Old laptops in a locked closet, retired switches under a conference table, backup drives nobody wants to touch, and a rack of decommissioned servers still sitting in a branch office. That’s how business e recycling problems usually surface. Not as a sustainability initiative, but as a backlog.
In Atlanta, Georgia, that backlog carries real exposure. A single forgotten SSD can turn into a security incident. A pile of obsolete equipment can block a move, delay a refresh, or create audit questions your team can’t answer cleanly. Idle hardware also ties up value that could have been recovered through resale, component harvesting, or commodity recycling.
Most companies don’t need another reminder to “recycle responsibly.” They need a working process for pickup, inventory, data destruction, downstream documentation, and liability transfer. They need an e recycling partner that treats end-of-life IT like a controlled business workflow, not a junk haul.
Your E Recycling Challenge Starts Now
The usual trigger is operational. An office consolidation creates a pile of retired desktops. A data center refresh leaves older servers with no approved exit path. Facilities wants the room cleared. IT wants chain of custody. Legal wants proof. Finance wants to know whether any of it still has value.

That’s where many internal programs stall. Someone suggests a local scrap pickup. Someone else asks whether the drives were wiped. Then the project sits because nobody wants to own the risk.
What the backlog is really costing you
Stored electronics aren’t neutral. They consume floor space, complicate inventories, and keep sensitive media inside the business longer than necessary.
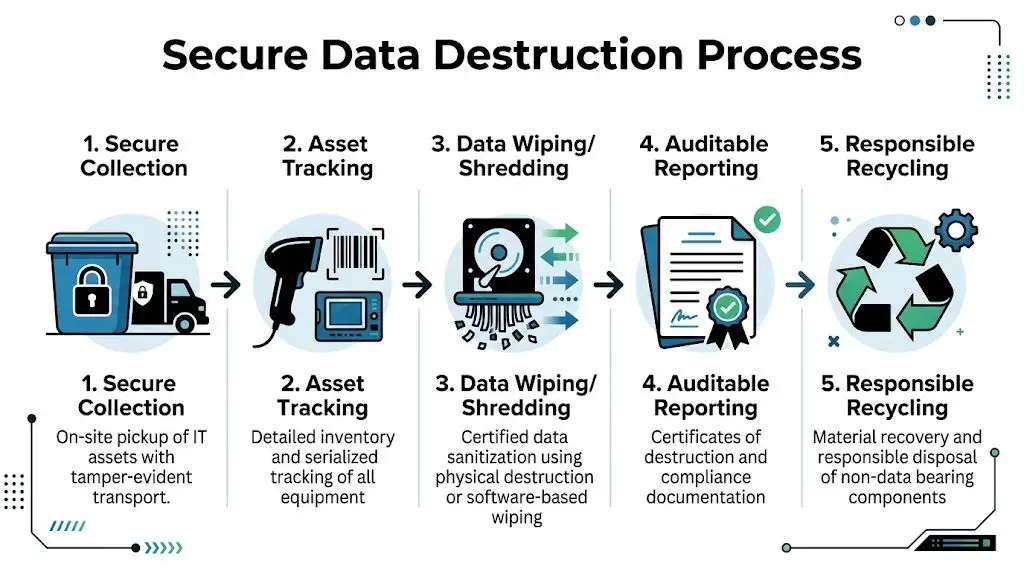
A more workable approach is to treat e recycling as an ITAD process with four controls:
- Asset identification so equipment isn’t leaving the site as an untracked bulk load
- Documented handoff so custody is clear from pickup forward
- Verified data destruction for anything that ever stored business information
- Recycling and remarketing records that support audits, policy reviews, and vendor due diligence
Old equipment becomes risky the moment nobody can say what’s on it, where it is, or who last handled it.
If your team is already searching for commercial e recycling pickup options, that usually means the issue is no longer disposal. It’s governance.
What works and what fails
What works is a scheduled, serialized, documented removal tied to destruction and recycling certificates.
What fails is informal cleanout logic. “We wiped most of it” isn’t enough. “A recycler picked it up” isn’t a custody record. And “it’s been sitting there for months” is how useful assets turn into pure scrap.
What Business E-Waste Really Is
Business e-waste is broader than most asset lists suggest. It includes retired laptops, desktops, monitors, printers, mobile devices, servers, storage arrays, switches, telecom gear, point-of-sale systems, lab electronics, medical devices, and proprietary hardware used in operations or product development.
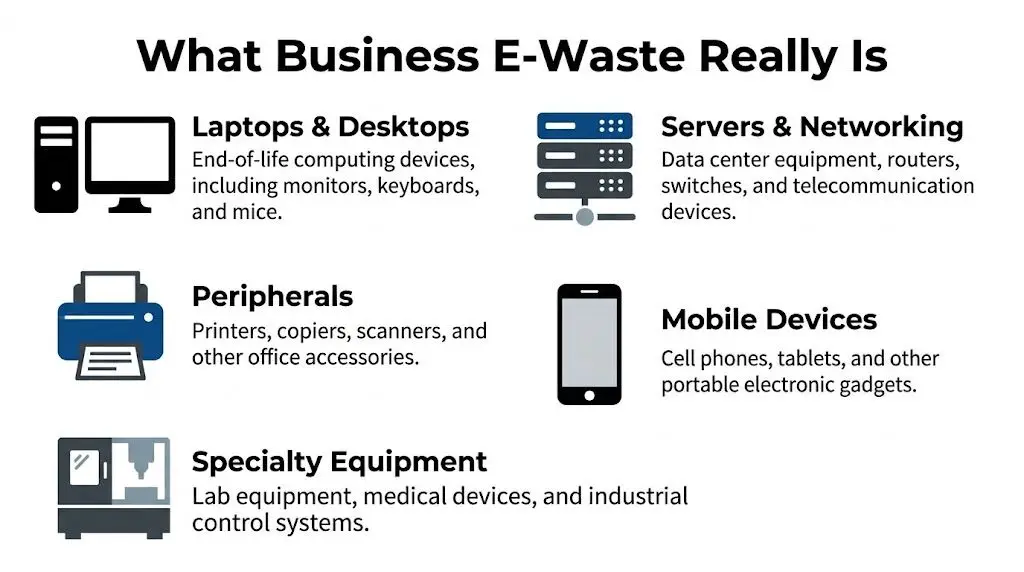
A lot of companies still think of e recycling as “computers and monitors.” That misses the equipment most likely to create compliance issues: storage media, specialty electronics, and devices tied to regulated workflows.
The scale behind the problem
The volume of discarded electronics keeps climbing. In 2022, the world generated 62 million tonnes of e-waste, an 82% increase from 2010. Projections show 82 million tonnes by 2030, and only 22.3% is formally collected and recycled, according to global e-waste data summarized by Sensoneo.
For business leaders, the takeaway isn’t abstract. More electronic waste in circulation means more pressure on disposal channels, more scrutiny on downstream handling, and more room for bad vendors to present themselves as legitimate processors.
What belongs in a business e recycling program
A practical enterprise scope usually includes:
- User devices such as laptops, desktops, thin clients, monitors, docks, and accessories
- Infrastructure gear including servers, racks, storage, firewalls, routers, and switches
- Office support equipment like printers, copiers, scanners, and conference room technology
- Specialty assets such as medical electronics, lab systems, test equipment, and embedded devices
Teams comparing vendors can also benefit from watching how the broader waste management industry organizes collection, transport, and material accountability. The strongest e recycling programs borrow that operational discipline and add tighter controls for data-bearing devices.
If an asset plugs in, stores data, or contains regulated components, it shouldn’t leave your facility through an informal channel.
Navigating Key E Recycling Regulations
Compliance usually breaks down in two places. First, companies underestimate how many rules touch end-of-life electronics. Second, they assume recycling and data handling are separate decisions. They aren’t.

Federal rules that shape disposal decisions
The FTC Disposal Rule matters whenever devices may contain consumer information. The business obligation is straightforward: dispose of that information in a way that protects against unauthorized access. In practice, that means documented sanitization or destruction, not casual reuse or bulk recycling.
Healthcare organizations have another layer. HIPAA doesn’t create a separate recycling category, but it does require covered entities and business associates to protect patient information through the asset’s full lifecycle. If a workstation, copier drive, or storage device held protected data, disposal has to be secure and documented.
Some organizations also manage equipment under internal standards aligned with NIST 800-88. That becomes important during audits, litigation holds, or vendor reviews because it gives the business a recognized framework for sanitization and destruction decisions.
Environmental handling rules still matter
End-of-life electronics can contain batteries, lamps, toner, leaded glass, and other materials that require controlled handling. Businesses often overlook this when they treat cleanouts as facilities projects rather than regulated asset disposition.
A useful starting point is understanding how EPA universal waste requirements affect storage, labeling, and downstream management for common regulated items.
Where companies get exposed
The legal risk usually isn’t a dramatic violation. It’s a documentation gap. Typical weak points include:
- Unclear ownership when facilities, IT, and procurement each assume someone else approved the vendor
- No destruction proof for drives removed during refreshes or de-installs
- Poor downstream visibility when a recycler can’t explain where material goes after pickup
- Mixed loads that combine reusable devices, scrap, and regulated components without proper triage
Practical rule: If your vendor can’t explain custody, sanitization method, and downstream processing in plain language, don’t release assets.
State requirements add another layer. Even when federal rules define the security baseline, state disposal and e-waste laws can affect how organizations manage certain categories of electronics. That patchwork is why serious business e recycling programs rely on documented procedures rather than one-off pickups.
Ensuring Secure and Certified Data Destruction
For most businesses, e recycling is really a data destruction decision wearing an environmental label. The metal, plastic, and glass matter. The bigger risk is what’s left on the drive.
Wiping versus shredding
Certified wiping has a place. It can support remarketing when devices are suitable for reuse and the media type, condition, and policy requirements allow it. But wiping is only reliable when the process is validated, the device is accessible, and the result is captured in an audit trail.
That’s the trade-off many companies miss. Data wiping alone can be unreliable, with failure rates of 40-60% for completely sanitizing SSDs, while on-site physical shredding reduces devices to small fragments and provides auditable proof aligned with NIST 800-88 and the FTC Disposal Rule, as described in SIMS Lifecycle’s explanation of the e-waste recycling process.
When physical destruction is the right call
Use shredding when the risk of residual data outweighs resale value. That often applies to:
- Failed drives that can’t be wiped and verified
- SSDs from regulated environments where certainty matters more than remarketing
- Legacy media from mergers, office closures, and storage-room cleanouts
- High-sensitivity systems used in healthcare, finance, legal, and government work
Certified providers may offer on-site or off-site destruction. The right choice depends on your policy, audit requirements, and tolerance for transport risk before destruction occurs.
The document that matters after the truck leaves
A certificate of data destruction is not a marketing extra. It’s one of the few records that proves a specific asset or media set was destroyed under a controlled process.
That’s why businesses often separate vendors quickly at this stage. If a provider offers pickup but can’t produce detailed destruction records, the chain breaks exactly where your audit team needs clarity.
For companies evaluating service options, secure destruction of data services should include asset tracking, method disclosure, and final reporting that maps back to the items released.
The safest process isn’t always the one with the highest resale return. Sometimes the correct answer is to destroy first and recover material value second.
Managing E Recycling Logistics and Chain of Custody
The strongest e recycling programs look almost boring on paper. That’s a good sign. Predictable scheduling, documented pickups, serialized records, and controlled transport beat “fast and easy” every time.

What a controlled pickup should include
Before equipment moves, the vendor and client should agree on scope. That means site contacts, pickup windows, access constraints, packing assumptions, and whether serialized inventory will be captured on-site or reconciled at the processing facility.
After that, the chain of custody should stay unbroken through each handoff.
A sound workflow usually includes:
- Scheduling and scope confirmation so nobody is improvising at the dock
- Pickup with signed transfer records listing the asset groups or serialized units released
- Transport controls such as secured vehicles and tamper-aware handling
- Receiving reconciliation that confirms what arrived against what left
- Final disposition reporting tied to destruction, recycling, or remarketing outcomes
Why serialized tracking matters
Bulk counts are fine for low-risk scrap. They aren’t enough for mixed enterprise loads.
If a pallet includes laptops, drives, network gear, and specialty devices, serialized tracking gives the business a defendable record. It helps during internal audits, insurance reviews, and vendor disputes. It also makes exceptions visible quickly. Missing asset? Duplicate serial? Wrong disposition? You can find it.
That’s why vendor vetting should go beyond pricing. A practical ITAD vendor due diligence checklist should ask how the recycler documents custody, reconciles discrepancies, and handles downstream vendors.
Unlocking Value with IT Asset Recovery
E recycling doesn’t have to be a pure cost center. If the equipment is recent enough, functional enough, and supported by a documented sanitization path, part of the stream may qualify for resale or component recovery before final recycling.
That’s where IT asset recovery changes the economics. Instead of treating everything as scrap, the processor sorts assets into resale, parts harvesting, commodity recovery, and destruction-only categories.
Where the value actually comes from
Some value comes from remarketable devices. Some comes from components. Some comes from the material stream itself.
The material side is stronger than many buyers realize. Precious metals in circuit boards are concentrated at 250-300 grams per tonne, compared to 5-10 grams per tonne in raw ore. Recycling 1 million laptops saves energy equivalent to removing 3,900 cars from the road for a year and recovers 1,500 tons of steel, based on RTS reporting on the e-waste recycling process.
The real trade-off in buyback programs
Not every asset should be remarketed. The decision depends on age, condition, brand demand, specs, storage media type, and the client’s security posture.
A practical screening model looks like this:
| Asset condition | Best path |
|---|---|
| Newer, working, wipe-verifiable devices | Resale or buyback |
| Repairable units with market demand | Parts harvesting or refurbishment |
| Obsolete or damaged gear | Commodity recovery |
| High-risk data-bearing media | Destruction first, recycling after |
For organizations with larger refresh cycles, business IT asset recovery programs can offset part of the project cost when the inventory supports resale. The mistake is assuming every old laptop has buyback value. Many don’t. The upside comes from proper sorting, not wishful accounting.
Choosing a Partner with R2 and E-Stewards Certifications
Certification matters because most downstream risk sits outside your building. A vendor can pick up equipment cleanly and still create liability later if the processing chain is weak.
What these certifications signal
R2 focuses on responsible reuse, recycling controls, data security, and downstream accountability. It’s especially relevant when a processor handles mixed streams that include resale, dismantling, and commodity recovery.
e-Stewards is often used by organizations that want stricter assurance around export controls and responsible handling of hazardous electronic waste.
The practical point isn’t which logo looks better on a website. It’s whether the certification is current, scoped to the actual facility doing the work, and supported by operational records.
Questions that separate serious vendors from risky ones
Ask these before release approval:
- Which facility is certified and does that facility process my asset type?
- How do you track downstream vendors after dismantling or sorting?
- What happens to batteries, lamps, toner, and damaged media?
- Can you provide destruction certificates and recycling documentation tied to the shipment?
Certifications don’t replace due diligence. They give you a stronger floor, not a free pass.
One more caution. Don’t confuse “certificate of recycling” with “certified recycler.” The first is a document. The second is an audited operating standard. You want both.
Frequently Asked Questions About Business E Recycling
How can I tell if an e recycler is a sham operation
Start with documentation. A legitimate business recycler should explain chain of custody, data destruction options, downstream controls, and export policy without hesitation.
The risk is significant. An estimated 70-80% of US e-waste, valued at over $10 billion annually, is lost to landfills or sham recyclers that illegally export hazardous materials, according to Lewis & Clark Law School commentary on sham recyclers and e-waste controls. The same source notes that businesses should require chain-of-custody records and a documented zero-landfill, zero-export policy.
What business equipment is usually accepted
Commercial programs typically accept laptops, desktops, monitors, servers, storage, networking gear, telecom hardware, printers, mobile devices, peripherals, and many categories of specialty business electronics. Acceptance depends on condition, battery status, and whether the processor is equipped for regulated components.
If you have medical, lab, or industrial electronics, confirm handling requirements before pickup. Those categories often need tighter intake and segregation procedures.
Should we wipe drives ourselves before pickup
Only if your policy allows it and your team can verify the result. Internal wiping can be useful for certain reusable assets, but it shouldn’t replace vendor-side tracking and final disposition records. For failed drives, mixed inventories, or regulated data, physical destruction is usually the cleaner choice.
Do we need on-site destruction
Not always. On-site destruction makes sense when internal policy, regulator expectations, or executive risk tolerance require direct observation before media leaves the facility. Off-site destruction can also work if custody controls, transport, and reporting are strong.
Can e recycling support both compliance and financial recovery
Yes, but not on every asset. Good programs separate devices that can be remarketed from devices that should be destroyed or dismantled immediately. The discipline is in triage. Secure handling comes first. Recovery follows where it’s appropriate.
What should we prepare before a pickup
A simple internal checklist helps:
- Identify the asset groups so IT, facilities, and procurement agree on scope
- Flag data-bearing devices that require destruction or verified sanitization
- Separate specialty items such as batteries, lab devices, or damaged hardware
- Assign one internal owner for approvals, access, and final documentation review
If your team needs a controlled path for end-of-life electronics, contact Beyond Surplus for certified electronics recycling, secure IT asset disposal, data destruction, logistics coordination, and audit-ready reporting.