A network refresh usually ends the same way. The new gear is live, the old routers and PBX shelves are boxed in a back room, and someone in IT gets asked a simple question that isn’t simple at all: who buys this stuff, and how do we sell it without creating a security problem?
That pile of decommissioned telecom hardware can be recovered for value, but it can also carry stored configurations, credentials, call records, and disposal liability. The companies that buy telecom equipment vary widely. Some know telecom inside and out. Some only want scrap weight. Some talk about cash and skip the paperwork that protects your business.
Your Guide to Selling Used Telecom Equipment
An IT manager finishes a voice migration, clears out legacy Avaya phones, Cisco routers, and a few session border controllers, then starts calling buyers. The first offer sounds attractive, but the buyer doesn’t ask for serials, storage details, or sanitization requirements. That’s the moment the sale stops being a resale decision and becomes a risk decision.
Used telecom gear has two lives at once. It has remarketing value if the equipment is complete, tested, and still in demand. It also has compliance exposure if the devices hold network settings, user data, or customer information. Treating the transaction like a simple surplus sale usually leaves money on the table and control gaps in the process.

Teams that handle this well start with three priorities:
- Know what you have: Build an accurate equipment list before requesting bids.
- Control data risk: Assume routers, PBX systems, and telecom servers retain data until proven otherwise.
- Demand documentation: A verbal promise is useless once the equipment leaves your dock.
A practical starting point is reviewing a telecom resale process that focuses on inventory, pickup, and disposition controls at where to sell telecom equipment.
The best sales process doesn’t begin with price. It begins with asset identification and liability control.
The Landscape of Telecom Equipment Buyers
Not all buyers serve the same purpose. Some buy to refurbish and resell. Some buy to harvest parts. Others act as intermediaries and shop your list to their network. If you choose the wrong category, the transaction gets slower, less secure, and less profitable.
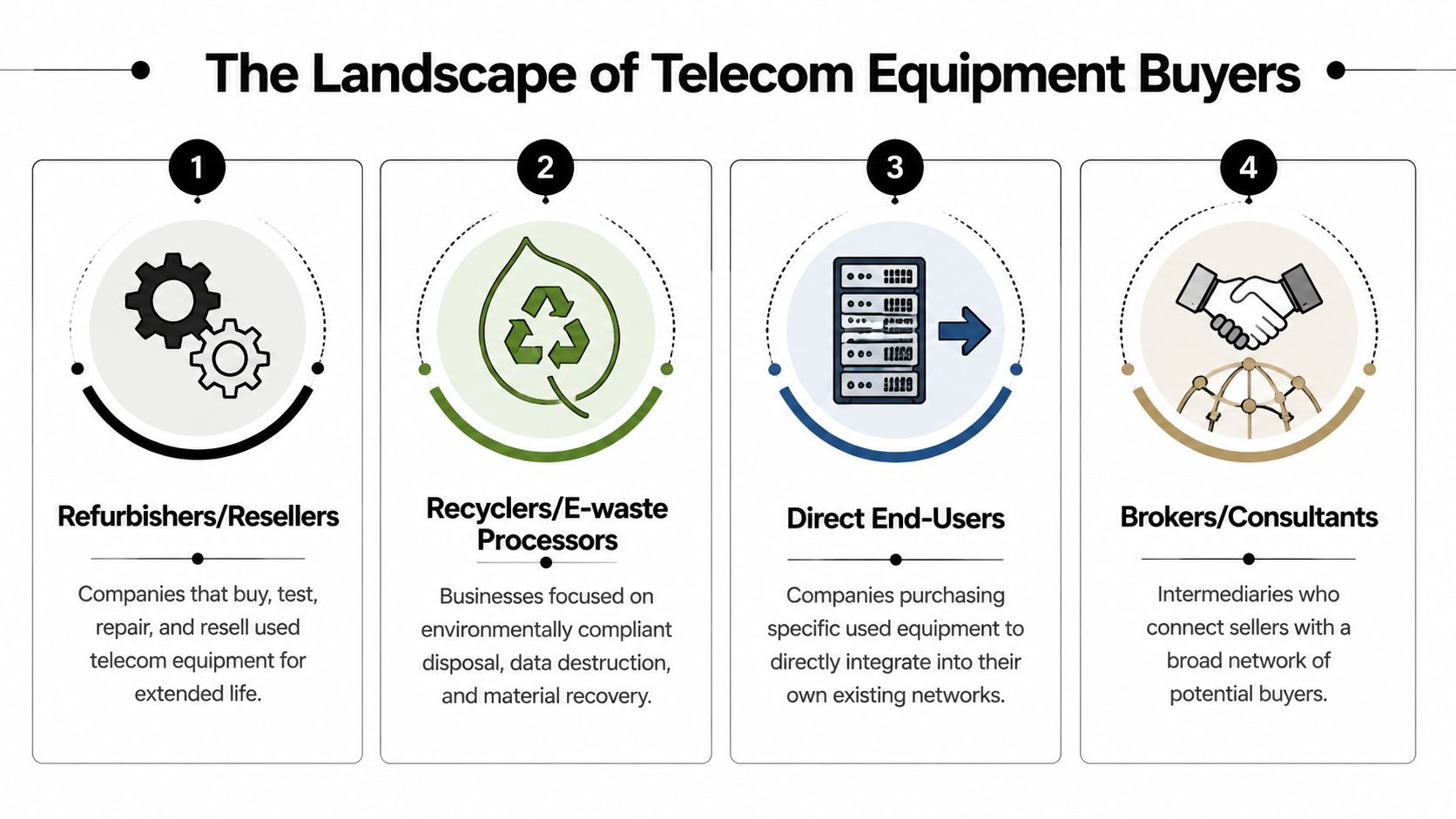
ITAD providers and secure disposition firms
An ITAD provider handles the full chain. That usually includes audit support, logistics, secure data destruction, resale, and recycling for what can’t be remarketed. This model fits organizations that care as much about paperwork and chain of custody as they do about payout.
The market still revolves around major telecom buyers. Telcos hold 71.25% market share in telecom equipment purchasing, while private 5G demand from enterprise and industrial buyers is projected to grow at a 14.62% CAGR from 2026 to 2031, according to Mordor Intelligence telecom equipment market data. That matters in the secondary market because buyer demand isn’t limited to carriers anymore. Enterprises, integrators, and industrial network operators are also sourcing specialized gear.
Brokers and telecom resellers
A broker usually doesn’t want every asset. They want the assets they can move quickly. That can work well for clean, desirable lists with current Cisco, Juniper, Avaya, Nokia, or optical inventory. It works poorly when your lot includes mixed condition equipment, untested shelves, missing accessories, or end-of-life gear.
Brokers can be useful if you already know your inventory and can tolerate a narrower scope. Some channel-focused firms also support resale relationships through programs such as the Sheridan Technologies reseller program, which shows how structured resale networks can help place business technology assets through established partner channels.
Recyclers and material recovery firms
A recycler is the right choice when the main objective is compliant downstream processing, not remarketing. If the equipment is obsolete, physically damaged, incomplete, or low-demand, recycling may be the most efficient route. The trade-off is obvious. Material recovery rarely matches the return available through tested reuse.
Direct end users
A direct buyer may want a very specific module, handset family, power supply, or optical configuration to support an installed base. These deals can produce strong returns, but they’re inconsistent. Most businesses don’t have time to locate direct users for every item in a telecom room.
Here’s the practical comparison:
| Buyer type | Best for | Main advantage | Main limitation |
|---|---|---|---|
| ITAD provider | Mixed lots and regulated environments | Security, documentation, logistics | May not be highest bid on a single premium item |
| Broker/reseller | Marketable telecom gear | Fast resale focus | Often selective |
| Recycler | Obsolete or damaged assets | Compliant disposition | Lower recovery |
| Direct end user | Specific in-demand items | Strong fit for exact need | Hard to source consistently |
For companies comparing local and national options, a useful benchmark is how firms describe telecom intake, evaluation, and pickup at telecom equipment buyers near me.
How Buyers Determine the Value of Your Telecom Assets
The offer doesn’t come from a model number alone. Buyers price telecom equipment based on resale probability, test results, configuration completeness, and how much work they’ll need to do before the gear can move again.

The first pass is inventory quality
A serious buyer starts with your list. They want manufacturer, model, quantity, serial number, installed modules, optics, power supplies, rack ears, and license status where relevant. A vague spreadsheet with “Cisco switches” forces the buyer to price defensively.
If you want stronger bids, give buyers enough detail to estimate remarketing value without guessing.
Testing changes the economics
Testing is where value separates from scrap. According to RQ Communications on selling telecom equipment, surplus telecom gear can lose 50% of its value within 6 to 12 months post-End-of-Life, untested gear fails 25% to 35% of post-purchase quality control, and fully tested equipment can reach up to 85% of list price on the secondary market.
That explains why two offers on the same part can be far apart. One buyer is pricing for verified resale. The other is pricing for uncertainty, returns, and repair.
Practical rule: If your team can document condition, boot status, included modules, and license posture, the buyer doesn’t have to build as much risk into the offer.
What usually increases value
Some factors are straightforward, others get missed all the time.
- Complete configurations: Chassis with matching cards, power supplies, and rails are easier to resell.
- Known-good testing status: Booted, wiped, and documented gear attracts more confidence.
- Recognizable enterprise brands: Cisco, Avaya, Mitel, Nokia, and similar lines tend to have established secondary demand.
- Timing: Equipment sitting too long after replacement often falls into a weaker resale window.
What hurts your number fast
Buyers discount hard when they see friction.
- Untested lots: Unknown condition turns a resale project into a repair gamble.
- Missing components: A shelf without the right cards or power setup may be worth parts value only.
- Poor storage: Dust, corrosion, broken ports, and mixed pallets signal avoidable risk.
- License ambiguity: Telecom systems with unclear entitlements are harder to place.
A disciplined valuation process isn’t complicated. It’s just detailed. The more of that detail you provide up front, the less room there is for a buyer to downgrade the deal later.
Critical Documentation for a Secure and Compliant Sale
The equipment isn’t your biggest exposure. The missing paperwork is.
Telecom hardware often stores more than people expect. Routers, PBX platforms, session border controllers, and related servers can retain credentials, call detail information, IP configurations, and other sensitive records long after they’ve been powered down.
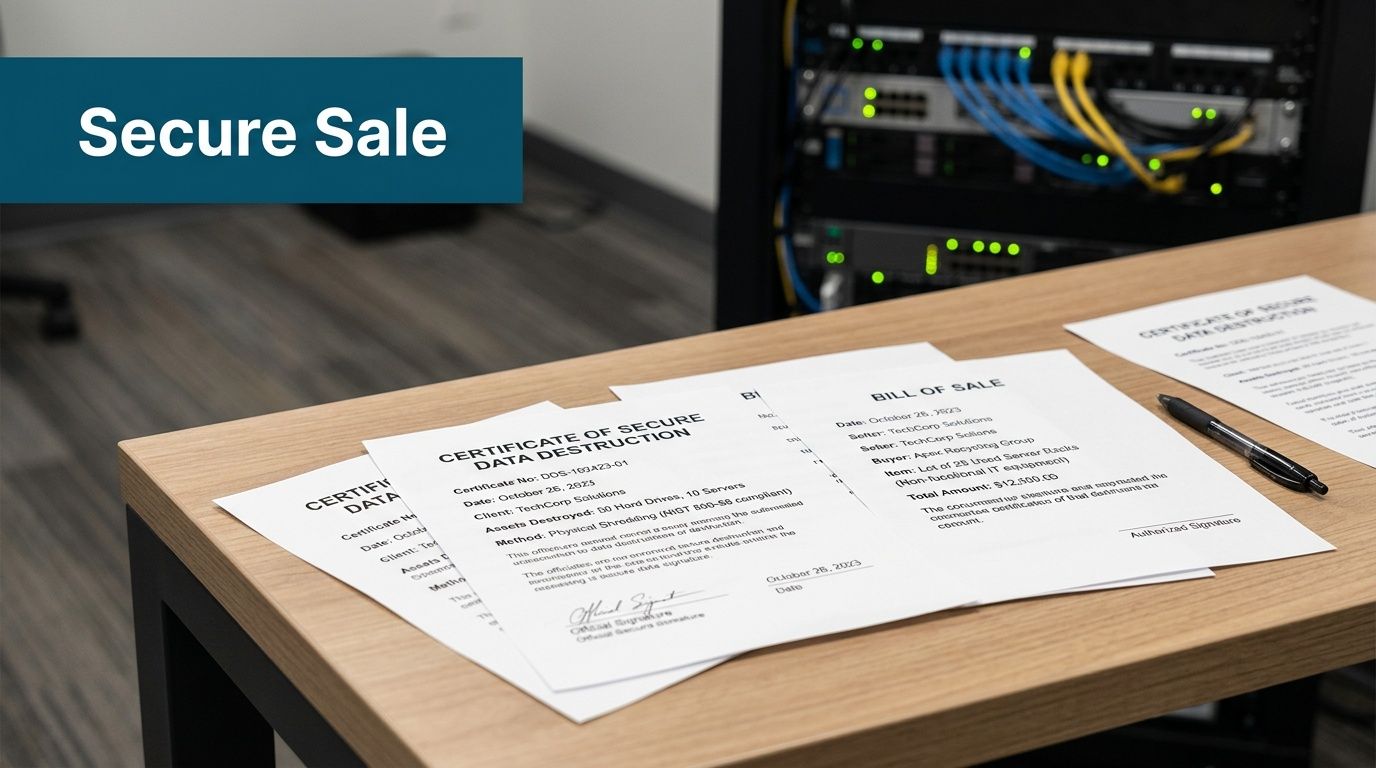
Why certificates matter
A compliance audit cited by Beyond Surplus telecom surplus buyers guidance found that 68% of decommissioned telecom assets retained recoverable data even after common reset workflows. That’s why reputable buyers require NIST 800-88-compliant wiping or physical destruction and issue certificates that transfer liability away from the seller.
If a buyer says a factory reset is enough, that’s not a process. That’s a warning.
The documents you should require
Ask for these before pickup, not after a dispute.
- Certificate of Data Destruction: This should identify what was sanitized or destroyed and connect back to your asset list.
- Certificate of Recycling: You need confirmation for equipment that can’t be reused and must be processed responsibly.
- Chain-of-custody record: This shows who handled the assets from your site to final processing.
- Bill of sale or settlement record: It should state what changed hands and under what terms.
A company that can’t explain its documentation package usually can’t defend it during an audit.
Certifications and process proof
Industry certifications don’t replace due diligence, but they’re a strong screening tool. They show whether the company operates under a documented system instead of informal handling. Businesses that need a baseline for what certification-backed controls look like can review electronics recycling certification requirements.
If the buyer won’t commit to auditable records, keep the equipment in your facility until you find one who will.
In regulated sectors, documentation is what turns a hardware pickup into a defensible disposition event. Without it, you may still own the risk long after the pallets leave.
Preparing Your Telecom Equipment for a Successful Sale
The fastest way to lower your return is to hand over mixed equipment with no list, no accessories, and no internal owner. Buyers slow down when they have to sort your inventory for you.
A better approach is operational. Assign one owner, build one master list, and stage the equipment as if you’re preparing for a site audit. That saves time for both sides and reduces price revisions after pickup.
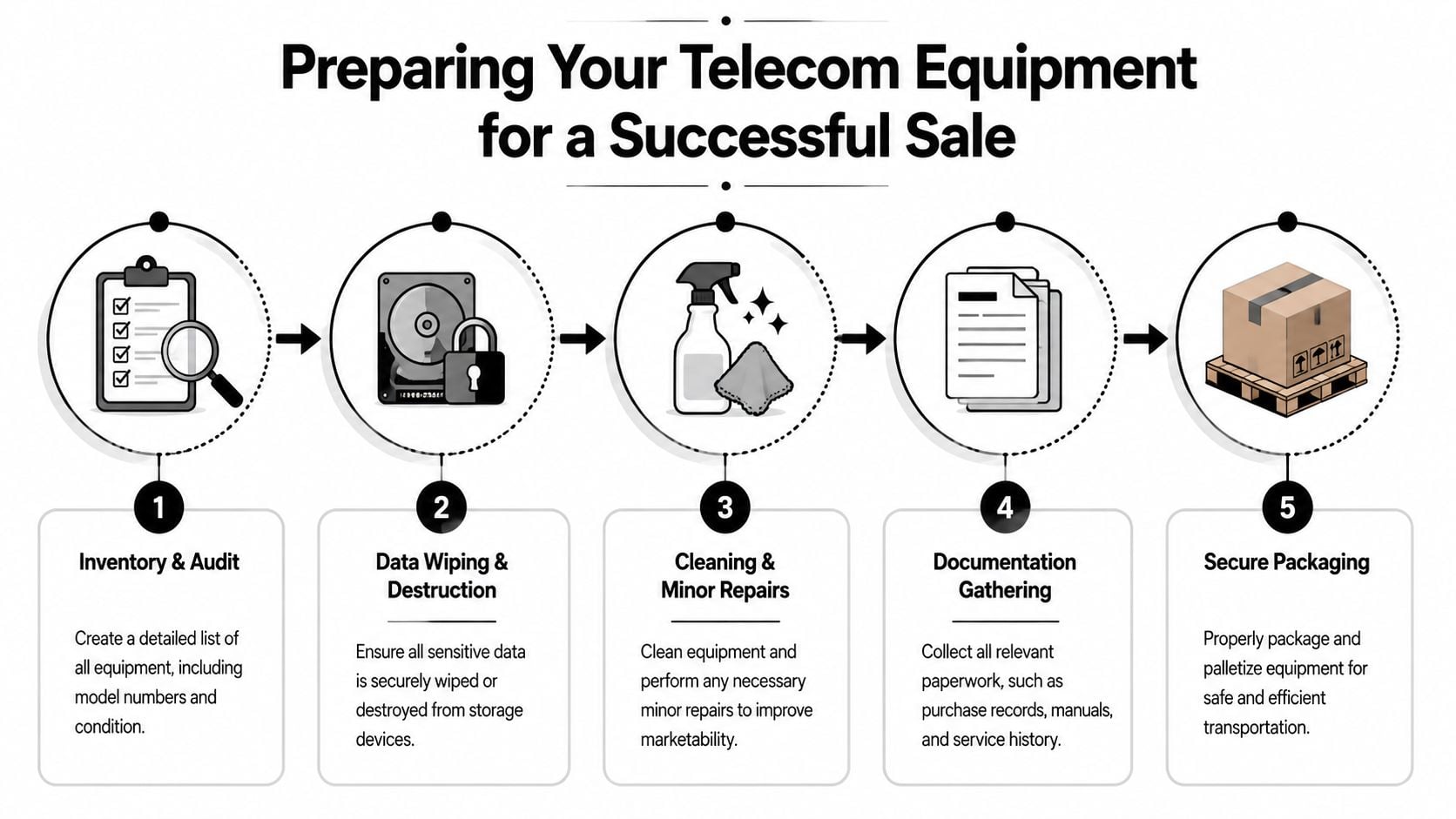
Start with an internal asset sweep
Walk the telecom closets, MDFs, IDFs, data rooms, and storage areas. Don’t rely on memory or an old procurement report. The actual resale lot often includes forgotten spares, line cards, handsets, optics, and power modules that never made it into the retirement plan.
Use a checklist like this:
- Record model and serial data from each device.
- Note installed components such as cards, SFPs, transceivers, and power supplies.
- Separate tested from untested gear so the buyer can quote correctly.
- Flag anything with storage for sanitization handling.
- Identify missing accessories before the buyer does.
Bundle what belongs together
Telecom assets sell better as complete working sets. A PBX chassis with the right cards, licenses, and power units is easier to place than loose parts in separate boxes. The same goes for routers with matching modules and optics.
Small details matter. Rack ears, faceplates, handsets, expansion modules, and manufacturer rails can be the difference between resale and parts harvesting.
Clean up the handoff
You don’t need to cosmetically restore everything, but you should make the lot presentable and easy to inspect.
- Consolidate by product family: Keep Cisco with Cisco, Avaya with Avaya, optics with optics.
- Label pallets or cartons clearly: Match labels to your inventory spreadsheet.
- Keep damaged units separate: Don’t bury bad assets inside the good lot.
- Prepare site access details: Dock hours, contact names, freight limitations, and lift-gate needs should be settled in advance.
A clean inventory file and a staged pickup area often do more for deal speed than another round of price negotiation.
Preparation also helps you decide route by route. Some assets should be sold for reuse, some should be harvested for components, and some should go straight to recycling. You’ll make better decisions when the lot is organized before buyers start quoting.
Red Flags to Identify Untrustworthy Telecom Buyers
The highest offer can be the most expensive mistake in the deal.
A major compliance gap still exists in this market. A 2025 Gartner report noted that 68% of enterprises faced regulatory audits for improper IT asset disposition, and a Deloitte survey found only 22% of buyback vendors provide auditable certificates of data destruction, as summarized in this telecom buyback compliance discussion. This is the primary concern with unvetted buyers. They may pay quickly, then leave you with an unprovable chain of custody.
What to watch for immediately
Some warning signs show up in the first call.
- They quote without asking questions: A buyer who doesn’t ask about storage, condition, or included components is pricing loosely.
- They avoid documentation: If certificates are “available on request later,” assume they won’t arrive.
- They push cash deals with thin records: Informal transactions create formal problems during audits.
- They can’t explain downstream handling: You need to know what gets resold, what gets wiped, and what gets recycled.
The subtle red flags
Others are less obvious but just as serious.
A buyer may sound knowledgeable, list familiar telecom brands, and still have no controlled process. Another may promise data wiping but refuse to describe the standard used or the asset-level reporting you’ll receive. Some will offer one blended number for everything because they haven’t evaluated the lot carefully and plan to renegotiate after pickup.
A disciplined review helps. Procurement and IT teams can use a structured vendor due diligence checklist to compare buyers on documentation, security controls, logistics, and downstream transparency before approving any sale.
Buyers who dislike scrutiny usually have a reason for it.
A trustworthy buyer doesn’t just talk about recovery value. They make the entire disposition trail auditable.
Choosing a Partner for Secure Value Recovery
Telecom resale works best when you stop treating it like a one-time cleanout and start treating it like an asset disposition project. The right partner should be able to evaluate mixed telecom lots, handle secure removal, document data destruction, and route each item to resale or recycling without losing chain of custody.
That matters even more in a volatile market. In 2024, worldwide telecom equipment revenue fell 11% year over year, the steepest annual decline in over 20 years, according to Dell’Oro telecom equipment market reporting. In that kind of cycle, pricing swings quickly, surplus volumes rise, and weak buyers often get weaker.
What a reliable partner should provide
Look for a provider that can do all of the following in one controlled process:
- Clear intake and valuation methods
- Secure data destruction options
- Documented chain of custody
- Remarketing for recoverable assets
- Responsible recycling for the rest
For businesses managing larger decommissions, one option is a structured telecom resale and disposition workflow such as telecom equipment liquidation, which combines buyback with compliant downstream handling.
The decision that actually matters
Price still matters. It just can’t be the only filter.
If two buyers are close on value and only one can produce asset-level records, destruction certificates, and a defensible audit trail, that’s the safer and usually smarter transaction. Recovering value from used telecom gear is important. Preventing avoidable security, legal, and environmental exposure is more important.
If your business is ready to sell decommissioned routers, PBX systems, switches, optical gear, or mixed telecom hardware, contact Beyond Surplus for certified electronics recycling and secure IT asset disposal with documented value recovery options.