For any business in Arizona, managing outdated technology is much more than a spring-cleaning task—it’s a critical security operation. Arizona ITAD services offer a secure, compliant, and strategic way to retire old IT assets. This process turns a potential liability into a smoothly managed part of your business lifecycle, covering everything from certified data destruction to responsible recycling and even getting some cash back for your old gear.
Why IT Asset Disposition Is a Core Business Strategy
So, what exactly is IT Asset Disposition (ITAD)? At its core, ITAD is the complete process an organization uses to get rid of retired or obsolete IT equipment in a way that's both secure and environmentally sound. Think of it less like taking out the trash and more like decommissioning a sensitive facility. For any organization in Arizona's booming tech and business sectors, mishandling old computers, servers, and hard drives can lead to disaster.
A single forgotten hard drive can hold a treasure trove of sensitive information—customer data, financial records, you name it. A data breach that starts with a piece of improperly disposed of equipment can trigger massive financial penalties, destroy your reputation, and land you in legal hot water. This is exactly where a certified ITAD partner becomes indispensable.
Beyond Simple Recycling
A professional ITAD program is a meticulously managed process designed to protect your organization at every single step. It’s a world away from just dropping off old equipment at a local recycler.
The essential parts of a solid ITAD plan include:
- Secure Logistics: This means professional, GPS-tracked pickup and transportation, ensuring your assets are locked down from the moment they leave your office.
- Certified Data Destruction: This is the non-negotiable step. It ensures all data is permanently wiped using methods like physical shredding or NIST-compliant wiping, backed by a Certificate of Data Destruction for your records.
- Responsible E-Waste Management: This guarantees that all non-reusable materials are processed in an environmentally friendly way, keeping hazardous materials out of our landfills.
- Value Recovery and Remarketing: Your ITAD partner will identify functional equipment that can be refurbished and resold, generating a financial return that can help offset the cost of the service.
By treating asset retirement as a strategic function, businesses can effectively mitigate risk, ensure regulatory compliance, and even capture hidden financial value. It’s a proactive measure that safeguards your company’s future.
Beyond just data security and compliance, ITAD services play a huge role in environmental responsibility. Many companies are making bigger commitments to sustainability, and sustainable asset disposition practices fit perfectly into those goals. To get a deeper understanding of the entire process, learn more about what is IT asset disposition in our detailed guide. This framework transforms a necessary chore into a powerful tool for risk management and financial optimization.
Breaking Down The Full ITAD Process, Step By Step
A solid ITAD program isn't just about hauling away old gear. Think of it as creating a secure, documented journey for every single piece of equipment you’re retiring. From the moment it leaves your Arizona facility, each asset is tracked until its final destination—whether that's being sold, recycled, or completely destroyed. This is a strategic operation, not a simple disposal run.
The market for this is booming for a reason. Businesses are getting serious about managing old tech securely and responsibly. The global ITAD market was valued at USD 15,578.94 million in 2023 and is expected to hit USD 32,355.70 million by 2032—that's a compound annual growth rate of 8.5%. This isn't just a niche service anymore; it's a critical business function. You can read the full research about ITAD market growth to see what's driving this huge expansion.
This lifecycle chart really captures the essence of the process. It shows how we turn a potential liability—like a server full of sensitive data—into a secure, and sometimes valuable, asset.
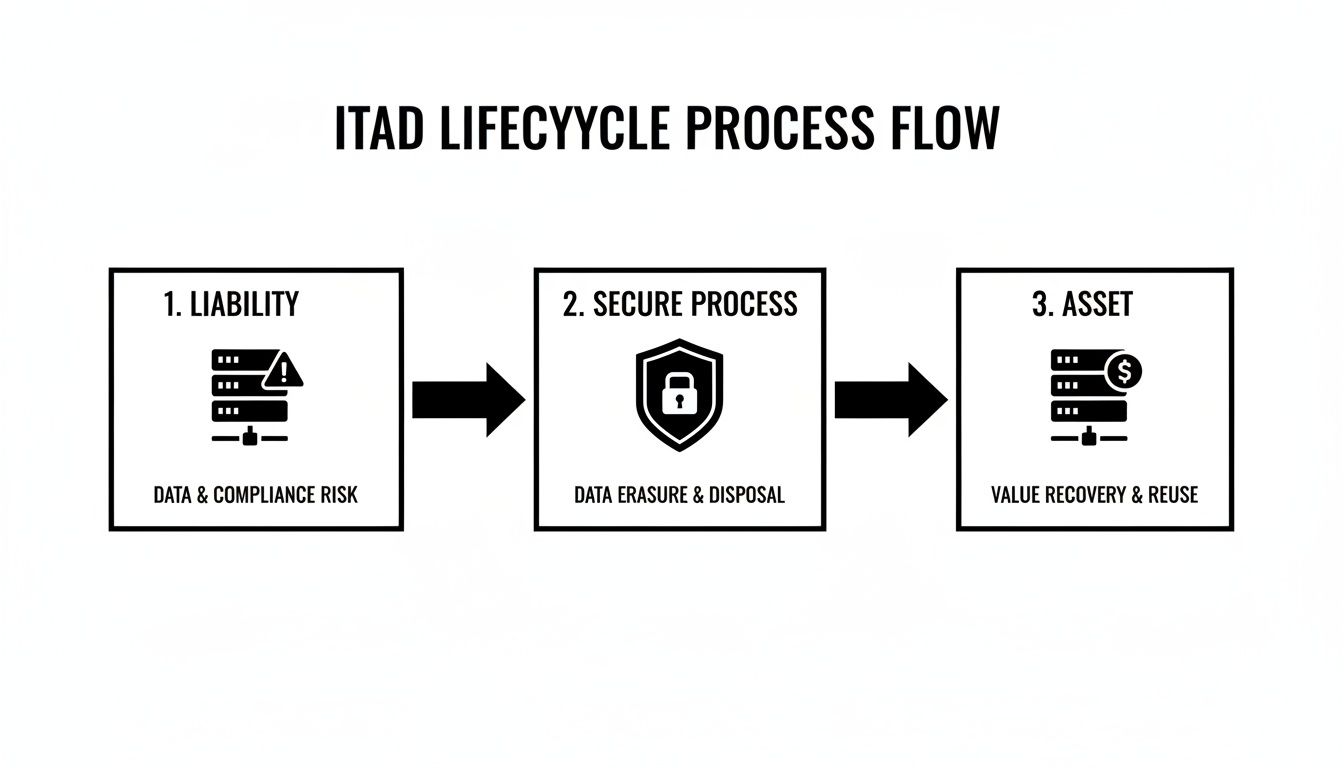
At its heart, ITAD is all about managing risk while unlocking whatever value is left in your old equipment.
On-Site Inventory and Secure Pick-Up
It all starts at your facility. The first thing a professional ITAD crew will do is conduct a detailed inventory of every asset you're retiring. Each device gets tagged and cataloged, creating the very first link in the chain of custody right there on-site.
Next comes the pick-up. This isn’t like calling a standard courier. Your assets are securely packed and loaded into GPS-tracked vehicles. It’s a dedicated logistics operation built to prevent any loss or theft from the second the equipment is out of your hands. Every move is tracked and accounted for.
Certified Data Destruction and Sanitization
Once your equipment arrives at a secure ITAD facility, anything with a hard drive or storage media is immediately separated for data destruction. This is where the real risk management happens. The method we use is tailored to your security needs and the type of device.
There are three main ways to make sure your data is gone for good:
- Data Wiping: We use specialized software to overwrite every bit of data on a drive with random characters, following standards like NIST 800-88. This renders the original data completely unrecoverable but keeps the hard drive intact and ready for reuse.
- Degaussing: For magnetic media like traditional hard drives and backup tapes, a powerful magnetic field instantly scrambles all the data. It’s a quick and total wipe, but it also makes the drive unusable afterward.
- Physical Shredding: This is the most absolute method. We feed the hard drives into industrial shredders that grind them into tiny, unrecognizable metal fragments. There's no coming back from that.
For bigger projects like taking servers offline, a little prep work goes a long way. Our detailed server decommissioning checklist can walk your team through the initial steps before we even arrive.
After the data is destroyed, you will receive a Certificate of Data Destruction. This isn't just a receipt—it's a legally binding document that proves your data has been properly eliminated and officially transfers the liability from your organization to the ITAD vendor. You'll want to keep this on file for any compliance audits.
Asset Value Recovery and Remarketing
Just because you're done with a piece of equipment doesn't mean it's worthless. The final step is to figure out if any of your assets can be resold. Our team tests, grades, and refurbishes functional gear like newer servers, networking equipment, and laptops that still have life left in them.
We then sell these refurbished assets through our established secondary markets. A good ITAD partner works on a transparent revenue-sharing model, meaning a portion of the sales proceeds comes right back to you. This can seriously offset the cost of the service, turning a compliance headache into a smart financial move for your bottom line.
Navigating Data Security and Compliance Mandates
For any Arizona business, the real risk with old technology isn’t the hardware itself—it’s the data locked inside. Every single outdated server, laptop, and phone is a potential liability, holding sensitive information that has to be permanently and verifiably wiped out. If you don't, you're opening the door to catastrophic data breaches, serious financial penalties, and a hit to your company's reputation that's hard to come back from.
This is exactly why any professional Arizona ITAD service is built around a rock-solid focus on data security and regulatory compliance.

Staying out of trouble means navigating a complex web of federal and state rules. Arizona businesses are right in the middle of these strict regulations, which spell out exactly how sensitive information must be handled from creation to its final moments.
Key Regulations Arizona Businesses Must Follow
A few major laws set the rules for data handling, and getting it wrong is more than a minor slip-up. It can trigger audits, lawsuits, and fines big enough to cripple a company.
- The FTC Disposal Rule: This federal rule hits just about every business holding consumer information. It requires companies to take "reasonable measures" to shield that info from unauthorized access when it's time for disposal.
- HIPAA (Health Insurance Portability and Accountability Act): If you're in healthcare here in Arizona, HIPAA is the law of the land. It demands that all Protected Health Information (ePHI) be made totally unreadable, indecipherable, and impossible to piece back together before the IT assets holding it are retired.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions, from local banks to investment firms, fall under GLBA. This law obligates them to protect sensitive customer financial data and ensure it's securely destroyed when it's no longer needed. Digging into the top healthcare data security solutions can offer great ideas that apply across all these regulated fields.
Choosing The Right Data Destruction Method
To keep you compliant, certified ITAD providers use several proven methods for data destruction. The right choice really depends on your company's security policies, what kind of media you're dealing with, and whether you hope to reuse the hardware.
| Data Destruction Method | Description | Best For |
|---|---|---|
| Data Wiping | Software-based overwriting that blankets existing data with random characters, making it unrecoverable. | Keeping the hard drive intact for resale or reuse while still ensuring security. |
| Degaussing | Uses a powerful magnetic field to instantly scramble all data on magnetic storage like HDDs and tapes. | Wiping large batches of magnetic media fast; the process renders the drive useless. |
| Physical Shredding | The hard drive is literally fed into an industrial shredder and ground into tiny, irreparable metal bits. | The most secure, bulletproof option for extremely sensitive data; total destruction. |
Each of these methods is designed to meet or blow past government standards. You can dive deeper into the official guidelines for media sanitization in our guide on NIST SP 800-88, which is pretty much the gold standard for data destruction.
The Importance Of A Certificate Of Data Destruction
So, after all your data is gone, how do you prove it? This is where the Certificate of Data Destruction comes in. It's a formal document that acts as your legal proof that the data on your retired assets was destroyed permanently and properly.
A Certificate of Data Destruction is way more than just a receipt. It’s an auditable, legally defensible record that officially transfers liability from your shoulders to your ITAD partner. It lists critical details like the serial numbers of the destroyed devices, the method used, and the exact date of destruction.
This certificate is your ultimate safety net. If an audit or legal question ever comes up, this single document shows you did your due diligence and followed every required step to protect sensitive information. Partnering with an ITAD provider who gives you this documentation is an absolute must for a secure and compliant asset retirement program.
Why Arizona Is a Critical Hub for Data Center Decommissioning
It's no accident that Arizona has become a magnet for massive data centers. Our state’s sunny climate, ultra-reliable power grid, and business-friendly policies have created the perfect environment for this digital infrastructure to thrive. This concentration makes Arizona a crucial nerve center for the nation's technology backbone—and as a result, a key hub for specialized Arizona ITAD services.
When these sprawling facilities upgrade or close down, the job of retiring their assets is nothing short of monumental.
Decommissioning a data center isn't just a large-scale cleanout. It’s a complex, high-stakes logistical ballet involving the methodical teardown of thousands of servers, storage arrays, networking switches, and power distribution units. Every single piece of equipment is both a potential security risk and a recoverable financial asset.
This kind of project demands a level of project management, security, and recycling muscle that very few ITAD providers can actually deliver. The sheer volume and weight of the equipment, combined with the non-negotiable need for flawless data destruction, puts data center projects in a league of their own.
The Scale of Arizona's ITAD Operations
The incredible amount of electronic hardware processed right here in Arizona is a testament to our state's capacity for handling serious, enterprise-level needs. This high volume has helped build a robust local infrastructure for managing e-waste responsibly and securely.
For instance, a single Phoenix facility recently recycled a staggering 10 million pounds of e-scrap in just one year. That figure alone shows the immense volume being handled locally and solidifies Arizona's position in the national ITAD ecosystem. You can discover more insights about Arizona's ITAD capacity on reworxrecycling.org.
This immense processing power means Arizona-based ITAD vendors are uniquely equipped to handle the intense demands of data center decommissioning. They have the logistics, security protocols, and downstream recycling partnerships to manage tens of thousands of assets from a single project.
Specialized Services for Data Center Projects
Taking on a data center decommissioning requires a specific skill set that goes way beyond typical IT asset disposal. The services are more intensive and demand precision-perfect coordination from start to finish.
Key capabilities for these large-scale projects include:
- On-Site Project Management: You need a dedicated team on the ground to oversee the entire process, from the initial inventory and asset tagging to the final sweep of the empty facility.
- De-installation and Asset Removal: This is hands-on work. Technicians have to safely de-rack servers, disconnect incredibly complex cabling, and prep heavy equipment for secure transport.
- Secure Chain of Custody: Every single asset must be meticulously tracked from the moment it’s unplugged until its final disposition. Auditable documentation at every stage is a must.
- High-Volume Data Destruction: The ability to perform on-site hard drive shredding or certified data wiping for thousands of drives is essential. This eliminates risk before any assets even leave the building.
The logistical hurdles are significant, but so is the potential for value recovery. An expert provider can identify and remarket valuable enterprise-grade components, turning what could be a costly decommissioning project into a revenue-positive event. To navigate this intricate process, it helps to understand the full scope of professional data center decommissioning services available, which further cements Arizona as a strategic destination for companies nationwide looking for a reliable, high-capacity partner for their most critical ITAD needs.
How To Recover Value From Your Retired IT Assets
Don’t look at that storage room full of old IT equipment as a pile of junk. Think of it as a hidden revenue stream just waiting to be tapped. A smart Arizona ITAD services program flips the script, changing the conversation from disposal costs to financial opportunity. This process, known as IT asset value recovery, is all about turning your retired hardware into actual capital.

The idea is pretty straightforward. Instead of just shredding and recycling everything, a certified ITAD partner will carefully evaluate each piece of equipment to see if it can be refurbished and find a new home. Functional hardware gets thoroughly tested, graded for cosmetic condition, and then sold through well-established secondary markets.
The Value Recovery Process Explained
Recovering value isn't guesswork; it's a systematic operation. Once your assets get to a secure ITAD facility and the data has been completely destroyed, technicians jump into the triage and testing phase. They meticulously sort through everything to pinpoint the items that still have market value.
This is far more than just a quick power-on test. The process involves:
- Comprehensive Diagnostics: Technicians run deep-level tests on core components like CPUs, RAM, and hard drives to make sure they are 100% functional.
- Cosmetic Grading: Every single unit is inspected for physical wear and tear—scratches, dents, you name it. It's then assigned a grade (like A, B, or C) that directly affects its final resale price.
- Refurbishment: Sometimes, minor repairs or a simple component upgrade can be performed to squeeze the maximum possible value out of an asset.
This focus on reuse is a huge priority in the industry today. To give you an idea, one major Arizona-based ITAD company processed over 275,000 assets in a single year. Out of those, more than 100,000 were successfully repaired and given a second life. This commitment to extending the lifecycle of IT hardware is what modern asset disposition is all about. You can learn more about Arizona's reuse numbers and see the real-world impact of this approach.
Which Assets Hold The Most Residual Value
Let's be clear: not all retired IT equipment is created equal when it comes to resale. While nearly all hardware has some basic commodity value, certain categories consistently deliver the biggest returns for Arizona businesses.
Assets with the strongest resale potential usually include:
- Enterprise Servers and Storage: Newer-generation servers, especially those packed with high-core-count CPUs and tons of RAM, are always in high demand.
- Networking Gear: Enterprise-level switches, routers, and firewalls from big names like Cisco often hold their value surprisingly well.
- Laptops and Desktops: Business-class laptops that are less than four or five years old are a hot commodity on the secondary market.
- Mobile Devices: Don't forget about company-owned smartphones and tablets. If they're in good shape, they can add up to a nice chunk of recovered revenue.
On the flip side, older gear like bulky CRT monitors, outdated printers, and obsolete accessories generally have little to no resale value. Those are destined for responsible recycling.
Understanding Transparent Revenue Sharing
Any reputable ITAD partner will operate on a completely transparent revenue-sharing model. This simply means that after your refurbished assets are sold, you get a predetermined cut of the net proceeds. The entire process should be crystal clear and fully documented.
A detailed value recovery report is non-negotiable. This report should give you a complete, itemized breakdown of what sold, the price each piece fetched, and the precise calculation of your share. This level of transparency is key to having a clear financial record of your asset retirement program.
The capital you recover can be a game-changer. Many of our clients use these funds to directly offset the cost of our ITAD services, making the whole program budget-neutral or even profitable. Others reinvest that money right back into new technology, turning an end-of-life process into the start of a new tech cycle. It’s what makes your IT asset retirement program a truly smart, financially sound move for your organization.
Choosing The Right Arizona ITAD Partner for Your Business
Picking an ITAD vendor in Arizona is a bigger deal than most people think. This decision directly impacts your company’s security, compliance, and even its reputation. A great partner is like a shield, protecting you from nasty data breaches and steep regulatory fines.
But the wrong one? They can expose you to a world of risk. This choice goes way beyond just comparing price tags.
Your entire evaluation has to be built on a foundation of verification and trust. The first and most important thing to check is a potential partner's certifications. These aren't just fancy badges; they're independent proof that their processes are up to snuff and that they're committed to doing things the right way.
Verifying Certifications and Standards
In the world of ITAD, certifications are completely non-negotiable. They're your guarantee that a vendor is following the highest standards for data security, environmental responsibility, and keeping their own workers safe. Before you even think about signing a contract, make sure they hold current, industry-leading credentials.
You'll want to look for these two heavy-hitters:
- R2v3 (Responsible Recycling): This is one of the top-tier standards in the industry. It ensures vendors are using safe and sustainable practices for everything from data sanitization to final electronics recycling. It’s a comprehensive playbook for managing the entire lifecycle of your old equipment.
- e-Stewards: Another premier certification, e-Stewards is famous for its incredibly strict environmental rules. One of its key promises is a flat-out ban on exporting hazardous e-waste to developing countries, which is a huge ethical and environmental win.
These certifications mean a vendor’s facility and processes have been thoroughly audited and approved by an objective third party. That should give you the confidence you need to trust them with your sensitive gear.
When you're vetting a potential partner, don't just take their word for it. Ask them to show you copies of their current certification documents. A transparent, trustworthy vendor will have zero problem providing this proof and will be happy to show their commitment to compliant operations.
Essential Questions to Ask a Potential ITAD Vendor
Certifications are the entry ticket, but your vetting process shouldn't stop there. You need to dig deeper by asking direct, specific questions about their day-to-day procedures and capabilities. Their answers will tell you everything you need to know about their level of expertise and whether their services are a good fit for your business.
Your checklist of questions should absolutely include these topics:
- Chain-of-Custody Documentation: How do you track my assets from the moment they leave my building to their final disposition? Ask to see a sample chain-of-custody report. It should be detailed, clear, and auditable.
- Data Destruction Methods: What specific methods do you use? Are you wiping drives to NIST 800-88 standards, or are you physically shredding them? Crucially, confirm they provide a Certificate of Data Destruction for every single project.
- Logistics and Security: Do you use your own fleet of trucks or do you subcontract? What security measures do you have in place during transport, like locked trucks and GPS tracking?
- Value Recovery Model: How exactly do you handle reselling our equipment? You'll want to request details on their revenue-sharing process and the kind of reporting they provide to make sure everything is completely transparent.
Making the right call means getting a clear picture of how different vendors operate. To help you sort through your options, you can learn more about the key factors to weigh when comparing IT asset disposition companies in our detailed guide. Choosing the right partner isn't just about getting rid of old gear; it's about gaining peace of mind and turning asset retirement into a secure, strategic advantage.
Frequently Asked Questions About ITAD Services
When it's time to retire old IT gear, Arizona businesses naturally have questions about how it all works, what it costs, and what happens to their data. Making a smart, confident decision starts with getting clear answers. Here are a few of the most common questions we hear every day.
What Kinds of Business Equipment Do You Handle?
We are equipped to manage virtually any commercial, enterprise, or specialized IT equipment for your business. Our Arizona ITAD services are designed exclusively for business environments, from complex data center hardware and laboratory or medical equipment to standard office electronics.
We securely process a huge range of assets, including:
- Servers, storage systems (SAN, NAS), and all types of networking gear.
- Laptops, desktops, and powerful workstations.
- Specialized electronics from industries like healthcare, manufacturing, and R&D labs.
- Medical and laboratory equipment.
Please note: our services are focused strictly on commercial and enterprise asset disposition. We do not process consumer electronics or residential e-waste.
How Is Our Data Kept Secure During the Process?
Data security isn't just a feature of our ITAD process—it's the absolute foundation. We maintain a rock-solid, documented chain of custody from the second our team steps into your building until we issue the final destruction certificate. Your sensitive information is locked down and protected at every single stage.
We offer both on-site and off-site data destruction to fit your security protocols. This includes mobile hard drive shredding right at your location and data wiping that meets the rigorous NIST 800-88 standards. Once complete, you receive a formal Certificate of Data Destruction, giving you the legal proof needed to satisfy any compliance audit.
Do You Offer Pickup Services Throughout Arizona?
Absolutely. Our logistics network is nationwide, which means we provide secure, scheduled pickups for businesses across the entire state of Arizona. You don't have to worry about the transportation details; we manage all the logistics to make sure your assets get from your site to ours smoothly and securely.
Whether your enterprise is in a major hub like Phoenix, Tucson, and Scottsdale or in a more remote commercial location, our team can provide secure pickup and transport.
Can We Recover Any Financial Value From Our Old Equipment?
Yes, and you absolutely should! Value recovery is a huge part of a smart ITAD strategy. Instead of just being a line-item cost, retired IT can actually become a source of revenue. We meticulously audit every asset that comes through our doors to see what still has life left in it.
Equipment that still has market demand is professionally tested, graded, and prepared for resale. We work on a completely transparent revenue-sharing model, returning a significant portion of the proceeds directly to you. This financial return often helps offset—or even exceed—the costs of the service.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. Schedule your nationwide pickup today by visiting us at https://sonitechllc.com.