This workflow highlights how selecting the correct destruction method is a key component of a larger compliance strategy that protects your organization.
On-Site Shredding vs. Data Wiping: A Comparison
To clarify the decision, it is helpful to compare the two primary methods side-by-side. Each has a specific application, and understanding the trade-offs is key to aligning the right service with the right assets.
| Feature | On-Site Hard Drive Shredding | Certified Data Wiping (Sanitization) |
|---|---|---|
| Security Level | Absolute. Physical destruction makes data recovery impossible. | Very High. Meets NIST 800-88 standards, making data forensically unrecoverable. |
| Asset Value | Destroys any resale or reuse value of the hard drive. | Preserves the hardware, allowing for remarketing, donation, or redeployment. |
| Best For | Outdated, non-functional, or low-value assets. Required by strict compliance policies. | Newer, functional, and high-value equipment. Leased assets needing return. |
| Verification | Visual confirmation and a Certificate of Destruction. | A certified report and Certificate of Sanitization for each serial number. |
| Cost | Typically priced per drive or by weight. Can be very cost-effective for bulk disposals. | Often priced per device. The cost can be offset by the resale value recovered. |
Ultimately, whether you shred or wipe, the objective is the same: secure, compliant data destruction. There is no single "best" answer, only the one that best fits your equipment, budget, and risk tolerance.
Both wiping and shredding are valid, secure methods. The key is to align your choice with your operational needs and risk management strategy. You can learn more about the technical details by exploring professional security and data destruction services. A qualified ITAD partner can conduct an inventory assessment and recommend the most appropriate and cost-effective path forward for every asset.
Why Chain of Custody Documentation Matters for Your Business
When your Georgia business transfers retired IT equipment for disposal, the process is not complete. For risk management purposes, the most critical phase has just begun.
The term chain of custody refers to the chronological documentation trail that records every touchpoint for your equipment—from the moment it leaves your facility to its final destruction. This should be viewed not as simple record-keeping, but as your primary defense in a compliance audit.
Consider a financial firm in Atlanta undergoing a GLBA audit. Regulators will not just ask if old servers were disposed of; they will demand irrefutable proof of how. Without a detailed, unbroken chain of custody, the firm cannot prove it met its legal duties, leaving it exposed to serious penalties. This documentation is what officially transfers liability from your organization to your ITAD partner.

Essential Documents for Your Audit Trail
A legitimate, commercial ITAD process generates specific, legally sound documents. A simple invoice is insufficient. To be fully audit-proof, your final documentation package must include several key components.
You should always expect to receive these three documents:
- A Serialized Asset Report: This is a detailed inventory listing every single device by its unique serial number, model, and any internal asset tags. It functions as the master list, confirming precisely what your partner received and processed.
- A Certificate of Data Destruction: This is the most crucial document. It certifies that every data-bearing device was destroyed according to specific standards (like NIST 800-88), lists the serial numbers of the shredded or wiped devices, and legally confirms that the data is permanently gone.
- A Certificate of Recycling: This document confirms that all non-data-bearing materials and shredded remnants were processed and recycled in an environmentally responsible manner, adhering to a zero-landfill policy.
These documents work together to create a complete, unbroken record. They prove your company performed its due diligence, protecting your organization long after the equipment has been retired. You can see a detailed example of a proper hard drive destruction certificate in our comprehensive guide.
The Bigger Picture of E-Waste and Liability
The need for this level of detail is driven by the sheer scale of the e-waste problem. Globally, e-waste is the fastest-growing waste stream. Over 50 million metric tons are generated annually—equivalent to discarding 1,000 laptops every second.
With Georgia's status as a major national data center hub, the volume of retired IT hardware originating from our state is immense, making secure and documented disposal absolutely essential for businesses.
For any Georgia business managing computer disposal, remember this principle: if it isn't documented, it didn't happen. A complete chain of custody is not a "nice-to-have"—it is the only verifiable proof that you have fulfilled your legal and ethical obligations.
How to Select a Certified ITAD Partner in Georgia
Choosing the right IT Asset Disposition (ITAD) provider is more than finding a vendor to haul away old technology; it is a critical security decision. For any Georgia business, this partner becomes an extension of your compliance and risk management team. The wrong choice can lead to devastating data breaches and environmental liabilities, while the right one protects your brand and your bottom line.
When vetting a potential partner, look beyond a simple price list. Your evaluation should begin with their credentials. Non-negotiable qualifications include certifications like R2v3 (Responsible Recycling) or e-Stewards. These are not just logos on a website; they are hard-earned proof that a provider adheres to the highest industry standards for data security, environmental responsibility, and worker safety.
Look for Industry-Specific Experience
A provider's experience should align with your industry's unique compliance challenges. A partner that regularly works with healthcare facilities in Atlanta, for instance, will possess a deep, practical understanding of HIPAA's stringent requirements for disposing of devices containing Protected Health Information (PHI). They will know the process inside and out.
Likewise, a vendor who primarily serves financial institutions will be an expert in GLBA compliance.
Do not hesitate to ask for case studies or references from businesses in your sector. This is the best way to confirm their capability to manage the specific data risks and documentation requirements your company faces.
Prioritize a Zero-Landfill Policy and Value Recovery
True environmental stewardship is a commitment, not a buzzword. Look for a partner with a strict zero-landfill policy. This guarantees that every component of your retired assets is either recycled or responsibly repurposed, preventing hazardous materials from contaminating Georgia's environment.
Additionally, a top-tier ITAD partner should offer robust value recovery services. Through an IT asset buyback program, functional equipment can be securely refurbished and remarketed. This generates a return that can significantly offset—or even completely eliminate—your disposal costs. It transforms a necessary expense into a smart financial decision.
The global e-waste crisis is staggering. In 2022, the world produced 61.9 million metric tonnes of electronic waste, with only 22.3% properly recycled. This issue is particularly acute here in Georgia, where Atlanta’s data center boom is accelerating hardware refresh cycles and creating mountains of retired IT gear filled with sensitive data. Discover more insights about data center equipment recycling in Georgia.
Ultimately, your goal is to find a partner who does more than just schedule a pickup. You need a provider who offers peace of mind through a secure, transparent, and fully documented process. By focusing on certifications, relevant experience, and a genuine commitment to both environmental and financial sustainability, you can select a partner that truly protects your organization.
You can explore the full range of professional ITAD services in Georgia to understand how a certified partner can safeguard your business.
Common Questions About Computer Disposal for Businesses in Georgia
Even with a solid plan, businesses in Georgia often have questions regarding the logistics of secure computer disposal. The costs, services, and processes can seem complex, but working with a certified ITAD partner makes the entire process straightforward and secure.
Here are a few of the most common questions we receive from corporate clients.
What Does Secure Computer Disposal Typically Cost a Georgia Business?
This is often the first question, and the answer depends on several factors. The final cost is influenced by the volume of equipment, the chosen data destruction method (shredding vs. wiping), and any logistical requirements like on-site service or de-installation.
However, the key factor many businesses overlook is value recovery.
If your retired equipment is relatively modern and functional, it may be eligible for an IT asset buyback program. The revenue recovered from reselling these assets can often reduce or even completely cover your disposal costs. What begins as a perceived expense can result in a net return to your company. The only way to determine the final cost is to request a custom quote based on your specific inventory.
Should Our Business Wipe Hard Drives Before an ITAD Provider Arrives?
While this is a sound internal security practice, it is not necessary when you engage a certified ITAD vendor. A professional provider guarantees complete data destruction as a core part of their service.
Your partner will use either physical shredding or NIST 800-88 compliant data wiping to ensure all information is permanently destroyed. This entire process is tracked and formally documented with a Certificate of Data Destruction.
This certificate is your most important deliverable. It is the legal document that officially transfers liability for the data from your company to the disposal vendor, providing a clear, audit-proof record that you have met your compliance obligations.
Can You Manage a Complete Data Center Decommissioning in Atlanta?
Yes. Full-service ITAD companies specialize in large-scale, complex projects like data center decommissioning. This is not a simple pickup; it is a meticulously planned, end-to-end service designed to manage every detail.
A typical decommissioning project includes:
- Project Management: Coordinating all timelines and logistics to ensure minimal disruption to your operations.
- On-Site De-installation: Safely disconnecting and removing all servers, racks, switches, and cabling.
- Serialized Asset Tracking: Creating a detailed manifest of every piece of equipment from the point of collection.
- Certified Data Destruction: Securely shredding or wiping all hard drives, SSDs, and other storage media on-site or at a secure facility.
- Responsible Recycling: Ensuring all non-reusable materials are processed in an environmentally compliant manner.
A qualified partner handles every detail, making the entire process secure, efficient, and fully documented.
What Kind of Proof Will My Business Receive After the Service?
Once your IT assets are processed, you should expect a comprehensive documentation package. This is not just a receipt; it is your permanent compliance record and is non-negotiable for proving you have met your legal obligations.
This package must include three key documents: a serialized inventory of all assets processed, a Certificate of Recycling to confirm proper environmental handling, and a Certificate of Data Destruction. Together, these documents provide definitive proof of compliance with federal regulations like HIPAA, GLBA, and the FTC Disposal Rule.
For a professional and secure approach to managing your company's retired IT assets, trust Beyond Surplus. We provide certified, compliant, and transparent electronics recycling and secure data destruction services for businesses across Georgia and nationwide. Contact us today for a custom quote.