Degaussing is the process of completely and permanently wiping data from magnetic storage media, like hard disk drives (HDDs) and old backup tapes. It blasts the device with a powerful magnetic field, scrambling the magnetic particles that hold your data and making it forensically unrecoverable.
For any business, this method is a non-negotiable step to guarantee sensitive corporate information is gone for good before recycling or disposing of IT assets.
What Is Degaussing, Really?

To get a clear picture of what degaussing does, think of a hard drive platter as a magnetic whiteboard. Your business data is "written" by arranging millions of microscopic magnetic particles into specific patterns. When you just delete a file, it's like using a cheap eraser—the obvious writing is gone, but faint outlines remain. With the right forensic tools, someone can easily recover what was there before.
Degaussing is the equivalent of taking a power washer to that whiteboard. It doesn’t just erase the data; it blasts the entire surface back to a completely random, blank state. The intense magnetic field it generates knocks every single magnetic particle out of alignment, utterly destroying the patterns that formed your corporate data. The information isn't just removed; it's obliterated.
To quickly summarize the key points, here’s a simple breakdown for IT managers:
Degaussing at a Glance
| Aspect | Description |
|---|---|
| What It Is | A data destruction method that uses a powerful magnetic field. |
| Media Affected | Primarily magnetic storage like Hard Disk Drives (HDDs) and enterprise tapes. |
| Outcome | Data is rendered permanently and forensically unrecoverable. |
| Device Impact | The storage device (e.g., HDD) is also destroyed and becomes unusable. |
This process ensures that once a drive is degaussed, there is no going back. The data is gone, and so is the drive's ability to ever function again, making it a crucial step in secure IT asset disposal.
From Naval Warfare to Data Security
Believe it or not, the technology we now use for data security has its roots in naval warfare. Degaussing was originally developed during World War II to make ships "invisible" to magnetic sea mines, which were designed to detect the massive metal hulls of naval vessels.
The same core principle—using a powerful, reversing magnetic field to neutralize a magnetic signature—was adapted from protecting battleships to protecting your most sensitive corporate data.
What Degaussing Actually Achieves
This process is far more absolute than simply deleting files or formatting a drive. It offers a final, irreversible method of data destruction for any magnetic media.
When a company degausses a hard drive, it guarantees that:
- The data is permanently gone. The physical magnetic signature that represented your files is destroyed.
- The drive itself is useless. Degaussing also erases the critical firmware and servo tracks the drive needs to operate, effectively bricking it.
- Compliance requirements are met. It's a recognized and approved method for meeting stringent data protection laws like HIPAA, FACTA, and GDPR.
By destroying data so thoroughly, degaussing provides an absolute guarantee that sensitive business information won't fall into the wrong hands. It’s a vital part of any serious corporate data security strategy. You can learn more about how degaussing fits into a complete security plan in our guide on what is data sanitization.
How Degaussing Makes Business Data Disappear Forever
To really get your head around degaussing, you have to picture what’s going on inside a classic hard disk drive (HDD). Think of those shiny, spinning platters as a massive landscape covered with billions of tiny, microscopic compass needles. When your company saves a file—a client list, a financial forecast, anything—the computer carefully lines up these needles into specific North-South patterns. These patterns are the physical reality of the ones and zeros that make up your digital data.
When you just "delete" a file, the system doesn't actually wipe the data. It just removes the signpost that points to it, leaving the magnetic patterns themselves completely intact and often recoverable. This is where degaussing comes in, and it plays on a whole different level. A degausser machine unleashes an incredibly powerful, focused magnetic field, one that's thousands of times stronger than the field used to write the data in the first place.
This overwhelming force completely washes over the drive's platters, hitting every single one of those microscopic needles with a magnetic pulse they can't resist.
The Science of Magnetic Obliteration
The intense energy from the degausser throws all the magnetic particles into total chaos. Instead of pointing in their neatly arranged patterns, they are violently scrambled and forced into a completely random, uniform state. The original North-South alignments that represented your sensitive business information aren't just overwritten or erased; they are fundamentally and irrevocably obliterated. The magnetic blueprint is gone.
This process is critical for secure data destruction for a few key reasons:
- Destruction of User Data: First and foremost, all the organized magnetic patterns are reduced to meaningless noise, making any kind of forensic data recovery impossible.
- Destruction of Drive Firmware: Degaussing also wipes out the essential factory-written code that tells the drive how to operate.
- Destruction of Servo Tracks: It erases the timing and positioning guides—the servo tracks—that the read/write heads need to navigate the platters.
From Functional Drive to Unusable Brick
The end result of this process is absolute. By destroying the firmware and servo tracks, degaussing renders the hard drive physically useless. Without that critical operational data, the drive’s internal parts have no instructions on how to spin up, where to find anything, or how to function at all.
In essence, a degaussed hard drive is no longer a storage device. It is effectively a "bricked" piece of hardware, incapable of being formatted, partitioned, or ever used again. This physical finality provides the ultimate assurance that the data it once held is gone forever.
This permanent destruction is exactly why degaussing is a cornerstone of secure IT asset disposal for any organization that can’t afford even the slightest risk of a data leak. For a deeper look into the mechanics, you can explore our guide on what is a degausser and see how these powerful machines work. This process ensures that when an asset leaves your control, the sensitive information it contained has been completely neutralized.
Understanding Which Devices Can Be Degaussed
Here's one of the most important things any IT manager needs to know: degaussing isn't a silver bullet for data destruction. Its power is entirely tied to the technology inside the storage device. Plain and simple, degaussing only works on hardware that stores data magnetically.
This single fact means that knowing your hardware is the absolute first step in any secure IT asset disposal (ITAD) plan. Using the wrong destruction method doesn’t just mean you failed to erase data—it means you’ve created a massive, and completely avoidable, corporate security hole.
Magnetic Media: The Right Candidates for Degaussing
Degaussing is the gold standard for wiping data from certain types of older and enterprise-grade storage. These devices rely on tiny magnetic particles arranged in specific patterns to hold information. A degausser’s intense magnetic field completely scrambles those patterns, permanently destroying the data.
The main types of media that are perfect for degaussing include:
- Traditional Hard Disk Drives (HDDs): With their spinning magnetic platters, these are the most common devices that businesses degauss. The process doesn’t just wipe the data; it destroys the firmware and servo tracks, rendering the HDD completely useless.
- Magnetic Tapes: A huge range of backup and archival tapes are magnetic. This covers common enterprise formats like LTO (Linear Tape-Open), DLT (Digital Linear Tape), and older ones like DDS/DAT.
For this kind of hardware, degaussing is a forensically sound way to sanitize data. It ensures that even the most skilled expert can't recover what was once there.
The flowchart below gives you a simple visual of what degaussing does to magnetic data, taking it from a structured, readable state to total chaos.
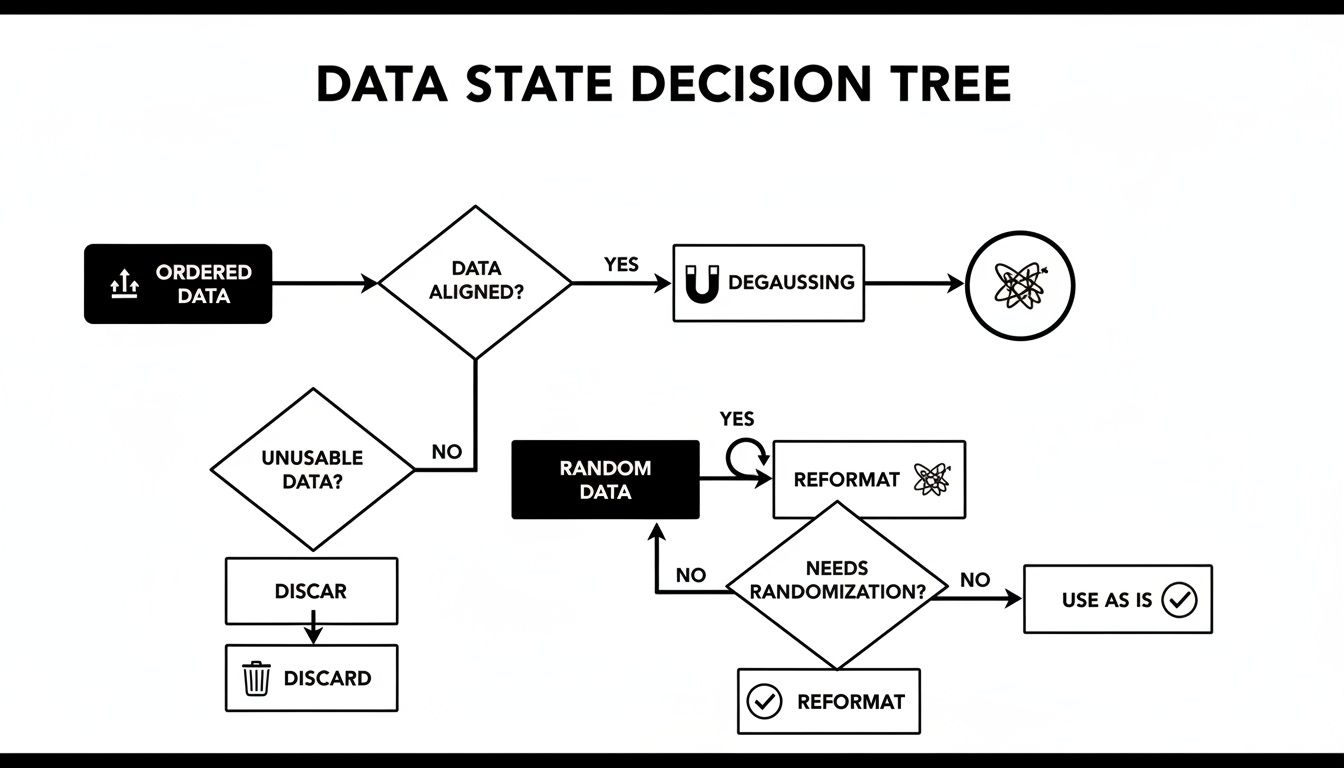
As you can see, the process takes organized information and completely randomizes its magnetic structure, making the original data gone for good.
Non-Magnetic Media: Where Degaussing Fails
On the flip side, trying to degauss modern, non-magnetic storage is a complete waste of time. These devices don't use magnetism to store data, so a degausser's power has no effect. It’s like trying to erase a printed book with a giant magnet—the tool is simply wrong for the job.
Degaussing has absolutely no effect on media like:
- Solid-State Drives (SSDs): SSDs use flash memory (NAND chips) to store data electronically. There are zero magnetic parts to erase.
- USB Flash Drives: Just like SSDs, these popular thumb drives are based on NAND flash memory.
- SD Cards and Memory Cards: The small cards used in cameras and other gadgets also use electronic flash memory.
- Smartphones and Tablets: The internal storage in every modern mobile device is based on flash memory.
This is a common and dangerous mistake. An IT manager who sends a batch of old SSDs to be degaussed is living with a false sense of security. The sensitive corporate data on those drives is still perfectly intact and readable.
When dealing with these non-magnetic devices, the only truly secure and compliant method of data destruction is physical shredding. You can learn more about different strategies in our guide on what to do with old hard drives and other media. Knowing the right tool for the right job is the bedrock of protecting your organization's data.
To make it even clearer, here's a quick reference table for your IT department.
Media Destruction Methods at a Glance
This table breaks down which common storage types are suitable for degaussing and which require a different approach.
| Media Type | Effective for Degaussing? | Correct Method |
|---|---|---|
| Hard Disk Drives (HDDs) | Yes | Degaussing, Shredding |
| Magnetic Tapes (LTO, DLT) | Yes | Degaussing, Shredding |
| Solid-State Drives (SSDs) | No | Shredding |
| USB Flash Drives | No | Shredding |
| Smartphones/Tablets | No | Shredding |
| SD/Memory Cards | No | Shredding |
This simple breakdown should serve as a go-to checklist for IT managers. When in doubt, always confirm the underlying technology of your storage media before choosing a destruction method. It's the only way to be certain your company's data is truly gone.
Degaussing vs Shredding: Comparing Destruction Methods

When it's time to retire old IT assets, choosing the right data destruction method is one of the most critical security decisions your business will make. The three main options—degaussing, shredding, and software wiping—each play a very different role. Getting a handle on their differences is key to aligning your actions with your security policies, compliance needs, and hardware lifecycle plans.
Degaussing is the go-to for an absolute, forensic-level guarantee of data erasure on magnetic media. Nothing is coming back from that. Physical shredding, on the other hand, grinds a device into tiny, unrecognizable pieces, giving you clear visual proof of destruction. It’s also the only compliant method for Solid-State Drives (SSDs). And then there’s software wiping, which simply overwrites existing data—a solid choice only if you plan to reuse or resell the hardware.
The right choice really boils down to your end goal. For total security, many organizations don't just pick one; they layer their approach.
The Degauss and Shred Combination
For magnetic media like Hard Disk Drives (HDDs), the most secure protocol out there is a one-two punch: degaussing followed by shredding. This two-step process is the gold standard for government agencies and any highly regulated industry that simply can't afford any margin for error.
First, the HDD gets degaussed. This step completely sanitizes the drive, wiping every last bit of data from the magnetic platters at a level that even forensic experts can't recover.
Next, that now-useless drive is physically shredded into pieces. This gives you indisputable visual confirmation that the device is destroyed, leaving no chance it could be mistaken for a working drive or tampered with down the line. This dual method offers the ultimate peace of mind for businesses.
Why Media Type Dictates the Method
Choosing between degaussing and shredding isn't a matter of preference—it's dictated by the technology inside the storage device itself. As we’ve covered, degaussing only works its magic on magnetic media like HDDs and tapes.
For SSDs, which store data on flash memory chips, shredding is the only secure and compliant option. A powerful magnet does absolutely nothing to an SSD, which is why shredding has become the industry-standard method to make sure the data they hold is gone for good. Working with a certified ITAD partner like Beyond Surplus ensures you're always using the right method for every asset. Our experts can walk you through all the options for secure hard drive shredding for any media type.
The decision between degaussing and shredding isn't about which method is "better" in a general sense, but which method is correct for the specific media and required security level. An improper choice can lead to significant corporate data vulnerabilities.
Comparing Degaussing, Shredding, and Wiping
To make the decision process a bit simpler, here’s a straightforward comparison of the three main data destruction methods. This table lays out their best use cases, key benefits, and limitations to help you figure out the best strategy for your business assets.
| Feature | Degaussing | Shredding | Software Wiping |
|---|---|---|---|
| Media Type | HDDs & Magnetic Tapes | All Media (HDDs, SSDs, etc.) | HDDs & some SSDs |
| Data Recovery | Impossible | Impossible | Possible with advanced tools |
| Device Reusability | No (Device is destroyed) | No (Device is destroyed) | Yes (Device remains functional) |
| Visual Proof | No | Yes (Physical destruction) | No |
| Best For | Max security on magnetic media | Ultimate security on all media | Reusing or reselling hardware |
The need for secure destruction is only growing. The hard drive degaussers market is expected to jump from USD 101.23 million in 2023 to USD 148.75 million by 2033, pushed by the demand for irreversible data erasure to comply with regulations like HIPAA and GDPR. This mirrors how the naval sector has long relied on degaussing for stealth.
Beyond Surplus provides both on-site and off-site degaussing with Certificates of Destruction, which is essential for projects like data center de-installations where data leaks can cost companies an average of USD 4.45 million globally. You can read the full research about these market trends and their drivers.
Meeting Compliance with Certified Degaussing
For any business in a regulated field, getting rid of old data isn't just a good idea—it's the law. Strict rules like HIPAA for healthcare, GDPR for personal data, and FACTA for consumer credit info create a rigid framework for protecting sensitive information. Getting this wrong can lead to crippling fines and a damaged reputation you might never recover from.
This is where certified degaussing comes in. It’s a recognized and approved method for meeting these tough standards. The process is forensically sound, ensuring that every last bit of data on magnetic media is wiped out for good, putting you in line with data privacy and security mandates.
The Role of Certified ITAD Vendors
The key to getting this right is partnering with a certified IT Asset Disposition (ITAD) vendor. True professionals use degaussers that are evaluated and listed by the National Security Agency (NSA), which guarantees the equipment’s magnetic field is strong enough to meet federal standards for complete data obliteration. This isn't just a small detail; it's a critical step in maintaining a defensible security posture.
Once the job is done, a reputable ITAD partner will give you a Certificate of Destruction. This is your legally defensible record for any audit, proving you took the necessary, certified steps to destroy data securely and legally. The certificate includes serialized tracking information, following each individual asset through the destruction process.
Think of this certificate as more than just a piece of paper. It represents a formal transfer of liability. Once it's issued, the responsibility for the disposed data shifts from your organization to the vendor, protecting your business and showing you’ve done your due diligence.
Understanding the general landscape of regulatory compliance is essential, as degaussing is often a core requirement under strict data protection laws. This context helps businesses see why certified processes are so vital for managing risk.
Proving Compliance and Transferring Liability
The documentation provided by a certified vendor is your first line of defense in an audit. It’s concrete proof that you followed an established, secure, and compliant process for data destruction. This is especially important in sectors like healthcare and finance, where the chain of custody for sensitive data is put under a microscope.
An ITAD partner with the right credentials, like an R2 Certification, ensures the entire process is handled responsibly from start to finish. You can learn more about why industry standards matter in our article explaining what is R2 certification.
Modern degaussers can wipe a hard drive clean in seconds—a vital capability when you consider how many data breaches come from improperly discarded media. In fact, driven by the growing need for compliance, the degaussing market is projected to hit USD 148.75 million by 2033. For IT directors, cloud teams, and educational institutions, certified degaussing is a cornerstone of a secure ITAD strategy.
Ultimately, meeting compliance isn't just about destroying data. It's about implementing a documented, defensible, and secure process that shields your organization from the massive legal, financial, and reputational risks of a data breach.
Putting Secure Degaussing into Practice
By now, it's clear that degaussing is an incredibly powerful way to permanently wipe data from hard drives and tapes. But here’s the reality check for business owners and IT managers: this is absolutely not a do-it-yourself project. Proper, compliant degaussing demands highly specialized—and expensive—equipment, plus a rock-solid understanding of complex regulations.
Trying to tackle this in-house is a minefield of risk. You could face everything from incomplete data erasure to falling out of compliance with laws like HIPAA or the FTC Disposal Rule. Partnering with a certified IT Asset Disposition (ITAD) expert like Beyond Surplus takes the guesswork, liability, and operational headache off your team's shoulders.
Why Your Business Needs a Certified ITAD Expert
When you bring in a professional, you’re not just outsourcing a task; you're gaining access to the right tools and a proven process for a secure, defensible data destruction program. An expert partner provides a structured, documented approach that will stand up to any audit.
Here’s what a partnership with Beyond Surplus brings to the table:
- Access to NSA-Listed Degaussers: We use the same caliber of equipment trusted by government agencies. This guarantees the magnetic field is strong enough to obliterate data on today’s high-coercivity hard drives.
- Airtight Chain of Custody: From the moment we pick up your assets to their final destruction, every step is tracked and documented. This minimizes risk and leaves no gaps in security.
- Audit-Ready Documentation: You'll receive a formal Certificate of Destruction. This isn't just a piece of paper; it's your legally defensible proof of compliance and the official transfer of liability.
Don't let legacy hard drives and old backup tapes become a ticking time bomb in your storage closet. It only takes one overlooked device to trigger a catastrophic data breach, torpedoing your company's reputation and finances. The risk is just too high to leave to chance.
Shifting your mindset from simple hardware disposal to a strategic IT asset disposition plan is a game-changer for modern data security. This proactive approach ensures every single device holding your data is handled according to a secure, repeatable, and compliant process.
It’s time to build a data destruction program you can actually count on—one that’s secure, compliant, and defensible. Contact the experts at Beyond Surplus today to talk about your specific business needs and build an ITAD plan that protects your most valuable asset: your data.
Common Questions About Degaussing
Even after understanding the technical side of things, it’s natural for business owners and IT managers to have questions about what degaussing actually means for their hardware. Here are some straightforward answers to the questions we hear most often.
Does Degaussing Physically Destroy The Hard Drive?
For all practical purposes, yes. Degaussing doesn't just erase your files; it completely scrambles the essential firmware and servo tracks the drive needs to operate. Think of it like wiping out the drive's internal operating system and its ability to navigate itself.
Once that foundational data is gone, the drive can't be formatted, recognized by a computer, or used in any way. It effectively becomes a metal and plastic paperweight, ready for responsible physical recycling.
Is Degaussing A Better Method Than Shredding?
It's not about one being "better"—they're different tools for different jobs. Degaussing is the gold standard for achieving 100% data sanitization on magnetic media like HDDs and tapes before they are physically destroyed. Nothing survives it.
Shredding, on the other hand, provides total physical destruction and is the only secure method for non-magnetic media like SSDs. For the absolute highest level of security, many government and corporate policies mandate both: first degauss the HDD to guarantee the data is gone, then shred it for physical proof. The right move depends entirely on your media type and compliance requirements.
The most secure data destruction strategies often layer methods. For magnetic media, this means a "degauss-then-shred" approach, which combines absolute data sanitization with verifiable physical destruction, leaving zero room for error.
How Can I Confirm Degaussing Was Successful?
Since the drive is rendered useless by degaussing, you can't just plug it in to check. Verification comes down to two things: process and paperwork. The best way to ensure it's done right is to work with a certified IT Asset Disposition (ITAD) vendor.
A professional service uses degaussers that are on the NSA's Evaluated Products List (EPL). This isn't just a fancy label; it's your guarantee that the machine’s magnetic field is powerful enough to meet strict government standards for total data destruction.
After the process, you'll get a serialized Certificate of Destruction. This is more than just a receipt; it's a legally defensible document that proves your organization followed a secure and compliant process, creating a clear audit trail and transferring liability.
What Happens To A Drive After It Is Degaussed?
Once a drive is degaussed, its data is gone for good and it’s completely inoperable. The final step is responsible electronics recycling. That degaussed drive—now just a mix of metal and plastic—is physically broken down so its raw materials can be recovered and put back into the supply chain.
Using a certified e-waste recycling partner ensures this last step is handled in an environmentally sound and compliant way. It keeps hazardous materials out of landfills and supports a circular economy for electronics. The entire process addresses both data security and environmental responsibility from start to finish.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. We provide a documented, compliant, and secure process to protect your business data. Learn more about our nationwide IT asset disposal solutions.