For businesses in Atlanta, GA, accumulating obsolete IT assets poses a significant risk far beyond taking up valuable storage space—it’s the sensitive corporate, financial, and customer data they retain. Professional shredding and recycling services in Atlanta provide the essential solution to neutralize this threat, ensuring both data security and environmental compliance for your enterprise.
This process combines the absolute security of physical data destruction with the environmental responsibility of certified electronics disposal. It is the cornerstone of any modern IT Asset Disposition (ITAD) strategy for Atlanta businesses looking to safeguard their operations and reputation.
Protecting Your Business with a Two-Step Strategy
For any Atlanta organization, disposing of obsolete technology presents a dual challenge: you must protect confidential information and adhere to strict environmental regulations. Failure on either front can lead to severe consequences, including costly data breaches, substantial fines, and lasting damage to your company’s reputation.
This is where a structured approach to IT equipment disposal becomes a strategic necessity. It’s not merely about discarding old equipment; it’s a methodical process designed to protect and preserve your business from potential liabilities.
This combined strategy addresses the entire lifecycle of retiring IT assets, ensuring security and sustainability are managed in tandem. The process is straightforward but critical for commercial clients:
- Step One: Secure Data Destruction. This is the first and most crucial step. It involves the complete, irreversible destruction of all data-bearing devices. We’re talking about industrial-grade shredding that physically pulverizes hard drives, SSDs, servers, and other media into small, unsalvageable fragments.
- Step Two: Responsible Electronics Recycling. After all data is verifiably destroyed, the remaining electronic components—metals, plastics, and circuit boards—are processed for responsible recycling. This prevents hazardous e-waste from entering landfills and allows valuable raw materials to be recovered and reused in the manufacturing supply chain.

This approach guarantees that no sensitive information can ever be recovered, while simultaneously helping your business meet its corporate sustainability goals. The growing focus on secure data management has fueled significant growth in the professional destruction industry.
In fact, market analysis shows the paper shredding services market jumped from $2,060.55 million in 2021 to an estimated $2,543 million by 2025. North America is leading this charge. This trend highlights a clear understanding among businesses: certified destruction is a non-negotiable part of modern operations. You can learn more about these market trends and the growth of secure disposal services.
Ultimately, integrating professional shredding and recycling into your ITAD policy is the only way to create a secure, auditable, and compliant end-of-life process for your company’s technology assets in Atlanta, GA.
Why Shredding is the Ultimate Data Security for Businesses
Think of software-based data wiping like erasing a whiteboard. It might appear clean, but with the right forensic tools, faint traces of what was written can often be recovered. Now, imagine taking that same whiteboard and feeding it into an industrial shredder. There is nothing left to recover. Period.
That’s the fundamental difference between data sanitization software and physical shredding and recycling. When your business requires absolute, verifiable certainty that sensitive information is permanently destroyed, shredding is the gold standard. It’s your ultimate defense against a data breach long after an asset has left your facility.
The Limits of Wiping vs. the Finality of Shredding
Data wiping software is designed to overwrite existing information with random characters. While it can be effective on a perfectly healthy drive, in a real-world commercial environment filled with aging and diverse IT assets, “perfect” is rarely achievable.
Wiping has several critical blind spots for enterprise IT:
- Failure on Damaged Drives: If a hard drive has bad sectors or physical damage, wiping software can fail, leaving behind recoverable fragments of your most sensitive data.
- Ineffectiveness on SSDs: Modern solid-state drives (SSDs) use wear-leveling technology that distributes data across memory cells. This makes it incredibly difficult for software to guarantee it has overwritten every single data block.
- Lack of Absolute Proof: Wiping software generates digital logs, but this does not offer the same tangible, witnessed proof of destruction that comes from watching a hard drive turn into a pile of metal fragments.
Physical destruction is the only method the National Security Agency (NSA) recognizes as sufficient for eliminating top-secret data. If it’s the standard for national security, it should be the standard for protecting your company’s critical business data.
Shredding completely sidesteps these issues. It doesn’t matter if a drive is damaged or uses complex flash memory. The process simply reduces the physical device to tiny, useless pieces, making data recovery impossible.
Want to dive deeper into the mechanics? Check out our complete guide on everything you need to know about hard drive shredding.
On-Site vs. Off-Site Shredding: Choosing the Right Service for Your Business
Once you’ve decided to shred, the next question is where it happens. You can have it done at your facility (on-site) or have the assets securely transported to a specialized plant (off-site). Both are highly secure options, but they serve different needs based on your organization’s compliance requirements, budget, and operational preferences.
Making the right choice is about aligning the service with your internal security protocols. While the concept is simple, the demand for verifiable destruction has created a huge market. For context, the global market for paper shredders—a similar industry focused on physical destruction—was valued at USD 2.69 billion in 2025 and is expected to hit USD 4.25 billion by 2032. This shows a universal business need for proof of destruction that’s just as critical in IT asset disposal.
Here’s a head-to-head comparison to help you decide which approach fits your organization best.
On-Site vs Off-Site Shredding for IT Assets
This table breaks down the key differences between mobile shredding at your location and plant-based shredding at a secure facility.
| Feature | On-Site Shredding | Off-Site Shredding |
|---|---|---|
| Process | A specialized truck with an industrial shredder arrives at your facility. Assets are destroyed on-premise while you witness the process. | Assets are placed in locked containers and securely transported to a certified facility for destruction under constant camera surveillance. |
| Security | The absolute highest level of witnessed security. You can physically observe your assets being destroyed, ensuring a completely unbroken chain of custody. | Very high security. Involves GPS-tracked transport, access-controlled facilities, and fully audited processes. You receive a Certificate of Destruction as proof. |
| Best For | Organizations with the strictest compliance needs (like healthcare or finance) or any company whose internal policies demand witnessed destruction. | Businesses looking for a cost-effective and highly secure solution that can efficiently handle large volumes of IT assets without disrupting operations. |
| Logistics | Requires scheduling in advance and having a designated, safe area for the shredding truck to park and operate. | Much simpler logistics. Just schedule a secure pickup, and the vendor takes care of all the downstream processing and destruction at their plant. |
Ultimately, whether you choose on-site or off-site services, professional shredding provides a level of data security that software solutions cannot promise. It is the definitive final chapter for your IT assets, ensuring that retired technology never becomes a future liability.
The Journey of Your Recycled IT Equipment
Once your hard drives and other data-bearing devices have been physically shredded, the data is gone forever. But what happens to the resulting pile of metal, plastic, and glass fragments? This is where the next critical phase begins. The leftover material embarks on a complex journey through a responsible recycling stream, shifting the focus from data security to environmental sustainability.
This is why partnering with a certified e-waste recycler with a zero-landfill policy is paramount. Their role isn’t just to make things disappear; it’s to meticulously disassemble and recover every possible component. This detailed process ensures valuable materials are reclaimed while hazardous substances are managed safely and in accordance with all regulations.
This infographic breaks down the basic flow of how your shredded e-waste is sorted and prepared for reuse.
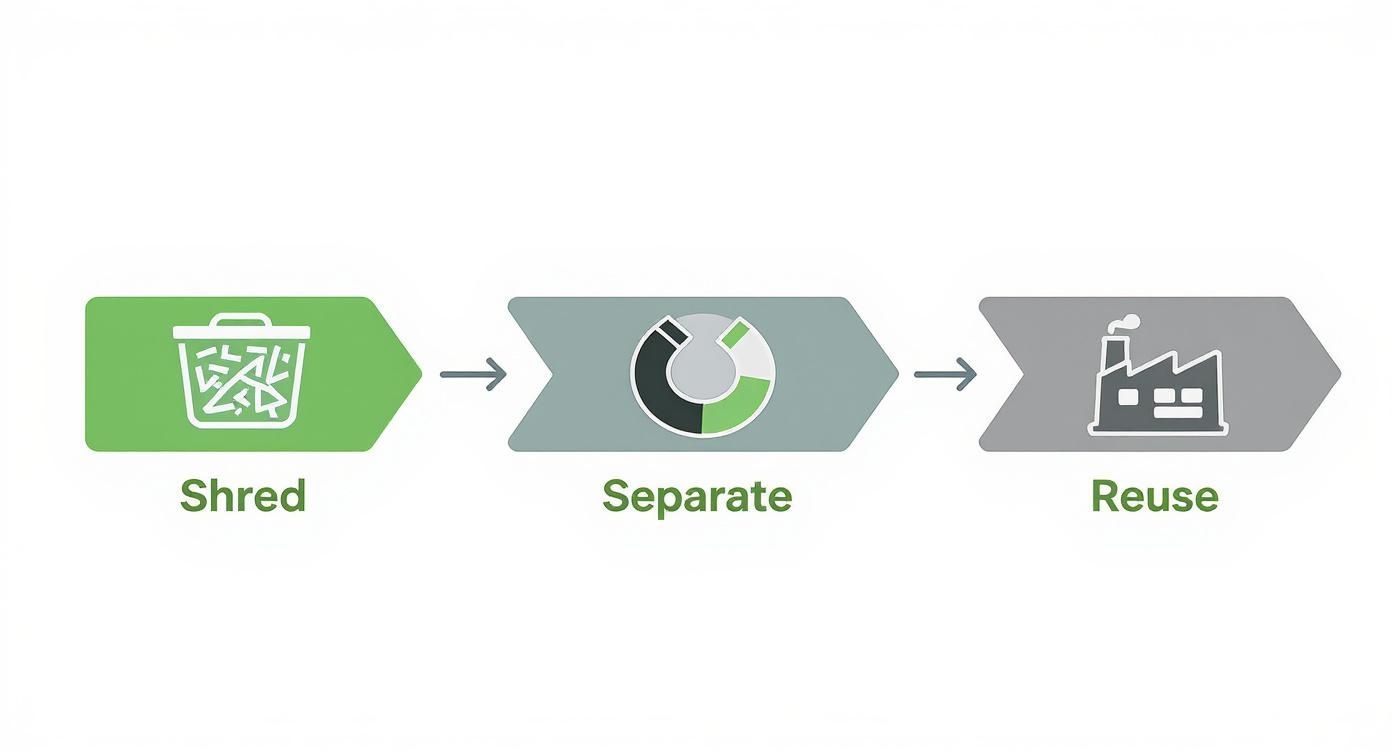
As you can see, the journey moves from breaking down raw materials to sophisticated separation, ultimately feeding valuable commodities right back into the manufacturing supply chain.
The Separation and Reclamation Process
The first step uses advanced mechanical sorting. A combination of powerful magnets, eddy currents, and infrared scanners works together to separate different materials from the mixed pile of shredded e-waste. It’s a highly technical process designed for maximum efficiency.
This sorting creates several distinct commodity streams:
- Ferrous Metals: Steel and iron are extracted by massive magnets. As some of the most recycled materials globally, they’re sent to mills to be melted down and turned into new products.
- Non-Ferrous Metals: Aluminum, copper, and brass are separated using eddy currents. These valuable metals are smelted and refined for reuse in everything from construction materials to new electronic components.
- Plastics: Different types of plastics are sorted using density and optical scanners. They are then cleaned, shredded into pellets, and sold to manufacturers who turn them into car parts, new device casings, and more.
- Precious Metals: Circuit boards contain small but valuable amounts of gold, silver, palladium, and platinum. These are sent to specialized smelters where advanced chemical processes extract these metals, which helps reduce the need for destructive mining operations.
By reintroducing these resources into the supply chain, responsible e-waste recycling actively builds a circular economy. It transforms what was once considered “waste” into a valuable asset, directly reducing the environmental toll of raw material extraction.
Handling Hazardous Materials
Beyond valuable commodities, electronic devices also contain materials that can be harmful if not managed correctly. Certified recyclers are equipped to handle these substances safely, preventing them from contaminating the environment.
Materials like lead from old CRT monitors, mercury from backlights, and cadmium from batteries are carefully isolated. These are then sent to specialized facilities permitted to treat and dispose of hazardous waste according to strict EPA regulations. This downstream accountability is the hallmark of a truly responsible ITAD vendor.
If you choose an uncertified recycler, you run the risk of these toxins ending up in a landfill where they can leach into soil and groundwater. The environmental difference is stark, underscoring why it’s critical to vet your ITAD partner’s environmental credentials.
While e-waste has unique challenges, the principles of responsible material handling are part of a larger, well-established recycling infrastructure. For perspective, in 2024, the United States recycled approximately 46 million tons of paper, and the national recycling industry as a whole generates $170 billion annually. This shows the economic and environmental power of a mature recycling system—a model that secure electronics recycling follows to manage its own complex waste streams. To see how different materials contribute, you can read the full research about U.S. recycling. This larger context shows why choosing certified partners for shredding and recycling is such a sound business decision.
Maintaining Compliance with Data Protection Regulations
For any business handling sensitive information, compliance isn’t just a best practice—it’s a legal necessity. Navigating the complex web of data protection regulations can feel overwhelming, but understanding your obligations is the first step in shielding your organization from crippling fines and lasting reputational damage.
When it comes to IT asset disposal, the rules are clear: your business is responsible for the data on its old equipment until it is verifiably destroyed.
This is where effective shredding and recycling becomes your direct path to compliance. It is more than just getting rid of old hardware; it’s a critical risk management strategy. Regulations like HIPAA, FACTA, and GDPR don’t stop applying when a server is decommissioned. Their data protection mandates extend throughout an asset’s entire lifecycle, right up to its final disposal.
Key Certifications Your ITAD Vendor Must Have
So, how can you be sure a vendor meets these high standards? Certifications are your proof. They are not just logos on a website; they represent a solid commitment to rigorous, third-party audited processes for both data security and environmental responsibility.
Two of the most critical certifications in the ITAD industry are:
- R2 (Responsible Recycling): This standard focuses on protecting the environment, as well as the health and safety of workers and communities. An R2-certified vendor is audited to ensure they follow a strict hierarchy of reuse, recycling, and disposal methods, preventing e-waste from being irresponsibly dumped.
- e-Stewards: Considered by many to be the gold standard, e-Stewards is built on a complete ban of exporting hazardous e-waste to developing nations. It also demands the highest levels of data security and worker protection.
Choosing a vendor with these certifications means you’re partnering with a company that has already proven its commitment to the highest industry benchmarks. You’re not just hoping they do the right thing—you know they do.
The Paper Trail That Protects Your Business
Your compliance strategy is only as strong as its documentation. Without a clear, auditable paper trail, you have no way to prove you acted responsibly in the event of an audit. Two documents are non-negotiable in the ITAD process.
First is the Chain of Custody record. This document meticulously tracks your assets from the moment they leave your facility. It logs every single touchpoint, including who handled the equipment, where it was transported, and when it arrived at the secure processing plant. An unbroken chain of custody is your proof of due diligence.
The Certificate of Destruction is your ultimate legal safeguard. It serves as irrefutable proof that your data-bearing assets were physically destroyed in accordance with federal and state regulations, effectively transferring liability from your organization to the disposal vendor.
This final certificate details precisely what was destroyed, the method used (e.g., shredding), the date of destruction, and a unique serial number for auditing. For businesses needing to meet specific government sanitization standards, understanding the technical guidelines is key. For a detailed breakdown, you can explore the NIST 800-88 guidelines for media sanitization, which provide the federal framework for proper data destruction.
Key ITAD Regulations and Their Data Destruction Requirements
Different regulations govern various types of data, but they all share one common thread: a non-negotiable requirement for secure disposal. While the table below covers some key ITAD-related rules, it’s important to remember that a holistic approach is crucial. For a broader perspective on managing various business rules, consider understanding compliance risk management.
Here’s a quick look at some of the primary regulations and what they demand for data destruction.
| Regulation | Governs | Data Destruction Implication |
|---|---|---|
| HIPAA | Protected Health Information (PHI) | Requires PHI to be rendered unreadable, indecipherable, and unable to be reconstructed. Physical destruction like shredding is a preferred method. |
| FACTA | Consumer financial and personal information | Mandates that businesses destroy consumer report information before discarding it. The FTC’s Disposal Rule specifically cites shredding as a compliant method. |
| GDPR | Personal data of EU citizens | Imposes strict rules on data handling, including the “right to erasure.” Organizations must be able to prove they have securely and permanently deleted personal data upon request. |
| SOX | Corporate financial records and reporting | Requires public companies to maintain and securely dispose of financial records to prevent fraud. Data destruction must be documented and auditable. |
Ultimately, staying on the right side of these laws means treating data destruction with the same seriousness as data creation. A documented, certified, and verifiable process isn’t just good practice—it’s your best defense.
Building Your Internal IT Asset Disposal Plan
A successful ITAD strategy doesn’t begin when the vendor’s truck arrives—it starts long before, with a robust internal plan. A proactive approach transforms IT asset disposal from a chaotic, last-minute task into a secure, repeatable, and streamlined process. For IT and facility managers, establishing this internal framework is the key to ensuring every disposal event is executed flawlessly.
This is not about creating more bureaucracy. It’s about building a bulletproof system that mitigates risk, avoids logistical nightmares, and protects your company from the inside out. A sound internal plan ensures that from the moment a device is marked for retirement, it is treated with the same security and accountability as when it was live on your network.
Start with a Detailed Asset Inventory
You cannot securely dispose of assets you cannot track. The first step is to create a detailed inventory of every single asset slated for retirement. This is more than a simple headcount; it is a critical security measure and the foundation of your chain of custody.
Your inventory must capture key details for each piece of equipment:
- Asset Tag Number: Your company’s unique identifier.
- Serial Number: The manufacturer’s unique device identifier.
- Asset Type: Specify if it is a laptop, server, hard drive, or network switch.
- Physical Location: Note its last known location (e.g., storage closet, data center rack).
This list becomes your master record. When your ITAD partner arrives, you will match their count against your list, ensuring no asset is unaccounted for. This step is fundamental to a secure shredding and recycling process.
Define Clear Data Handling Policies
Your employees are your first line of defense in maintaining data security. It is vital to create and communicate clear policies for handling equipment being decommissioned. Everyone must understand that old IT assets are not junk—they are containers filled with sensitive company information.
These policies should strictly prohibit any unauthorized or casual disposal. No employee should ever be permitted to take old equipment home, attempt to sell it, or discard it in a regular dumpster. Clear rules prevent accidental data breaches and help foster a security-first culture. You can learn more about the full IT asset disposition process to help shape your internal policies.
Secure Assets Before Pickup
The moment an asset is decommissioned, it becomes a security risk. Internal theft of IT equipment is a real and often overlooked threat. To mitigate this, designate a specific, secure location for storing all end-of-life assets awaiting pickup.
This secure holding area must be access-controlled. This could be a locked storage room, a caged-off section of a warehouse, or an office with limited entry. Centralizing retired equipment not only prevents theft but also streamlines the pickup process for your disposal vendor.
Consolidating all assets in one place makes the logistics of collection far more efficient. It means your vendor can quickly and accurately collect everything on the inventory list without searching multiple locations, saving time and reducing the potential for errors.
Establish a Protocol for Documentation
Documentation is your legal proof of compliance. Your internal plan must include a clear process for managing the essential paperwork from your ITAD vendor. This includes the initial chain of custody record you receive at pickup and the final Certificate of Destruction and Recycling you receive after processing is complete.
Assign a specific person or department—typically IT or compliance—to be responsible for receiving, verifying, and securely filing these documents. These records are your best defense in an audit and must be retained according to your company’s data retention policies and any relevant regulations. A strong documentation protocol closes the loop on a secure disposal process, giving you a clean, auditable trail from start to finish.
How to Choose the Right ITAD Partner in Atlanta
Selecting an IT Asset Disposition (ITAD) vendor is one of the most critical security and compliance decisions your business will make. This is not about finding the lowest-cost pickup service; it is about mitigating the most risk.
The right partner acts as an extension of your security team. The wrong one, however, can expose your organization to devastating data breaches and significant legal penalties. A qualified partner for shredding and recycling offers more than a simple transaction—they provide a secure, transparent, and fully auditable process that protects your data from the moment it leaves your building until you have the final Certificate of Destruction.
Vetting Your Vendor on Certifications and Security
First, scrutinize a vendor’s certifications and their physical security protocols. These are not just marketing badges; they are independent verification that a company is committed to industry best practices.
When evaluating a potential partner in the Atlanta area, start with these non-negotiable questions:
- Are you R2 or e-Stewards certified? These are the gold standards for responsible electronics recycling and data security. A certified vendor has passed rigorous third-party audits covering everything from environmental practices and worker safety to secure data handling.
- What are your facility’s security measures? Ask about 24/7 surveillance, access control systems, and employee background checks. A secure facility is fundamental to protecting your assets before they are processed.
- What is your process for secure transportation? Your assets are most vulnerable during transit. A reliable partner will use GPS-tracked vehicles, sealed and locked containers, and vetted logistics staff to guarantee a secure chain of custody.
Evaluating Expertise and Documentation
Beyond a secure facility, your vendor’s expertise in handling different types of equipment and providing rock-solid documentation is essential. Not all IT assets are the same, and your partner needs the capability to manage everything from standard office laptops to highly specialized data center, medical, or laboratory equipment.
Choosing a vendor is a matter of trust and verification. Their ability to provide an unbroken, fully documented Chain of Custody is your proof of due diligence and your ultimate defense in any compliance audit.
Ask potential partners about their experience in your specific industry. A vendor who already works with healthcare clients, for example, will be well-versed in the strict requirements of HIPAA.
Finally, confirm their documentation process. Will you receive a serialized inventory report at pickup? How quickly will they issue a formal Certificate of Data Destruction and Recycling? This paperwork is your legal proof of compliant disposal—it’s not optional. For a deeper look into the vetting process, check out our guide on the criteria for selecting a recycling center. By asking the right questions, you can confidently choose a partner who will protect your organization’s reputation and security.
Common Shredding and Recycling Questions
When it is time to manage end-of-life IT assets, questions are inevitable. Making smart, secure decisions is much easier with clear, straightforward answers. This section addresses some of the most frequent questions we hear from businesses about professional shredding and recycling services.
Our goal is to provide the insights you need to ensure your ITAD plan is secure, compliant, and efficient from start to finish.
Is a Certificate of Destruction Legally Binding?
Yes, absolutely. A Certificate of Destruction is a formal, legally recognized document that serves as your official record of compliant disposal and a critical component of your risk management strategy.
This document details precisely what was destroyed, the method used, and the date of destruction. It creates an auditable trail proving you have performed your due diligence, which is essential for satisfying regulatory requirements under laws like HIPAA, FACTA, or SOX.
How Does Shredding Differ from Data Wiping?
This is a critical distinction. Data wiping uses software to overwrite existing data, but it is not always reliable. Wiping often fails on hard drives with even minor damage and can be inconsistent with modern solid-state drives (SSDs).
Shredding, on the other hand, is a physical process. The device is literally ground into small, irreparable pieces, making it completely impossible for anyone to recover the data. That is why physical destruction is the only truly foolproof method for permanent data elimination.
Think of it this way: wiping is like erasing a document, while shredding is like putting it through a woodchipper and then burning the pieces. One leaves a slight chance of recovery; the other offers total finality and peace of mind.
What Is the Best Way to Prepare Equipment for Pickup?
Your ITAD partner should provide a detailed checklist, but a few best practices always apply. First, compile a thorough inventory of all equipment being disposed of, including serial numbers and any internal asset tags.
Next, it is helpful to gather all equipment in one secure, easily accessible location. This minimizes the risk of internal theft and makes the pickup process much smoother. Unless your internal policy dictates otherwise, it is best to let the certified professionals handle the removal of hard drives.
Can Specialized Equipment Be Handled?
Of course. Certified ITAD vendors are well-equipped to manage sensitive and unique equipment from a wide range of industries. For more answers, feel free to check out our list of common electronics recycling queries for even more clarity.
Whether you have obsolete medical devices, laboratory instruments, or proprietary manufacturing hardware, a qualified partner will have the expertise to ensure compliant handling, data destruction, and responsible recycling for your specific assets.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal in Atlanta, GA. We deliver transparent, compliant, and reliable shredding and recycling services tailored to your business’s security needs.

![7 Universal Waste Examples Businesses in [City], [State] Need to Know in 2026](https://sonitechllc.com/wp-content/uploads/2026/04/universal-waste-examples-doodle-frame-768x431.webp)