Your network team finishes a carrier upgrade. The new gear is live, but the old equipment is still sitting in a cage, a branch closet, or a warehouse row marked “hold for later.” Weeks pass. Finance wants the space back. Security wants the drives handled correctly. Operations wants the project closed.
That’s where telecom equipment liquidation stops being a cleanup chore and becomes a business decision. If you handle it well, you reduce risk, recover value, and close the loop with clear documentation. If you handle it poorly, you create audit exposure, resale losses, and chain-of-custody problems that follow you long after the equipment is gone.
Why Telecom Liquidation is a Priority Now
Many IT directors are dealing with the same pattern. A fiber refresh, data center consolidation, or telecom modernization leaves behind stacks of routers, optical gear, radios, cabinets, shelves, and power equipment that no longer fit the production environment. The equipment may still work. It may even have resale demand. But once it loses a place in your roadmap, it turns into idle capital and operational drag.
The timing matters. The global telecom equipment market saw a historic 11% revenue decline in 2024, the sharpest drop in over two decades, which pushed broad liquidation of excess inventory across segments including RAN, optical transport, and routers, according to CSI reporting on Dell’Oro findings. That matters to an enterprise IT team because oversupply changes buyer behavior, pricing expectations, and how quickly assets lose value when they sit untouched.
What this looks like inside an organization
A common scenario starts with good intentions. Someone says the old telecom gear might be useful for spares, a lab, or a future site. So it stays in place.
Then the hidden costs show up:
- Storage pressure: Valuable floor space gets tied up by equipment no one is actively using.
- Security uncertainty: Nobody is fully sure what configuration data, credentials, or customer information remains on the devices.
- Ownership confusion: Facilities, network operations, procurement, and compliance all assume another team is tracking the disposition.
- Budget leakage: Assets with remarketing value age into lower-value equipment.
Practical rule: If equipment has no approved future use, treat it as an end-of-life asset and move it into a controlled disposition process.
This is also why many organizations tie liquidation to broader sustainability and reporting goals. A decommission project can support internal governance when the company documents responsible recycling, recovery, and downstream handling. Teams that already manage environmental reporting often connect this work to programs like ESG electronics recycling in Georgia.
Why waiting gets expensive
Telecom equipment liquidation works best before the project becomes urgent. Distressed timelines invite rushed pickups, weak documentation, and low offers. Planned liquidation gives you time to sort assets, verify data-bearing components, separate resale candidates from scrap, and align the process with legal and procurement requirements.
The difference is simple. Reactive disposal removes clutter. Strategic liquidation protects the business.
The Complete Telecom Liquidation Lifecycle
The safest projects follow a repeatable lifecycle. That keeps finance, legal, security, and operations aligned from the first inventory review to the final certificate package.
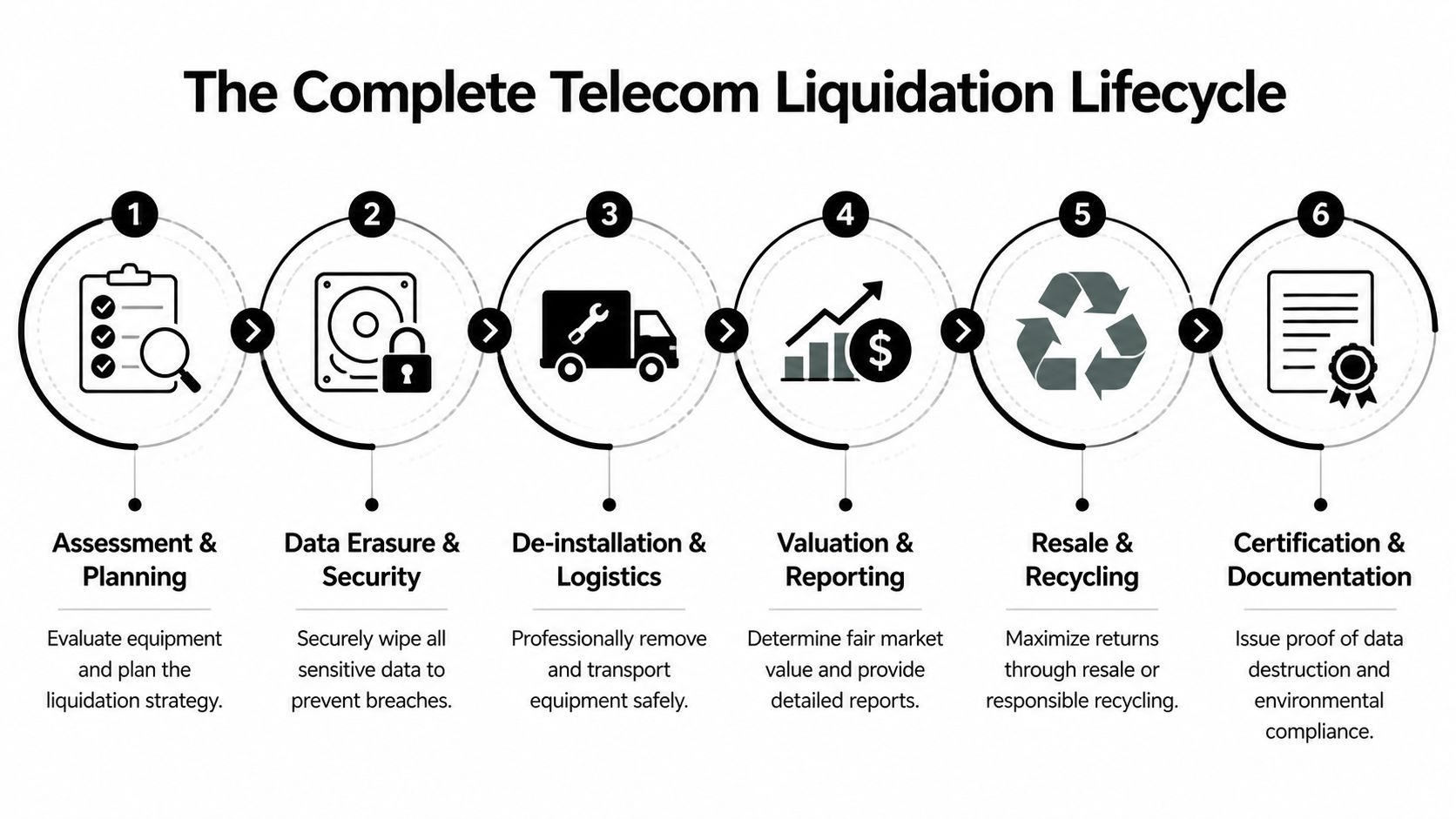
Asset inventory and audit
Start with a physical and logical inventory. Don’t rely only on a spreadsheet from procurement or a CMDB export. Telecom environments often contain moved, swapped, cannibalized, or partially documented hardware.
At minimum, capture:
- Manufacturer and model: Cisco ASR, Juniper MX, Nokia, Ericsson, Huawei, APC, Dell, HPE, and similar product families need accurate identification.
- Serial numbers: These support chain-of-custody, valuation, and audit records.
- Condition notes: Working pull, damaged, incomplete, tested, untested, or parts-only.
- Site details: Rack position, room access limits, loading dock access, and removal constraints.
- Data-bearing components: SSDs, hard drives, controller modules, management cards, and removable media.
A strong audit also separates telecom transport gear from standard IT assets. That matters because each category may need different buyers, test methods, and removal crews.
Fair market valuation
Valuation is where many projects go sideways. Book value doesn’t equal market value, and “used network equipment” is too broad a category to price accurately.
Good valuation looks at:
- Age and support status: Mid-life equipment may still attract buyers. Near-obsolete gear usually shifts toward parts harvest or recycling.
- Configuration: Line cards, optics, memory, power modules, and licenses can change resale potential.
- Market saturation: If many similar units are hitting the market at once, pricing softens.
- Completeness: Chassis-only listings usually underperform complete, tested systems.
Some organizations fold this into a broader IT asset lifecycle management process so liquidation decisions happen before the assets become distressed.
The best time to value telecom equipment is before the warehouse fills up, not after the CFO asks why it’s still there.
Secure data sanitization and destruction
This is the step new IT directors often underestimate. Telecom gear isn’t just “network hardware.” It can store routing tables, subscriber-related records, site configs, VPN credentials, authentication material, and internal topology data.
To be considered secure, data destruction must achieve DoD 5220.22-M 3-pass overwrite or physical shredding, and incomplete wiping on modern SSDs can leave 5-10% of data remnants detectable with forensic tools, as described in telecom liquidation data destruction guidance. Certified sanitization aligned to NIST 800-88 is the standard most enterprise teams want in place.
Three common methods apply:
- Logical wiping: Best for devices that can be securely sanitized and resold.
- Degaussing: Useful in certain magnetic media scenarios, though less relevant for many newer solid-state assets.
- Physical shredding: Best when the media is damaged, inaccessible, or too sensitive to release.
Choose the method based on media type and the organization’s risk posture, not convenience.
Logistics and reverse logistics
This phase covers de-installation, packing, staging, transport, and receipt verification. It sounds routine until the first site has no freight elevator, no pallet jack clearance, and no after-hours loading permission.
The practical questions matter:
- Who removes the gear from racks or cabinets
- How fragile optics, cards, and power modules are packed
- Whether chain-of-custody starts onsite
- How sealed containers or serialized pallets are tracked
- What happens to accessories, rails, cables, and transceivers
A weak logistics plan can erase the value recovered in earlier phases.
Final asset disposition
Everything doesn’t go down one path. A good telecom equipment liquidation project usually splits assets into several streams:
- Resale: Functional, marketable equipment with demand
- Refurbishment: Equipment that needs testing, cleaning, or minor remediation
- Parts harvesting: Chassis with useful modules, fans, power supplies, or optics
- Recycling: Commodities and low-demand items processed responsibly
- Destruction: Assets that are damaged, sensitive, or non-compliant for resale
The end result should be a clean reporting package. That includes asset lists, serialized outcomes where possible, certificates, and settlement details.
Strategies for Maximum Value Recovery
Many companies still treat liquidation as a disposal line item. That’s usually a mistake. The better view is financial triage. Which assets should be sold whole, which should be refurbished, which should be broken for parts, and which should go straight to compliant recycling?

Remarketing beats scrap when the gear is prepared correctly
For the right asset classes, secondary markets are active. Enterprise-grade networking gear and servers aged 3-5 years can recover 15-30% of original purchase price when they’re properly processed with certified NIST 800-88 sanitization, and that certification can increase resale prices by 15% or more, according to this valuation and liquidation analysis.
That number only applies when the basics are done right. Buyers pay more for equipment that is:
- Properly identified: Exact model and installed modules are known
- Sanitized and documented: The buyer doesn’t have to guess about security risk
- Complete: Power supplies, cards, bezels, and rails are included when relevant
- Handled carefully: Cosmetic and shipping damage are minimized
Three recovery paths with different outcomes
A smart project doesn’t force all assets into one channel.
| Path | Best fit | Main advantage |
|---|---|---|
| Remarketing | Working, in-demand gear | Highest potential recovery |
| Refurbishment | Functional gear needing prep | Broadens the buyer pool |
| Materials recycling | Obsolete or damaged gear | Clears inventory responsibly |
If your team needs a primer on how buyers think about pricing and sale format, this guide to learn asset valuation and marketing is a useful complement to ITAD planning.
Clean data, complete listings, and accurate configuration details usually matter more than optimistic asking prices.
What usually holds value
In telecom environments, value often survives longer in backbone and enterprise-class hardware than in miscellaneous accessories. Carrier and enterprise buyers tend to look first at routers, switches, optical platforms, servers, and supporting power gear that still fit deployed environments.
A specialist buyer network provides assistance. Some firms, including telecom equipment buyers, evaluate gear for resale potential before defaulting to scrap. That distinction matters because scrap is the floor, not the strategy.
The practical takeaway is simple. Don’t ask, “How do we get rid of this?” Ask, “Which channel gives each asset its best outcome?”
Navigating Compliance and Documentation Requirements
A liquidation project can fail even when the truck shows up on time and the warehouse gets cleared. The failure happens later, during an audit, a legal review, a customer questionnaire, or a security incident response. If you can’t prove what happened to the equipment and the data it held, you own the uncertainty.
Why the paperwork matters
Telecom gear often contains more sensitive information than nontechnical stakeholders expect. A retired router or baseband component may still hold configuration files, network diagrams, customer-related data, internal credentials, or location-specific information.
That creates several layers of risk:
- Privacy risk: Sensitive information may remain on storage media or embedded systems.
- Regulatory risk: Disposal practices can conflict with retention, destruction, or environmental requirements.
- Contract risk: Customers and partners may require proof of secure disposition.
- Audit risk: Missing records make it hard to demonstrate due diligence.
The solution isn’t just “erase the drive.” The solution is an auditable process backed by evidence.
What documents you should expect
At the end of a professional telecom equipment liquidation project, your file should tell a complete story. The exact format varies, but strong documentation usually includes:
- Asset inventory records: What was collected, by model and serial where available
- Chain-of-custody documentation: Who handled the assets and when custody changed
- Certificates of data destruction: Proof that sanitization or shredding was completed
- Certificates of recycling: Proof of downstream environmental handling
- Settlement reporting: What was resold, recycled, destroyed, or held back
For organizations aligning sanitization decisions to federal guidance, this overview of NIST SP 800-88 practices is often the reference point.
Documentation is how you transfer liability from assumption to evidence.
The business impact of weak records
When records are incomplete, small problems become expensive questions. Legal asks whether regulated data may have left the site. Procurement asks whether an approved vendor handled the shipment. Internal audit asks why asset tags disappeared from the fixed-asset rollforward. Security asks whether any media was destroyed or merely removed.
None of those questions are theoretical. They affect renewals, cyber questionnaires, insurer discussions, and board-level reporting. Good documentation doesn’t slow the project down. It’s what makes the project defensible.
Common Pitfalls in Telecom Equipment Liquidation
The lowest quote often looks attractive when your team is under pressure to clear a site fast. But cheap liquidation can become expensive disposal once missing data controls, weak packaging, and poor reporting start to surface.
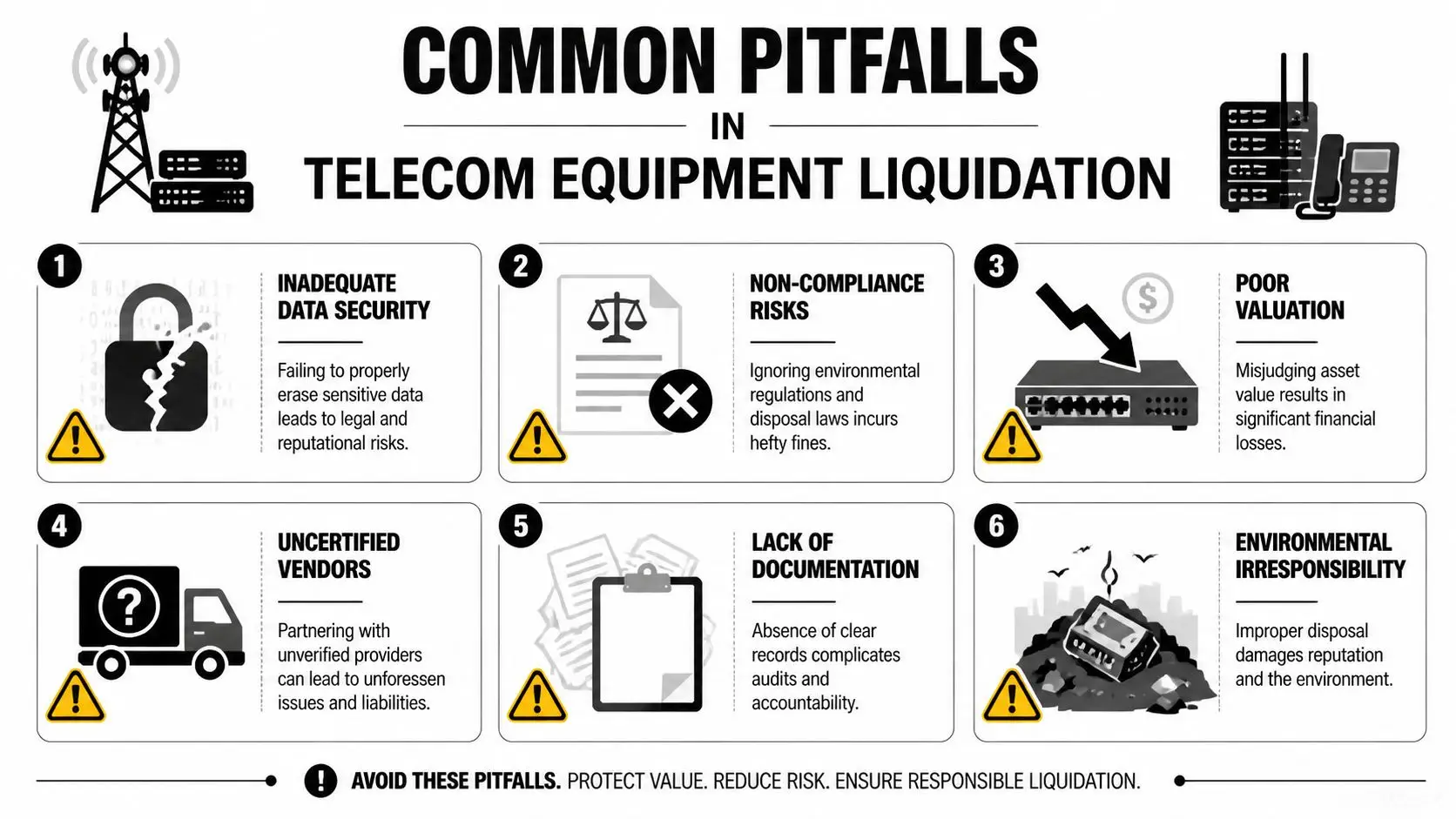
Fire-sale timing destroys leverage
The clearest warning sign is waiting too long. A distressed seller has fewer options, less time to sort assets, and less room to negotiate channel strategy.
A stark example came in 2025, when Tilson Infrastructure, with $361 million in assets, sold for $22 million in a bankruptcy auction, or less than 6% of book value, as reported by Wireless Estimator’s coverage of the sale. That’s an extreme case, but it illustrates the central lesson. Once liquidation turns into a forced event, buyers gain the advantage.
The mistakes that show up most often
Some errors are predictable because teams repeat them across industries.
- Treating all gear as scrap: This collapses resale candidates into low-value commodity disposal.
- Skipping configuration detail: A chassis with unknown cards or missing power supplies attracts lower bids.
- Using a generic hauler: Transport without technical handling can damage optics, line cards, and fragile assemblies.
- Forgetting embedded media: Teams remember hard drives, but miss flash modules, SSDs, and management storage.
- Accepting vague reporting: “Picked up and processed” isn’t enough for audit or legal review.
Why low-cost vendors can cost more
The cheapest provider may quote a simple pickup fee and promise fast removal. That sounds efficient. It isn’t always controlled.
A better screening question is this: can the vendor explain exactly how they handle serialized intake, data-bearing components, testable telecom gear, and final reporting? If the answer is vague, your project is being priced like junk removal instead of managed asset disposition.
A low bid can hide missing services. De-installation, sanitization, packaging, and reporting are where risk usually lives.
The biggest pitfall is assuming liquidation starts when the truck arrives. It starts much earlier, with planning, classification, and evidence.
How to Select a Certified ITAD Partner
Telecom liquidation volumes rise and fall in waves. History shows why specialized help matters. U.S. telecom capital spending ramped up 206% from 1994 to 2000 before the dot-com bust triggered broad equipment liquidation, according to market history summarized in this telecom equipment report. When those cycles turn, companies need a partner that can handle security, logistics, and recovery without improvising.

What to look for first
Start with operational credibility, not the sales deck. You need a vendor that can explain process in plain language and back it up with records.
Focus on four areas:
- Certifications and controls: Ask how the company manages downstream vendors, environmental handling, and documented data destruction.
- Security protocols: Confirm chain-of-custody, site procedures, employee controls, and handling of data-bearing devices.
- Logistics capability: Ask whether they coordinate de-installation, packing, palletization, and nationwide pickup.
- Reporting depth: Make sure they provide usable inventory and disposition records, not just a simple receipt.
Questions worth asking in the first call
A short vendor interview can reveal a lot. Ask direct questions and listen for precise answers.
- How do you identify data-bearing components in telecom gear?
- What sanitization or destruction methods do you use for SSDs and hard drives?
- Can you support site de-installation, or only dock pickup?
- How do you separate resale, parts harvest, and recycling streams?
- What final documentation do you issue after project closeout?
If your procurement team wants a structured review process, a vendor due diligence checklist can help standardize comparisons between providers.
What a real partner does differently
A qualified ITAD partner doesn’t just move equipment. They help your team make better end-of-life decisions. In practical terms, that means flagging high-value equipment before it is scrapped, identifying sensitive media before it leaves the building, and producing records your compliance team can use.
One example is Beyond Surplus, which provides services such as secure data destruction, telecom equipment buyback, de-installation support, and documentation for business clients. The important point isn’t brand preference. It’s choosing a partner that can handle the full chain from removal through final disposition with evidence at each step.
Transform Your Surplus into a Strategic Asset
Telecom equipment liquidation works best when you treat it as part of asset management, not emergency cleanup. Old routers, optical shelves, radios, servers, and support gear can create three very different outcomes. They can become compliance risk. They can become scrap. Or they can become recovered value with a documented chain of custody.
The difference usually comes down to timing, process, and partner selection. Inventory the assets carefully. Sanitize data with defensible standards. Match each item to the right disposition channel. Keep the paperwork tight enough for legal, finance, security, and sustainability teams to trust.
If you’re sitting on surplus telecom hardware now, don’t wait for the project to become a fire sale. A structured liquidation plan gives your team more control, clearer reporting, and better financial outcomes.
Beyond Surplus helps organizations manage telecom equipment liquidation with secure data destruction, compliant recycling, value recovery, and nationwide pickup coordination. If your team is planning a decommission, refresh, or site cleanup, contact Beyond Surplus for certified electronics recycling and secure IT asset disposal.